In a significant escalation of state-sponsored cyber espionage, hackers linked to Russia’s military intelligence units have been found exploiting known vulnerabilities in older Internet routers to surreptitiously harvest authentication tokens from Microsoft Office users on a massive scale. Security experts, including Microsoft and researchers from Lumen’s Black Lotus Labs, issued urgent warnings today, detailing a sophisticated yet remarkably simple spying campaign that allowed the state-backed Russian threat actor, identified as "Forest Blizzard," to silently siphon authentication tokens from users across more than 18,000 networks without deploying any traditional malicious software or code on the targeted devices.
Microsoft, in a comprehensive blog post, revealed that its security teams had identified over 200 organizations and 5,000 consumer devices ensnared in this stealthy network. The operation, attributed to a group also known as APT28 or Fancy Bear, demonstrates a concerning pivot towards exploiting foundational network infrastructure, particularly the often-neglected small office/home office (SOHO) routers, as a primary vector for large-scale data exfiltration.
Understanding Forest Blizzard: A History of State-Sponsored Cyber Operations
Forest Blizzard, a name coined by Microsoft for its observed activity, is a notorious cyber espionage group that has long been a focal point for international intelligence agencies. Widely known by its monikers APT28 (Advanced Persistent Threat 28) and Fancy Bear, the group is unequivocally attributed to the military intelligence units within Russia’s General Staff Main Intelligence Directorate (GRU). This attribution places the current campaign firmly within the context of Russia’s broader geopolitical objectives and its history of leveraging cyber capabilities for strategic advantage.
APT28’s operational history is extensive and impactful, marking it as one of the most prolific and disruptive state-sponsored threat actors globally. The group gained significant international notoriety in 2016 for its audacious compromise of the Hillary Clinton campaign, the Democratic National Committee (DNC), and the Democratic Congressional Campaign Committee (DCCC). These intrusions were a central component of a larger Russian effort to interfere with the U.S. presidential election, highlighting the group’s capacity for political influence operations and its willingness to engage in high-stakes cyber warfare. Their methods often involve sophisticated spear-phishing campaigns, zero-day exploits, and the deployment of custom malware. The group is tracked by the MITRE ATT&CK framework under identifier G0007, which details their tactics, techniques, and procedures (TTPs), emphasizing their focus on intelligence gathering and disruption. The current campaign, while technically distinct in its execution, aligns perfectly with their overarching mission of collecting sensitive information from government entities, political organizations, and critical infrastructure targets.
The Stealthy Mechanism: DNS Hijacking and Adversary-in-the-Middle Attacks
The genius and concern of Forest Blizzard’s latest campaign lie in its elegant simplicity and the scale of its impact. Researchers at Black Lotus Labs, the security division of the Internet backbone provider Lumen, were instrumental in uncovering the breadth of this operation. They observed that at its peak in December 2025, Forest Blizzard’s surveillance dragnet had compromised more than 18,000 Internet routers. The vast majority of these devices were identified as unsupported, end-of-life models, or severely outdated on security updates, primarily older Mikrotik and TP-Link devices commonly found in the SOHO market. This demographic of vulnerable devices proved to be a fertile ground for the GRU hackers.
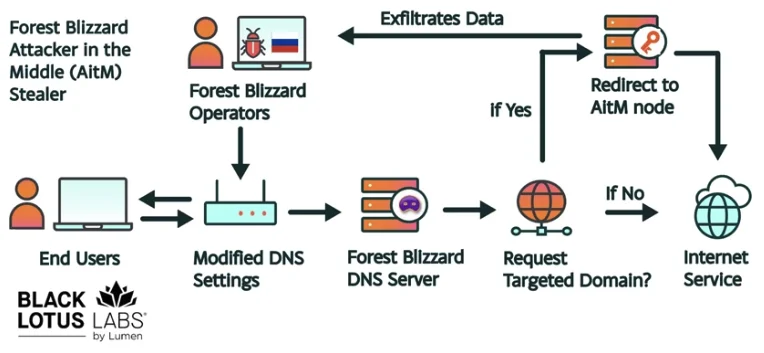
Ryan English, a Security Engineer at Black Lotus Labs, underscored that the GRU hackers did not need to install any complex malware on the targeted routers. Instead, they leveraged known vulnerabilities in these older devices to modify their Domain Name System (DNS) settings. DNS, often referred to as the "phonebook of the internet," is the critical service that translates human-readable domain names (like microsoft.com) into machine-readable IP addresses. In a DNS hijacking attack, bad actors interfere with this fundamental process, redirecting users to malicious servers without their knowledge.
In this specific campaign, the compromised routers were reconfigured to use DNS servers controlled by the attackers. As a result, any device connected to the local network of a hijacked router would then receive DNS queries from the attacker-controlled servers. This enabled the attackers to propagate their malicious DNS settings to all users on that local network. From this point forward, the attackers could intercept OAuth authentication tokens transmitted by those users.
Microsoft refers to this activity as using DNS hijacking "to support post-compromise adversary-in-the-middle (AiTM) attacks on Transport Layer Security (TLS) connections against Microsoft Outlook on the web domains." The significance of intercepting OAuth tokens cannot be overstated. These tokens are typically generated and transmitted after a user has successfully logged in and completed any multi-factor authentication (MFA) processes. By capturing these tokens, the attackers could gain direct, persistent access to victim accounts, effectively bypassing the need to phish for credentials or one-time MFA codes. This method provides an incredibly efficient and stealthy way to maintain access to accounts, particularly those protected by robust security measures. As Ryan English aptly put it, "Everyone is looking for some sophisticated malware to drop something on your mobile devices or something. These guys didn’t use malware. They did this in an old-school, graybeard way that isn’t really sexy but it gets the job done."
Chronology of the Campaign and Tactical Evolution
The timeline of Forest Blizzard’s activities reveals a group that is highly adaptive and responsive to disclosures from the cybersecurity community. While the peak of the mass DNS hijacking campaign was observed in December 2025, the roots of this tactical shift can be traced back earlier.
In August 2025, the U.K.’s National Cyber Security Centre (NCSC) released a detailed report (PDF) titled "Authentic Antics," which highlighted Forest Blizzard’s use of malware to control a more targeted and smaller group of compromised routers. This report provided crucial insights into the group’s then-current modus operandi. However, as Danny Adamitis, another engineer at Black Lotus Labs, observed, the NCSC’s public disclosure acted as a catalyst for a significant tactical pivot.

"Before the last NCSC report came out they used this capability in very limited instances," Adamitis told KrebsOnSecurity. "After the report was released they implemented the capability in a more systemic fashion and used it to target everything that was vulnerable." This illustrates the cat-and-mouse game inherent in cybersecurity: public disclosures, while vital for awareness and defense, can also prompt sophisticated adversaries to evolve their methods rapidly. Forest Blizzard quickly ditched its malware-centric approach in favor of mass-altering DNS settings on thousands of vulnerable routers, demonstrating a capacity for rapid retooling and scaling its operations.
The current wave of disclosures, including Microsoft’s blog post and Lumen’s Black Lotus Labs report on April 7, 2026, along with a new NCSC advisory detailing how Russian cyber actors have been compromising routers, brings this widespread DNS hijacking campaign into the public eye. These coordinated disclosures aim to alert potential victims and prompt remedial actions across the internet.
Targets and Impact: Government Agencies and Critical Infrastructure
The choice of targets for Forest Blizzard’s campaign underscores its intelligence-gathering objectives. Lumen’s report indicates that the hackers primarily targeted government agencies, including ministries of foreign affairs, law enforcement bodies, and third-party email providers. This selection aligns perfectly with the GRU’s mandate for state-level espionage, seeking to acquire sensitive information, compromise communications, and potentially lay groundwork for future disruptive operations. The scale of 18,000 compromised networks suggests a broad dragnet, but the focus on specific organizational types points to a strategic targeting effort rather than indiscriminate attacks.
The impact of such an operation extends beyond immediate data theft. The sustained access provided by stolen OAuth tokens could allow adversaries to monitor communications, exfiltrate documents, and gain deeper footholds into targeted networks. For government agencies, the compromise of email accounts can lead to the exposure of classified information, diplomatic communications, and operational plans, posing significant national security risks. For law enforcement, it could expose ongoing investigations or sensitive data on citizens.
Broader Implications and Official Responses
This campaign brings to the forefront several critical cybersecurity challenges, prompting responses and warnings from various official bodies.
The Pervasive Vulnerability of SOHO Devices: The success of Forest Blizzard’s "old-school" approach highlights a persistent and often underestimated weak link in the global cybersecurity chain: consumer-grade and older SOHO network infrastructure. These devices are frequently deployed with default configurations, receive infrequent or no security updates, and are often overlooked in enterprise security strategies. They represent a significant attack surface that sophisticated state-sponsored actors are increasingly exploiting. The fact that many of the exploited devices were end-of-life or unsupported emphasizes the critical need for individuals and organizations, especially small businesses, to regularly update their network hardware and replace obsolete equipment.
Supply Chain Security and Regulatory Action: The vulnerabilities exploited by Forest Blizzard resonate strongly with recent regulatory actions concerning the security of network hardware. On March 23, the U.S. Federal Communications Commission (FCC) announced a significant policy shift, stating it would no longer certify consumer-grade Internet routers produced outside of the United States without special conditional approval. This broader approach, which followed earlier discussions about specific bans (such as TP-Link), was driven by concerns that foreign-made routers pose "a severe cybersecurity risk that could be leveraged to immediately and severely disrupt U.S. critical infrastructure and directly harm U.S. persons."
While the FCC’s policy aims to mitigate future risks, it has sparked debate about its practical implications, with experts noting that few new consumer-grade routers would be available for purchase under this stringent policy (besides potentially those from domestic manufacturers like SpaceX’s Starlink, produced in Texas). The new policy requires router makers to apply for a "conditional approval" from the Department of War or Department of Homeland Security and does not retroactively affect previously purchased routers. However, the Forest Blizzard campaign serves as a stark validation of the FCC’s underlying concerns, demonstrating precisely how poorly secured routers, regardless of their origin, can be weaponized by state adversaries to compromise critical data and potentially disrupt services.
The Evolving Landscape of Cyber Espionage: Microsoft’s observation that this is the first time Forest Blizzard has used "DNS hijacking at scale to support AiTM of TLS connections after exploiting edge devices" signals an evolution in state-sponsored tactics. Adversaries are constantly innovating, often finding new ways to weaponize existing flaws or combining simple techniques in novel ways to achieve their objectives. The move away from complex malware, in this instance, suggests a strategic decision to maximize reach and stealth while minimizing the risk of detection through traditional endpoint security solutions.
Recommendations for Defense: In light of these disclosures, cybersecurity experts and agencies are reiterating crucial defensive measures:
- Router Updates and Replacement: Users and organizations must prioritize updating their router firmware. For end-of-life devices, immediate replacement with actively supported and patched hardware is essential.
- DNS Monitoring: Organizations should implement robust monitoring of their DNS settings and traffic for any unauthorized changes or suspicious queries.
- MFA Implementation: While tokens were bypassed post-MFA, strong multi-factor authentication remains a critical baseline defense against credential theft in general.
- Network Segmentation: Segmenting networks can limit the lateral movement and impact of a compromise if a router is indeed hijacked.
- Awareness and Education: Users need to be educated about the risks associated with outdated hardware and the importance of cybersecurity hygiene.
The Forest Blizzard campaign serves as a potent reminder that the battle against state-sponsored cyber threats is ongoing and requires continuous vigilance, adaptation, and investment in foundational security practices. As adversaries continue to innovate, even "old-school" methods, when executed with precision and scale, can pose significant threats to national security and global digital infrastructure. The international cybersecurity community will undoubtedly be watching closely to see how Forest Blizzard adapts its tactics in the wake of these latest public disclosures.