A sophisticated and financially motivated cybercrime collective, known as TeamPCP, has intensified its operations by deploying a destructive data-wiping worm specifically engineered to target systems within Iran. This alarming development, which materialized over the past weekend, marks a significant escalation in the group’s tactics, as it leverages poorly secured cloud services to spread its malicious payload. The worm, identified by security researchers, is designed to obliterate data on infected systems that are configured with Iran’s time zone or have Farsi set as the default language, injecting a potentially disruptive element into an already volatile geopolitical landscape, despite the group’s primary financial objectives.
TeamPCP’s Modus Operandi: A Cloud-Native Threat
TeamPCP, a relatively new entrant in the cybercrime arena, has rapidly distinguished itself through its focus on compromising corporate cloud environments. Their methodology primarily involves weaponizing exposed control planes rather than relying on traditional endpoint exploitation. This cloud-native approach targets critical infrastructure components such as exposed Docker APIs, Kubernetes clusters, Redis servers, and the React2Shell vulnerability. Since December 2025, the group has been observed deploying a self-propagating worm to infiltrate these environments, subsequently moving laterally within victim networks to siphon authentication credentials and extort organizations, typically communicating demands via Telegram.
The security firm Flare, which published a detailed profile of TeamPCP in January, highlighted the group’s strategic preference for cloud infrastructure. Their analysis revealed that Azure and AWS collectively accounted for a staggering 97% of compromised servers, with Azure alone representing 61% and AWS 36%. Assaf Morag of Flare emphasized that TeamPCP’s formidable strength does not stem from pioneering novel exploits or developing original malware. Instead, their success lies in the large-scale automation and seamless integration of well-known attack techniques. Morag elaborated that the group "industrializes existing vulnerabilities, misconfigurations, and recycled tooling into a cloud-native exploitation platform that turns exposed infrastructure into a self-propagating criminal ecosystem." This approach allows them to achieve widespread impact efficiently, leveraging readily available weaknesses across vast swathes of internet-facing cloud services.
A Chronology of Attacks: From Extortion to Wiper
The emergence of the Iran-targeting wiper campaign is the latest chapter in TeamPCP’s evolving playbook, following a clear timeline of escalating aggression and technical sophistication:
- December 2025: TeamPCP is first observed initiating its campaign of compromising corporate cloud environments. Their self-propagating worm begins actively seeking out and exploiting vulnerabilities in Docker APIs, Kubernetes clusters, Redis servers, and the React2Shell vulnerability. This period marks the establishment of their foundational infrastructure for credential theft and extortion.
- January 2026: Security firm Flare publishes an in-depth profile of TeamPCP, detailing their unique cloud-centric attack strategies and their reliance on automation rather than zero-day exploits. This report serves as an early warning to the cybersecurity community about the group’s growing threat.
- Late February 2026: While not directly attributed to TeamPCP, the vulnerability scanner Trivy from Aqua Security experiences a major supply chain attack as part of an automated threat dubbed "HackerBot-Claw." This incident, which exploited misconfigured workflows in GitHub Actions to steal authentication tokens, provided a crucial precedent and context for subsequent attacks on development tools, highlighting a growing systemic weakness in the software supply chain.
- March 19, 2026: TeamPCP executes a direct supply chain attack against Trivy. The group successfully injects credential-stealing malware into official releases distributed through GitHub Actions. Aqua Security promptly removed the harmful files, but not before malicious versions were published, enabling attackers to "snarf" sensitive data including SSH keys, cloud credentials, Kubernetes tokens, and cryptocurrency wallets from unsuspecting users, as reported by Wiz.
- "This past weekend" (approximately March 22-23, 2026): Leveraging the same technical infrastructure and access points gained from the Trivy supply chain compromise, TeamPCP deploys a new and highly destructive payload. This payload specifically targets systems within Iran, executing a wiper attack if the user’s timezone or locale settings correspond to the country. This marks a pivot from pure financial extortion to targeted data destruction.
- March 23, 2026 (Update): In a rapidly unfolding series of events, Wiz reports that TeamPCP also successfully pushed credential-stealing malware to the KICS vulnerability scanner from Checkmarx. The KICS GitHub Action was compromised for several hours between 12:58 and 16:50 UTC, further underscoring the group’s persistent targeting of development and security tools within the software supply chain.
This chronological progression demonstrates TeamPCP’s ability to evolve its tactics, moving from broad cloud compromise and extortion to highly targeted and destructive operations, often by exploiting the trust inherent in the software development ecosystem.
The "CanisterWorm" and Its Destructive Payload
At the heart of TeamPCP’s Iran-targeting operation is a malicious payload that security researchers at Aikido have dubbed "CanisterWorm." The name derives from the group’s unique method of orchestrating their campaigns using an Internet Computer Protocol (ICP) canister. ICP canisters are essentially tamperproof, blockchain-based "smart contracts" that encapsulate both code and data. Their distributed architecture makes them inherently resistant to takedown attempts, remaining reachable as long as their operators continue to pay virtual currency fees to keep them online. This infrastructure provides TeamPCP with a robust and resilient command-and-control mechanism, making their operations particularly difficult to disrupt.
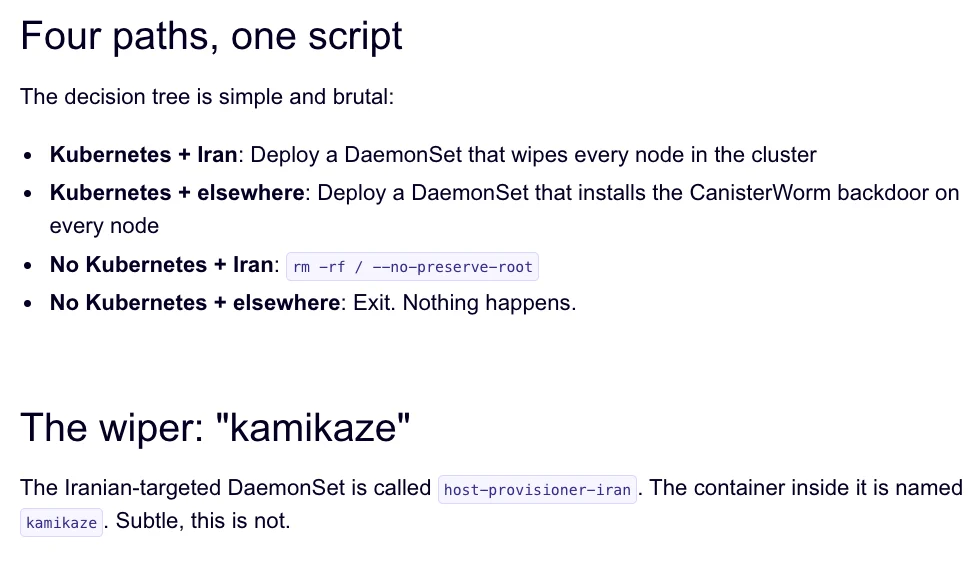
Charlie Eriksen, a security researcher at Aikido, provided critical insights into the CanisterWorm’s functionality. According to Eriksen’s analysis, published in a blog post on Sunday, the wiper component of the payload is highly conditional. It first performs a geographical and linguistic check, detecting if the victim system is located in Iran by examining its timezone or default language settings (Farsi). If these conditions are met, the worm then ascertains if the compromised system has access to a Kubernetes cluster. Should a Kubernetes cluster be detected, the CanisterWorm unleashes its full destructive capability, systematically destroying data on every node within that cluster. In scenarios where a Kubernetes cluster is not present, Eriksen confirmed that the malware will still proceed to wipe data, albeit confined to the local machine. This nuanced targeting mechanism indicates a calculated effort to maximize disruption within specific Iranian IT environments, particularly those leveraging cloud-native container orchestration. The technical details reveal a sophisticated understanding of cloud infrastructure and a precise execution strategy tailored for impact.
The Shadowy World of TeamPCP’s Communication and Tactics
Beyond their technical prowess, TeamPCP exhibits a distinctive operational style, characterized by overt bragging and an almost theatrical display of their capabilities. Members of the group are reportedly boasting about their exploits in a dedicated Telegram group, claiming to have stolen vast quantities of sensitive data from numerous major corporations, including a prominent multinational pharmaceutical firm. This public posturing serves multiple purposes: it likely boosts morale within the group, attracts new recruits, and acts as a psychological weapon against their victims and the broader cybersecurity community.
Further illustrating their unconventional tactics, Eriksen noted that after compromising Aqua Security a second time, TeamPCP gained access to numerous GitHub accounts. They then proceeded to spam these accounts with "junk messages," a move Eriksen described as "almost like they were just showing off how much access they had." This behavior suggests that the group possesses a substantial cache of stolen credentials, with the publicly observed actions likely representing only a fraction of their total illicit gains.

Security experts, including Catalin Cimpanu of Risky Business, have observed similar tactics in the context of supply chain attacks. In his newsletter "GitHub is Starting to Have a Real Malware Problem," Cimpanu explained that attackers frequently push meaningless commits to their repositories or utilize online services that sell GitHub stars and "likes." The objective of these seemingly innocuous actions is to manipulate GitHub’s search algorithms, ensuring that malicious packages remain prominently displayed at the top of search results, thereby increasing the likelihood of unwitting downloads and further compromise. The transient nature of the malicious payload, which Eriksen observed being rapidly deployed and withdrawn, and even occasionally redirecting visitors to a "Rick Roll" video on YouTube, further underscores the group’s "Chaotic Evil" persona. This erratic behavior, oscillating between serious cybercrime and playful trolling, suggests that while financial gain is a primary driver, TeamPCP also derives satisfaction from causing disruption and garnering attention, blurring the lines between traditional cybercriminals and hacktivists.
Escalating Supply Chain Risks: A Broader Problem
The recent series of attacks attributed to TeamPCP, particularly those targeting vulnerability scanners like Trivy and KICS, starkly highlight a rapidly escalating crisis within the software supply chain. The incident involving Trivy this past weekend was, notably, the second major supply chain compromise for the scanner in as many months. In late February, Trivy was also impacted by "HackerBot-Claw," an automated threat that broadly exploited misconfigured workflows in GitHub Actions to pilfer authentication tokens. This pattern underscores a systemic vulnerability within the interconnected ecosystem of modern software development, where a single weak link can expose an entire chain of users and organizations.
The implications of such attacks are profound. By injecting malware into widely used development tools and open-source projects, threat actors can bypass traditional perimeter defenses and gain access to a multitude of downstream targets. This "trust exploitation" is incredibly efficient for attackers, as they leverage the inherent trust developers place in their tools and libraries. Catalin Cimpanu’s reporting for Risky Business aptly captures the gravity of the situation, observing a significant increase in the frequency of supply chain attacks since 2024. He posits that threat actors are increasingly recognizing the immense efficiency and reach these attack vectors offer.
Cimpanu’s analysis also raises critical questions about the responsibility of platform providers. While security firms like Aikido, Flare, Wiz, and Aqua Security are demonstrating commendable efforts in spotting and responding to these incidents, the sheer volume and complexity of attacks suggest a need for broader systemic improvements. Cimpanu explicitly calls for GitHub’s security team to "step up" their efforts. However, he acknowledges the formidable engineering challenge this presents: "on a platform designed to copy (fork) a project and create new versions of it (clones), spotting malicious additions to clones of legitimate repos might be quite the engineering problem to fix." The distributed and collaborative nature of platforms like GitHub, while fostering innovation, also creates an expansive attack surface that is difficult to monitor comprehensively, making it an ideal hunting ground for groups like TeamPCP.
Expert Perspectives and Industry Reactions
The cybersecurity community has reacted swiftly to TeamPCP’s latest actions, offering both technical analysis and calls for enhanced vigilance. Charlie Eriksen of Aikido, whose team was instrumental in identifying the CanisterWorm, has provided crucial insights into the group’s dynamic nature. He noted the rapid deployment and withdrawal of the malicious code, coupled with its shifting functionalities, indicating an agile and experimental operational style. Eriksen also mused on the "Iran thing" potentially being a deliberate tactic to garner attention, suggesting a complex motivation beyond pure financial gain, leaning towards a "Chaotic Evil" persona. This assessment highlights the challenge in predicting the next moves of such groups, as their actions may not always align with purely rational economic incentives.
Assaf Morag from Flare reinforced the understanding of TeamPCP’s strength residing in the industrialization of existing vulnerabilities rather than the discovery of new ones. This perspective underscores the importance of basic cyber hygiene, patch management, and secure configuration as primary defenses against this specific threat actor. The consistent targeting of common cloud misconfigurations and known vulnerabilities means that many attacks could potentially be thwarted with diligent security practices.
Official responses from affected parties, while not always publicly detailed, reflect the urgency of the situation. Aqua Security, for instance, immediately removed the harmful files from Trivy’s GitHub releases, demonstrating rapid incident response. Wiz’s prompt reporting of both the Trivy and KICS compromises provided timely warnings to the wider community, enabling other users to assess their exposure. The implied call for GitHub to "step up" their security efforts, as articulated by Cimpanu, resonates with a growing sentiment within the industry that platform providers must bear a greater share of the burden in securing their ecosystems against these pervasive supply chain threats. This necessitates not only reactive measures but also proactive engineering solutions to identify and neutralize malicious content at scale.
The Geopolitical Undercurrents and Future Implications
The deliberate targeting of systems within Iran by a financially motivated group introduces a complex geopolitical undercurrent to TeamPCP’s activities. While Eriksen speculates that the Iran-specific wiper payload could be an attention-seeking stunt or an expression of "chaotic evil," the reality is that any cyberattack with geographical or linguistic targeting can have broader implications. In a region already fraught with tensions, even financially motivated cyber incidents can be misconstrued, attributed to state-sponsored actors, or leveraged in broader narratives, potentially contributing to cyber escalation. The distinction between financially driven cybercrime and state-sponsored espionage or sabotage often blurs, especially when the targets align with geopolitical interests.
Looking ahead, TeamPCP’s actions serve as a stark reminder of the evolving landscape of cloud security threats. The industrialization of exploitation, the focus on cloud-native infrastructure, and the exploitation of the software supply chain represent critical challenges for organizations worldwide. The resilience of ICP canisters as a command-and-control mechanism further complicates defensive efforts, necessitating innovative approaches to threat intelligence and disruption. The growing frequency of supply chain attacks, as noted by Cimpanu, signals a persistent and likely escalating trend. Organizations must therefore prioritize robust supply chain security measures, including rigorous vetting of third-party software, continuous monitoring of development pipelines, and implementing strong authentication and access control policies across their cloud environments. The dual nature of threat actors like TeamPCP – driven by both financial gain and a penchant for disruptive "chaos" – suggests that the cybersecurity community must prepare for increasingly unpredictable and impactful attacks in the future.
Conclusion: A Persistent and Evolving Threat
TeamPCP represents a modern archetype of cybercriminality, adept at leveraging automation, existing vulnerabilities, and the interconnectedness of cloud infrastructure to achieve their objectives. Their recent deployment of the Iran-targeting CanisterWorm, coupled with their consistent exploitation of software supply chains through platforms like GitHub, underscores a significant and evolving threat. The group’s blend of financial motivation with seemingly "chaotic evil" tendencies makes them particularly unpredictable and challenging to counter. As the digital landscape continues to expand and become more integrated, the onus falls not only on individual organizations to bolster their defenses but also on platform providers and the broader cybersecurity community to collaborate on systemic solutions. The battle against sophisticated, cloud-native threats like TeamPCP will require continuous innovation, proactive threat intelligence, and a collective commitment to securing the foundational elements of our digital world.