The Kraken cryptocurrency exchange has revealed it is currently the target of an extortion attempt by a cybercrime group threatening to disseminate videos purportedly showing access to its internal systems that host client data. The incident, confirmed by Kraken’s Chief Security Officer, Nick Percoco, underscores the persistent and evolving threat landscape facing the digital asset industry, particularly concerning insider vulnerabilities. Percoco explicitly stated that while the company is under duress, client funds were never compromised, and the security breach involved limited improper access to customer support data by two internal employees. Kraken has adopted a firm stance, refusing to pay any ransom or engage in negotiations with the perpetrators, and is actively pursuing legal action in collaboration with federal law enforcement agencies.
Unpacking the Extortion Attempt and Insider Threat
According to Kraken’s official statements, the extortion plot centers around a criminal group’s claim to possess video evidence of access to the exchange’s internal infrastructure. These videos, the criminals allege, demonstrate sensitive interactions with client data, which they threaten to release publicly unless their demands are met. This type of threat leverages fear of reputational damage and regulatory scrutiny, common tactics in modern cyber extortion campaigns.
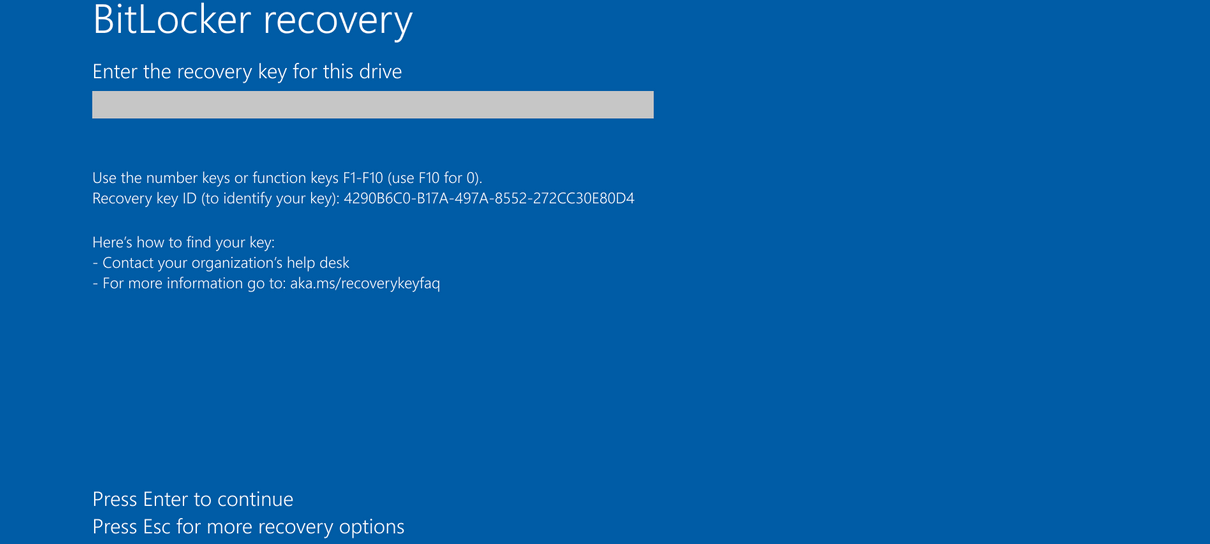
Percoco was quick to reassure Kraken’s vast user base, which spans millions of individuals across 190 countries, that the integrity of their funds remains uncompromised. He emphasized, "Our systems were never breached; funds were never at risk; we will not pay these criminals; we will not ever negotiate with bad actors." This resolute declaration aims to project strength and stability in the face of a sophisticated attack. The incident, as described, is not a traditional external hack but rather an "insider threat," a category of cyber risk that is increasingly challenging for organizations across all sectors. In Kraken’s case, it involved two instances of unauthorized access to a limited scope of customer data by support employees, who were reportedly recruited by the external threat actors.
The exposed information, affecting approximately 2,000 accounts—a mere 0.02% of Kraken’s extensive user base—was restricted to client support data. This type of information typically includes details exchanged during customer service interactions, which, while not directly financial, can still be valuable to criminals for phishing, social engineering, or identity theft.
A Detailed Chronology of Events
The current extortion attempt is not an isolated incident but rather the culmination of a series of events that began more than a year prior, highlighting the long-term nature of some sophisticated cyber campaigns.

The initial alarm was raised in February 2025, when Kraken received a "tip from a trusted source." This intelligence indicated that cybercriminals were circulating a video that seemingly demonstrated unauthorized access to Kraken’s client support systems. This initial tip-off prompted an immediate and thorough internal investigation by Kraken’s security teams. The investigation quickly uncovered that a support employee had been compromised, having been "recruited by the threat actor" to facilitate this unauthorized access.
Kraken responded swiftly and decisively to this first incident. The company immediately revoked the compromised employee’s access privileges to all internal systems, effectively severing the illicit connection. Concurrently, a comprehensive forensic investigation was launched to ascertain the full scope of the breach, identify any exposed data, and understand the methods used by the threat actor. In parallel, Kraken implemented enhanced security controls and protocols to prevent similar occurrences. Crucially, where user exposure was identified, the company took proactive steps to notify affected users directly, adhering to best practices for data breach disclosure and transparency.
More recently, Kraken received another tip, this time concerning a more current video that again purported to show insider access to the company’s systems. This second notification indicated a continued or renewed effort by the threat actors to penetrate Kraken’s internal operations, possibly leveraging different individuals or refined tactics. Similar to the first incident, Kraken’s response was immediate: the employee linked to this more recent video had their access revoked, a new investigation was launched, and further strengthening of security controls was undertaken. Again, affected users were notified directly as a matter of policy and regulatory compliance.
It is against this backdrop of repeated attempts at insider infiltration that the current extortion attempt has materialized. The criminal group is now attempting to capitalize on the compromised information and system access demonstrated in these videos, leveraging them as blackmail material to extract concessions from Kraken.
Kraken’s Standing and the Broader Cryptocurrency Landscape
Kraken stands as a formidable entity in the global cryptocurrency market. Founded in 2011, it is a U.S.-based exchange recognized as one of the largest and most established platforms for buying, selling, and trading digital assets. Its services extend to millions of users across 190 countries, offering access to a diverse portfolio of over 200 cryptocurrencies, including market leaders like Bitcoin and Ethereum. The exchange boasts a daily trading volume that frequently runs into hundreds of millions of U.S. dollars, cementing its position as a critical piece of the global digital finance infrastructure. Such prominence naturally makes Kraken a high-value target for cybercriminals.
The cryptocurrency industry as a whole has, unfortunately, been a fertile ground for cybercrime. Its rapid growth, the decentralized and often pseudonymous nature of transactions, and the immense financial value concentrated in exchanges make it uniquely attractive to malicious actors. While the underlying blockchain technology is inherently secure, the centralized points of interaction – the exchanges – are often the weakest links. These platforms require robust cybersecurity frameworks that extend beyond typical enterprise security to address unique threats, including sophisticated social engineering and insider recruitment tactics.
The Pervasive Threat of Insiders and Recruitment

The Kraken incident starkly highlights the escalating challenge of insider threats. An insider threat refers to a security risk that originates from within the targeted organization. This can involve current or former employees, contractors, or business associates who have legitimate access to the organization’s systems and data. The motives for insider threats are varied, ranging from financial gain (as appears to be the case with Kraken), to espionage, sabotage, or even simply negligence.
What makes the Kraken situation particularly insidious is the element of "malicious recruitment." This refers to external threat actors actively seeking out and compromising individuals within an organization to gain access to sensitive systems. These recruitment efforts can be highly sophisticated, involving financial incentives, coercion, or exploitation of personal vulnerabilities. Once recruited, an insider can bypass many of the traditional perimeter defenses that protect against external attacks, making detection and mitigation significantly more challenging. Reports from various cybersecurity firms consistently indicate a rise in insider-related incidents, with a significant percentage attributed to financially motivated actors. The average cost of an insider incident can be substantial, encompassing detection and escalation, notification, lost business, and reputational damage.
Industry Parallels and Lessons Learned
The Kraken incident is not an isolated event but rather indicative of a broader problem impacting multiple industries, and particularly the cryptocurrency sector. A notable parallel can be drawn with another major American cryptocurrency exchange, Coinbase, which suffered a significant data breach in mid-2025. In that instance, hackers successfully bribed employees of an India-based customer support agency to disclose private client support information. That incident impacted a staggering 70,000 customers, with Coinbase estimating the total financial damages to be around $400 million.
While the specifics differ—Kraken’s insider recruitment appears to have been directly within its support staff, whereas Coinbase involved third-party contractors—the core vulnerability remains the same: the human element in customer support operations. Customer support agents, by the nature of their role, often have access to a wide array of user information, making them prime targets for social engineering and recruitment by criminal enterprises. These incidents underscore the critical importance of rigorous background checks, continuous security awareness training, strict access controls, and robust monitoring for anomalous behavior within customer support teams, whether internal or outsourced. The financial impact of the Coinbase breach serves as a stark warning of the potential costs associated with such vulnerabilities, even when direct funds are not immediately stolen.
Beyond these two prominent examples, the cryptocurrency industry has been plagued by numerous other security incidents, many of which involve some form of human weakness or social engineering. While not all are direct insider threats, they collectively highlight the immense pressure on exchanges to secure not just their technological infrastructure but also their human capital against increasingly sophisticated and persistent adversaries.
Official Responses and Legal Pursuits
Kraken’s Chief Security Officer, Nick Percoco, has been unequivocal in the company’s stance: "We will not pay these criminals; we will not ever negotiate with bad actors." This firm position is not merely a declaration but a strategic decision aimed at deterring future extortion attempts and reinforcing the message that capitulation only emboldens cybercriminals. Many cybersecurity experts and law enforcement agencies advocate against paying ransoms, as it provides funding for criminal operations and does not guarantee the return or non-release of data.
.png)
Crucially, Kraken is not merely fending off the extortion but is actively pursuing legal remedies. The company stated that its investigation has yielded "enough evidence to legally prosecute all involved individuals attempting to blackmail them." This proactive legal strategy involves close collaboration with "federal law enforcement across multiple jurisdictions." The multi-jurisdictional nature of this cooperation is vital, given that cybercrime often transcends national borders, involving actors located in different countries and impacting victims globally. Law enforcement agencies, including the FBI and other international bodies, possess specialized units dedicated to combating cybercrime and can leverage international treaties and agreements to track, apprehend, and prosecute individuals involved in such schemes. This collaborative approach is essential for effective deterrence and justice in the digital realm.
Broader Implications and Future Outlook
The Kraken incident carries significant implications for the exchange itself, its users, and the wider cryptocurrency industry. For Kraken, while funds are secure, the incident inevitably impacts trust and reputation. Even minor data exposures can lead to user apprehension, potentially affecting user acquisition and retention. The company will likely face enhanced scrutiny from regulatory bodies, who are increasingly focused on cybersecurity resilience and consumer protection in the volatile crypto market. This might necessitate further investment in advanced threat detection systems, more stringent employee vetting processes, and continuous internal audits to fortify its defenses against evolving insider threats.
For Kraken’s users, the primary reassurance is that their funds remain safe. However, the exposure of client support data, even for a small subset, underscores the ongoing need for vigilance. Users are constantly reminded to employ strong, unique passwords, enable two-factor authentication (2FA) on all their accounts, and be highly suspicious of unsolicited communications that might be phishing attempts leveraging compromised personal data.
For the cryptocurrency industry, this incident serves as another potent reminder that the human element remains a critical vulnerability. It reinforces the need for exchanges to adopt a "zero-trust" security model internally, where no user or device is inherently trusted, regardless of their position or location. This includes implementing robust privileged access management (PAM) solutions, behavior analytics to detect unusual employee activity, and comprehensive, ongoing security awareness training programs that specifically address social engineering tactics and the dangers of insider recruitment. The industry may see increased collaboration on threat intelligence sharing and the development of collective best practices to counter these sophisticated attacks.
In the long term, incidents like Kraken’s will likely contribute to a maturation of cybersecurity practices within the crypto sector. As digital assets become more integrated into mainstream finance, the pressure from regulators, institutional investors, and retail users for ironclad security will only intensify. This will drive innovation in security technologies, greater adoption of advanced AI-driven anomaly detection, and a fundamental shift towards a security culture that prioritizes both technological and human defenses. The fight against cybercrime is a continuous arms race, and every incident, while challenging, offers crucial lessons for building a more secure digital future.