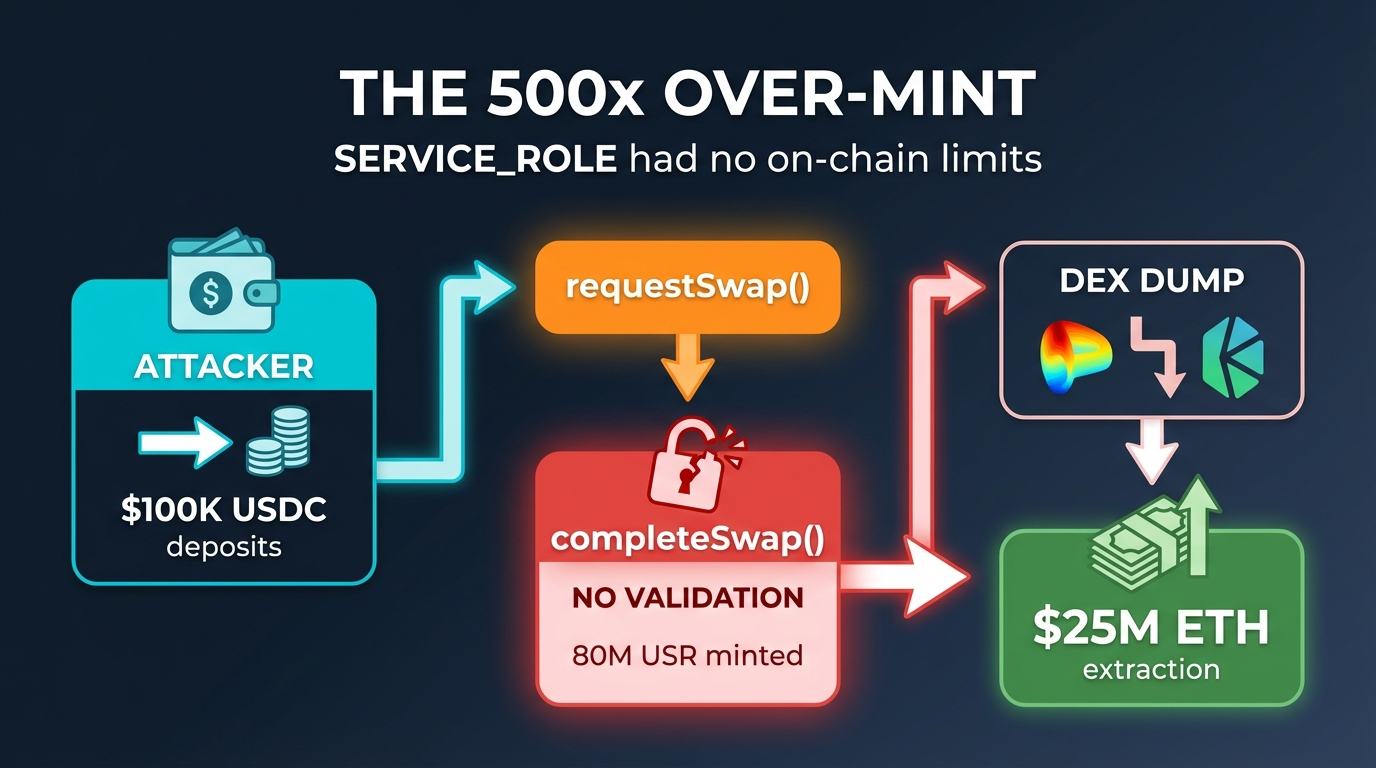
At 2:21 AM UTC on a quiet Sunday morning, March 22, 2026, the decentralized finance (DeFi) ecosystem was rocked by a sophisticated yet fundamentally simple exploit that saw an attacker convert an initial deposit of approximately $100,000 in USDC into roughly $25 million in extracted value. The incident targeted Resolv Labs’ USR stablecoin, leveraging a critical vulnerability within its minting function. The fallout swiftly spread across various DeFi protocols, impacting lending vaults, decentralized exchange (DEX) liquidity pools, and significantly eroding the confidence of investors in newer, complex stablecoin designs. This event has not only resulted in substantial financial losses but has also ignited uncomfortable questions about operational security, audit efficacy, and the inherent risks of deep protocol integrations within DeFi.
The exploit unfolded rapidly, demonstrating the attacker’s keen understanding of the system’s weak points and the lightning-fast execution required to capitalize on them before the wider market could react. What transpired was a textbook example of how a single, overlooked design flaw in a core mechanism can cascade into a multi-million dollar disaster, underscoring the perpetual tension between innovation and security in the fast-paced world of blockchain.
Understanding Resolv Labs and the USR Stablecoin
Resolv Labs had positioned itself as a prominent player in the stablecoin arena with its USR token, designed to maintain a dollar peg through an intricate delta-neutral strategy. This advanced approach aimed to collateralize USR with a diverse basket of assets, including ETH, staked ETH, and Bitcoin, while simultaneously hedging out directional price risks using perpetual futures. The goal was to offer a stablecoin that combined the security of overcollateralization with capital efficiency, a holy grail for many DeFi projects.
Complementing USR, Resolv introduced RLP (Resolv Liquidity Pool) tokens, serving as a junior tranche. RLP was engineered to act as a shock absorber, designed to bear initial losses and protect USR holders from potential depegs or market volatility. This two-token model, while complex, was intended to instill greater confidence in USR’s stability.
At its zenith, Resolv Labs commanded an impressive Total Value Locked (TVL) exceeding $500 million, a testament to its initial success and investor appeal. The project had garnered significant institutional backing, raising $10 million in seed funding from reputable names such as Coinbase Ventures, Maven 11, and Animoca Brands. Its integration into key DeFi protocols like Morpho, Aave, Euler, and Curve further cemented its status as a widely adopted and seemingly robust stablecoin solution. The protocol’s commitment to security appeared strong on paper, having undergone multiple audits and partnered with Hypernative for real-time threat monitoring, in addition to running an Immunefi bug bounty program.
The Pre-Exploit Warning Signs: A Troubling Decline
Despite its initial success and seemingly robust architecture, Resolv Labs was already showing signs of strain even before the exploit. The protocol’s TVL and USR market capitalization had been bleeding significantly in the weeks leading up to March 22. From an approximate $400 million in early February, USR’s market cap plummeted to around $100 million just weeks before the attack—a staggering 75% contraction.
This rapid decline raised uncomfortable questions. Was it a natural consequence of the notoriously fickle yield farming capital moving to greener pastures, especially after Resolv’s points program had concluded? Or did it hint at something more ominous, perhaps insiders quietly unwinding positions, sensing underlying vulnerabilities, or reacting to undisclosed issues? While no definitive answers have emerged, the scale and timing of this capital flight retrospectively appear as a significant, albeit unheeded, red flag, suggesting a potential loss of confidence or an early indicator of systemic weakness.
Anatomy of the Exploit: The 500x Over-Mint
The heart of the exploit lay in a critical design flaw within Resolv’s two-step minting process: requestSwap() followed by completeSwap(). This seemingly standard mechanism, intended to manage the creation of new USR tokens, harbored a fatal vulnerability.
Under normal operating conditions, a user would initiate a deposit of USDC via the requestSwap() function, thereby creating a pending mint request. Subsequently, a privileged off-chain signer, designated as the SERVICE_ROLE, would invoke completeSwap() to finalize the transaction, issuing USR tokens in direct proportion to the deposited amount—ideally, one dollar in, one USR out.
The catastrophic flaw was the absence of on-chain guardrails to enforce this 1:1 ratio. The SERVICE_ROLE possessed the unrestricted ability to pass any desired mint amount to completeSwap(), and the contract would simply execute the command without validation. Crucially, there were no maximum mint limits, no price-oracle checks to verify the value of the collateral against the minted amount, and no bounds validation to ensure consistency between the initial request and its completion. On-chain researchers, such as @andrewhong5297, quickly highlighted a critical architectural oversight: the SERVICE_ROLE, which held the power to mint arbitrary amounts of USR, was controlled by a plain externally owned address (EOA), not a more secure multisignature wallet. While the protocol’s administrative role utilized a multisig, the minting role, the ultimate lever of power, was dangerously centralized to a single key.
The attacker capitalized on this weakness by depositing a relatively modest sum, between $100,000 and $200,000 in USDC, across a few requestSwap() calls. Through the compromised completeSwap() flow, the attacker orchestrated an astonishing over-mint, generating approximately 80 million USR tokens. This massive inflation occurred in two primary transactions: an initial mint of roughly 50 million USR, swiftly followed by another 30 million. This represented an over-mint ratio of 400x to 500x compared to the legitimate collateral deposited.
Crypto research fund D2 Finance, among the first to publish an in-depth analysis, articulated the stark reality: either an oracle was gamed, the off-chain signer was compromised, or, most likely, the fundamental amount validation between the request and completion steps was entirely missing. Security analysts at Cyvers and other independent researchers heavily favored the latter explanation, suggesting it was likely combined with a compromised private key controlling the SERVICE_ROLE. This was not a sophisticated reentrancy attack or a flash loan exploit; it was a glaring operational security failure—a privileged role endowed with excessive power and woefully inadequate checks.

The Rapid Cashout: 17 Minutes to the Bottom
Once the 80 million illicitly minted USR tokens were in hand, the attacker moved with extraordinary speed and precision. D2 Finance aptly characterized the subsequent actions as a "textbook DeFi hack cashout running at full speed." The newly minted tokens were immediately unleashed onto various decentralized exchanges, including Curve, KyberSwap, and Velodrome. The attacker systematically swapped the devalued USR for more stable assets like USDC and USDT, which were then aggressively converted into Ethereum (ETH).
Blockchain security firm PeckShield reported tracking over $4.55 million worth of ETH (approximately 9,100 ETH) converted in the initial transactions alone. The total extracted value from the exploit is estimated to be in the range of $23 million to $25 million, a figure primarily constrained by the available liquidity on the targeted DEXs and the resultant slippage incurred during such a large-scale dump.
The impact on USR’s price was immediate and brutal. On Curve’s crucial USR/USDC pool, the token’s value plummeted to a staggering low of 2.5 cents, a mere 17 minutes after the first 50 million USR were minted. Across various platforms, reported lows for USR ranged from $0.20 to $0.257, representing a catastrophic 74% to 97% crash from its intended dollar peg. While the price saw a partial, ephemeral recovery to around $0.80-$0.87 on some pairs, the depeg has persisted significantly, with some trackers indicating USR trading as low as $0.05 to $0.07 at the time of writing. On-chain transaction data visibly showed multiple failed transactions during the dump, illustrating the attacker’s desperate race to exit before liquidity pools were entirely depleted.
Resolv Labs’ Immediate Response and User Impact
In the immediate aftermath, Resolv Labs confirmed the exploit via an official statement posted on X (formerly Twitter). The protocol announced that all functions had been paused and that an investigation was underway. Their statement notably emphasized that "the collateral pool remains fully intact and no underlying assets were lost," framing the issue as isolated to the USR issuance mechanics.
While technically accurate in that the ETH, staked ETH, and Bitcoin collateral backing pre-exploit USR still existed within the protocol, this framing somewhat understated the profound impact on users. Anyone holding USR acquired on the open market, or those who had legitimately minted USR and did not manage to exit before the price collapse, found themselves holding tokens worth only a fraction of their initial value. The company’s statement offered little solace to those who had seen their holdings evaporate. The expected path forward for legitimate holders typically involves recovery via pre-exploit snapshots, a mechanism used in similar mint exploits to roll back inflated supply while preserving underlying collateral. However, as of the latest updates, no concrete plan, timeline, or specific recovery mechanism had been formally announced by Resolv Labs, leaving many users in limbo.
The Ripple Effect: Contagion Across DeFi
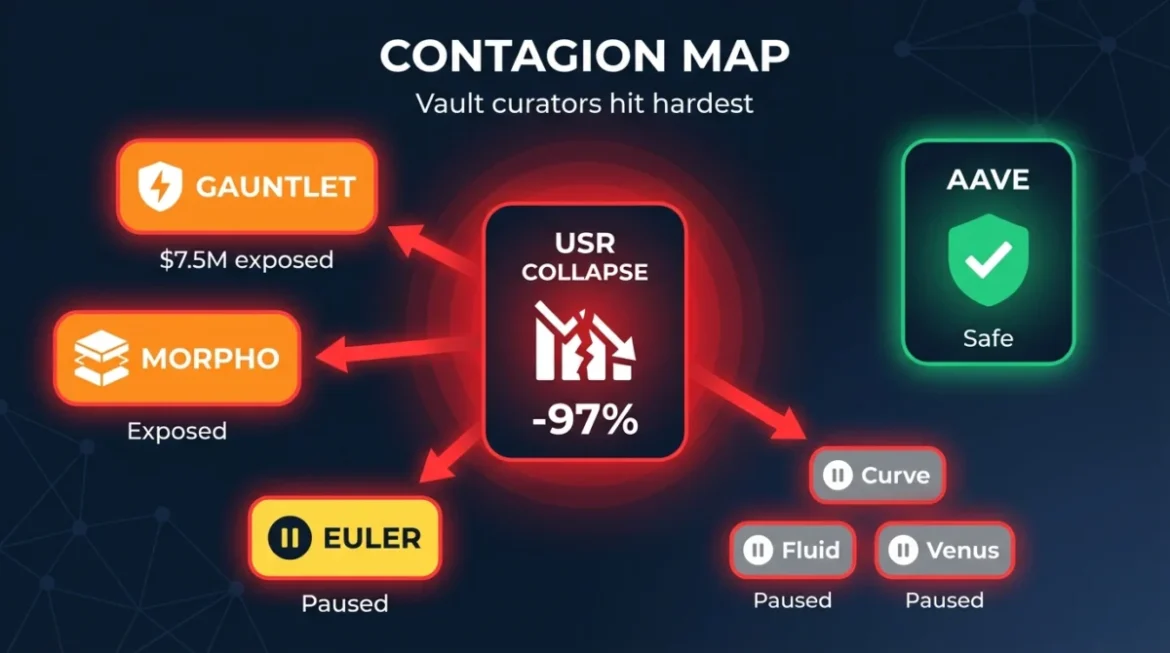
The damage from the Resolv exploit did not remain confined to the immediate protocol. USR and its derivatives, including wrapped staked USR (wstUSR) and RLP, were deeply integrated into a multitude of lending markets and curated yield vaults throughout the broader DeFi ecosystem. When USR’s price catastrophically collapsed, the ensuing contagion spread rapidly through these interconnected integrations.
Gauntlet, a prominent vault curator on Morpho, emerged as one of the most visibly affected entities. Their initial statement acknowledged the exploit and suggested that most vaults were unaffected, with only a few high-yield vaults carrying "limited exposure." However, subsequent community analysis revealed a more specific and concerning picture. Gauntlet USDC Core on Ethereum reportedly had an allocation of approximately $4.95 million within a wstUSR/USDC market, characterized by high utilization and severely diminished available liquidity post-depeg. Gauntlet USDC Frontier and a dedicated Resolv USDC vault also showed significant exposure. On-chain observers estimated the total direct exposure across various affected Gauntlet vaults to be in excess of $7.5 million. In response, Gauntlet proactively paused deposits on certain Morpho Frontier and Core vaults to manage the unfolding liquidity crisis.
Steakhouse Financial, another major Morpho curator, found itself in an ironic position. It not only managed dedicated Resolv USR vaults but also served as a risk manager and consultant for Resolv itself. Just days prior to the exploit, Steakhouse had published a detailed risk assessment of the Resolv protocol, which, chillingly, discussed exploit scenarios as a theoretical risk. Steakhouse Financial subsequently confirmed that its main vaults had no direct exposure to the exploit.
Euler Labs announced it was actively investigating the unauthorized minting incident and had promptly implemented measures to isolate any potential risks within its protocol.
In contrast, Aave, one of DeFi’s largest lending protocols, emerged largely unscathed. Stani Kulechov, Aave’s founder, confirmed zero risk exposure to USR. While Resolv had participated in Aave as a liquidity provider, its collateral assets were already deposited and remained unaffected by the USR minting flaw. Resolv is reportedly in the process of repaying its debt and exiting Aave in an orderly fashion, a testament to Aave’s robust risk management frameworks.
Other protocols, including Fluid/Instadapp, Venus, Inverse Finance, and Lista DAO, took precautionary measures by pausing USR-related markets. The kpk (karpatkey) team, managing certain yield vaults, acknowledged limited RLP exposure but confirmed that affected positions had either been closed or withdrawn.
Unanswered Questions and Systemic Vulnerabilities
The Resolv Labs exploit has brought several critical, uncomfortable questions to the forefront, highlighting systemic vulnerabilities within the broader DeFi security paradigm:
-
Why a Single EOA for Mint Authorization? The most glaring flaw remains the decision to empower a single externally owned address (EOA) with the authority to control the
SERVICE_ROLE, which could mint arbitrary amounts of USR. While the protocol’s general admin role wisely utilized a multisig, placing the "money printer" under the control of a single key is an extraordinary abdication of basic security best practices. Even if the exploit was the result of a compromised private key rather than an inside job, this architectural choice made the protocol trivially exploitable once that key was obtained. Modern DeFi protocols typically employ multisigs, time-locks, and robust role-based access controls for such critical functions. -
Absence of On-Chain Limits? The lack of fundamental on-chain guardrails is baffling for a protocol managing hundreds of millions in TVL. Why were there no maximum mint limits per transaction, no per-epoch caps, and, critically, no sanity checks comparing the deposit amount against the minted output? These basic protective measures, designed to prevent or mitigate over-minting scenarios, were conspicuously absent from a core stablecoin function.
-
What Happened to the Audits? Resolv Labs’ contracts underwent multiple audits and partnered with security firms like Hypernative for real-time monitoring. The protocol even ran an Immunefi bug bounty program, where researchers actively competed to uncover vulnerabilities. Yet, the core minting flow—arguably the single most sensitive function in any stablecoin protocol—was deployed without proper validation, a flaw that Cyvers’ post-exploit analysis succinctly pointed out. This raises profound questions about the scope and efficacy of security audits, suggesting that while code might be checked for traditional bugs, fundamental design and operational security flaws, especially those involving off-chain interactions and privileged roles, can still slip through.
-
The Pre-Exploit Capital Flight: The 75% market cap contraction over roughly six weeks, from $400 million to $100 million, is not typical organic behavior for a stablecoin. While yield farming capital is notoriously volatile and the end of points programs often triggers exits, the scale and timing of this withdrawal invite intense scrutiny. Was there a fundamental flaw in the protocol’s economic model that caused a quiet exodus, or did certain entities have privileged information or a deeper understanding of the risks that led them to unwind positions ahead of time?
Broader Implications for Decentralized Finance
The Resolv Labs incident is not merely another exploit; it serves as a potent case study with profound implications for the broader DeFi landscape:
-
Operational Security Trumps Complex Engineering: This exploit was not a novel, esoteric attack vector leveraging a complex smart contract vulnerability. Instead, it was a fundamental failure of basic operational security and access control. The minting flow relied on implicit trust in an off-chain signer with no on-chain enforcement of correct behavior. The contract performed precisely as it was instructed; the failure lies in the design that allowed it to be instructed to mint arbitrary amounts. This highlights that robust security encompasses not just code integrity but also secure key management, proper access controls, and comprehensive input validation.
-
Compounding Integration Risk: For participants in DeFi yield strategies, the Resolv incident is a stark reminder of how integration risk compounds. A user depositing into a yield vault that then allocates funds to a Morpho market, which in turn lends against wstUSR, is three or more layers removed from the underlying minting contract. Each layer offers convenience and potential yield but also introduces exposure to failures that individual users may lack the tools, expertise, or time to adequately evaluate. This layering effect amplifies systemic risk across the ecosystem.
-
Growth Versus Security Maturity: Resolv’s rapid ascent from under $50 million to over $650 million in TVL in under three months during its initial points season—driven largely by leverage looping on Morpho and Euler—illustrates the critical gap between explosive growth and security maturity. Such rapid scaling attracts significant capital, numerous integrations, and intense attention. However, it also means the protocol was bearing the weight of hundreds of millions of dollars while still operating with a core minting function controlled by a single, unvalidated wallet. This incident underscores the danger of prioritizing growth and market penetration over the meticulous, often "boring," work of building truly robust security foundations.
-
Stablecoin Design and Trust: The exploit also casts a shadow on the reliability of newer, more complex stablecoin designs, particularly those employing hybrid collateralization and intricate hedging strategies. While innovative, these designs often introduce additional points of failure, especially when critical components rely on off-chain processes or privileged roles. The incident reminds the community that the promise of a dollar peg is only as strong as the weakest link in its underlying mechanics and governance.
The Path Forward
As of now, Resolv Labs has paused all protocol functions, effectively freezing the system. The most likely path for recovery for legitimate USR holders involves a mechanism based on pre-exploit snapshots, similar to how other protocols have handled inflated supply exploits while the underlying collateral remains intact. However, the absence of a detailed timeline or specific mechanism from Resolv Labs leaves many users in a state of uncertainty.
The attacker’s wallet addresses are under active surveillance by prominent blockchain security firms, including PeckShield, Cyvers, and D2 Finance, as well as a dedicated community of on-chain researchers. While a significant portion of the extracted value has already been converted to ETH, the tracking efforts continue, with the hope of identifying the perpetrators and potentially recovering some assets.
Users who have funds in any Gauntlet-curated vaults, particularly USDC Core and Frontier, are strongly advised to check their positions directly on Morpho. Liquidity constraints resulting from the depeg of USR and its derivatives may temporarily affect withdrawal capabilities on markets with exposure to USR, wstUSR, or RLP.
The DeFi community eagerly awaits a full, transparent postmortem from Resolv Labs. This critical document must address key questions: precisely how the SERVICE_ROLE key was secured, what real-time monitoring was in place to detect anomalous mints, and why such a fundamental validation gap persisted in a function that had been integral to the contract since its initial deployment.
Until these questions are thoroughly answered, the Resolv protocol remains frozen, serving as another sobering case study for the decentralized finance industry. It is a powerful, costly reminder that the often-overlooked aspects of security—meticulous key management, robust access controls, and comprehensive input validation—ultimately matter more than the most clever or complex algorithmic designs. The pursuit of innovation in DeFi must be inextricably linked with an unwavering commitment to foundational security principles.