An extensive data extortion attack, orchestrated by the notorious cybercrime group ShinyHunters, sent shockwaves through the United States’ education system today, severely disrupting classes and coursework for millions of students and faculty. The attack targeted Canvas, a widely-used education technology platform developed by Instructure, leading to the defacement of its login page with a stark ransom demand. The message threatened to leak sensitive data purportedly stolen from an astonishing 275 million students and faculty across nearly 9,000 educational institutions, highlighting the profound vulnerability of critical digital infrastructure within the academic sphere.
The Cyberattack Unfolds: A Disruptive Defacement
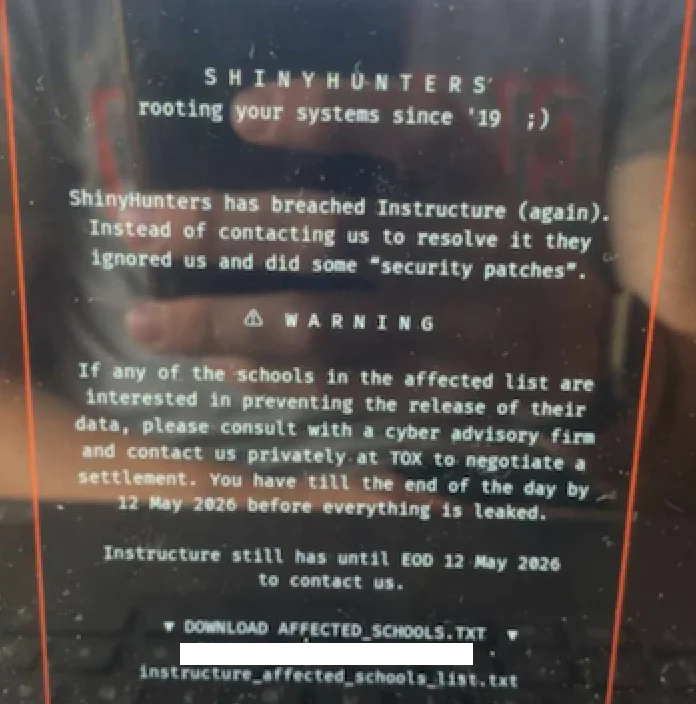
The morning of Thursday, May 7, brought widespread alarm as countless students and educators attempting to access Canvas were met not with their usual login portal, but with a brazen extortion message from ShinyHunters. This public defacement served as a dramatic escalation in an ongoing saga, transforming a previously acknowledged data breach into an immediate, visible crisis. The message directly addressed affected schools, advising them to negotiate their own ransom payments to prevent the publication of their data, regardless of Instructure’s decision to comply with the attackers’ demands.
Instructure, the parent company of Canvas, responded swiftly by disabling the platform, which serves as the digital backbone for thousands of schools, universities, and businesses to manage coursework, assignments, and facilitate communication. The service was replaced with a generic message indicating "scheduled maintenance," a descriptor that would later draw sharp criticism from cybersecurity experts for allegedly downplaying the severity of the incident. The timing of this disruption could hardly have been worse, coinciding with final exams for many affected institutions, potentially jeopardizing academic continuity and student outcomes across the nation.
Instructure’s Initial Response and Escalation
The May 7 defacement was not an isolated incident but the public culmination of a breach that Instructure had acknowledged earlier in the week. On May 6, Instructure released a statement confirming a data breach, following ShinyHunters’ initial claim of responsibility and their threat to leak data from tens of millions of students and faculty unless a ransom was paid. The initial deadline for this payment was set for May 6, subsequently extended to May 12, indicating a period of attempted negotiation or assessment by Instructure.
In its May 6 update, Instructure detailed the nature of the stolen information, stating that their investigation thus far indicated the breach included "certain identifying information of users at affected institutions, such as names, email addresses, and student ID numbers, as well as messages among users." Crucially, the company asserted that it had found no evidence of more sensitive data like passwords, dates of birth, government identifiers, or financial information being compromised. At that juncture, Instructure maintained that Canvas was "fully operational" and that they were "not seeing any ongoing unauthorized activity on their platform," concluding, "At this stage, we believe the incident has been contained."
However, this declaration of containment proved premature. By mid-day on May 7, the login pages for Canvas across numerous schools and universities were hijacked, displaying ShinyHunters’ ransom demand. This forced Instructure to pull Canvas offline entirely, replacing the portal with the "scheduled maintenance" message. The company’s status page initially stated, "We anticipate being up soon, and will provide updates as soon as possible," reflecting the scramble to regain control and restore services. The rapid escalation from a contained breach to a public defacement underscored the attackers’ persistent access and Instructure’s inability to fully mitigate the threat.
ShinyHunters: A Prolific Threat Actor in the Cyber Underworld
The group behind this disruptive attack, ShinyHunters, has established itself as a formidable and highly active presence in the cybercrime landscape, specializing in data theft and extortion. Operating with a fluid and adaptive methodology, they are known for gaining initial access to corporate networks through sophisticated social engineering tactics, particularly voice phishing. This often involves impersonating IT personnel or other trusted figures within a targeted organization to trick employees into divulging credentials or granting access to sensitive systems.
ShinyHunters boasts a disturbing track record of high-profile data breaches across various industries. Just last month, the group claimed responsibility for compromising the home security giant ADT, allegedly exfiltrating personal information belonging to 5.5 million customers. In that instance, ShinyHunters reportedly breached ADT by compromising an employee’s Okta single sign-on account through a voice phishing attack, which then granted them access to ADT’s Salesforce instance. Beyond ADT and Instructure, the group has taken credit for a series of other significant extortion attacks against prominent organizations, including Medtronic, Rockstar Games, McGraw Hill, 7-Eleven, and the cruise line operator Carnival. This extensive portfolio underscores their capabilities and their willingness to target large enterprises with vast user bases.
Charles Carmakal, Chief Technology Officer at Google-owned Mandiant Consulting, confirmed the group’s heightened activity, noting that "there are multiple concurrent and discrete ShinyHunters intrusion and extortion campaigns happening right now." This observation highlights the scale of ShinyHunters’ operations and suggests that the attack on Canvas customers is part of a broader, coordinated campaign targeting various entities simultaneously.
A Chronology of Compromise: From Penn to Pandemic-Era Learning
The Canvas incident, while dramatic, appears to be the latest chapter in a protracted campaign by ShinyHunters against Instructure. Cybersecurity expert Dipan Mann, founder and CEO of Cloudskope, provided critical context, arguing that today’s outage was misleadingly labeled as "scheduled maintenance" and that Instructure had been breached by ShinyHunters at least three times in the past eight months.
Mann pointed to a significant precursor: the September 2025 breach involving the University of Pennsylvania. In that incident, ShinyHunters released thousands of internal University of Pennsylvania files, including donor records, internal memos, and other confidential materials. While the Daily Pennsylvanian and other outlets initially framed it as a Penn-specific hack, Mann asserted that the breach was, in part, facilitated through a "Canvas/Instructure-mediated access path." As Mann eloquently put it in a blog post, "Penn was the named victim. Instructure was the mechanism. The incident was treated as a Penn-specific story by most of the national press and quietly handled by Instructure as a customer-specific matter. That framing was wrong then. It is dramatically more wrong in light of the May 2026 events, which now look like the planned escalation of an attack pattern that ShinyHunters had been working against Instructure’s environment for at least eight months prior."
According to Mann, the September 2025 Penn breach served as a "proof of concept" for ShinyHunters. The May 1, 2026, incident, when Instructure first acknowledged unauthorized access, was the "production run." And the May 7, 2026, defacement represented ShinyHunters "demonstrating publicly that the May 2 ‘containment’ did not happen." This detailed chronology paints a picture of a persistent attacker systematically exploiting vulnerabilities, with Instructure repeatedly failing to fully address the root cause or contain the threat.
In February, a ShinyHunters spokesperson revealed to The Daily Pennsylvanian that Penn had refused to pay a $1 million ransom demand. Consequently, on March 5, ShinyHunters made good on their threat, publishing 461 megabytes of data stolen from the university, including thousands of files such as donor records and internal memos. This history underscored the group’s resolve and the tangible consequences of non-compliance with their extortion demands, adding immense pressure to Instructure and its customers during the current crisis.
The Vulnerability of Educational Platforms: Data at Risk
Canvas is not merely a platform; it is a critical piece of digital infrastructure underpinning modern education. As one of the dominant Learning Management Systems (LMS) globally, it serves millions of students, faculty, and administrators across K-12 districts, higher education institutions, and even corporate training programs. Its pervasive adoption means that a breach affecting Canvas has far-reaching consequences, impacting academic operations, student privacy, and institutional reputation on an unprecedented scale.
The types of data typically stored within an LMS like Canvas are extensive and sensitive. While Instructure confirmed the theft of names, email addresses, student ID numbers, and user messages, ShinyHunters claimed to possess "several billion private messages among students and teachers, as well as names, phone numbers and email addresses." Even without highly sensitive financial or government ID data, the compromise of this information can have significant repercussions. Stolen names and email addresses are prime fodder for sophisticated phishing campaigns, targeting both individuals and their affiliated institutions. Student ID numbers can be exploited for identity fraud, and private messages could contain personally identifiable information, academic integrity issues, or even sensitive personal communications that, if leaked, could cause immense distress and reputational damage.
The education sector, despite its critical role, is frequently identified as a prime target for cybercriminals. Often operating with tighter budgets and fewer dedicated cybersecurity resources compared to private corporations, educational institutions present an attractive target due to the sheer volume of personal data they handle – data that encompasses minors, young adults, and faculty, making it valuable on the dark web. The increasing reliance on digital learning tools, accelerated by the global shift to remote education, has further expanded the attack surface, making robust cybersecurity measures more crucial than ever.
The "Scheduled Maintenance" Controversy and Expert Critique
Dipan Mann’s critique of Instructure’s communication strategy centered on the company’s decision to characterize the forced shutdown of Canvas on May 7 as "scheduled maintenance." This framing, Mann argued, was disingenuous and indicative of a broader pattern of downplaying the severity of security incidents. For users experiencing immediate disruption to their academic lives, the message felt dismissive and lacked transparency.
Mann highlighted that Instructure’s Chief Information Security Officer, Steve Proud, had declared the incident "contained" on May 2, just days before the platform was publicly defaced and taken offline. This discrepancy between official statements and the reality on the ground eroded trust and raised serious questions about Instructure’s security posture and incident response capabilities. Experts like Mann stressed that transparency is paramount in cybersecurity incidents, particularly when critical services are affected. Misleading communications can hinder effective response by affected institutions and individuals, and damage the long-term credibility of the service provider. The repeated nature of the breaches by ShinyHunters against Instructure, as detailed by Mann, suggested a systemic issue rather than isolated incidents, further intensifying the criticism.
Navigating the Ransom Dilemma: Institutions Caught in the Middle
The extortion message displayed on the Canvas login page presented a grave dilemma for thousands of educational institutions: negotiate independently with ShinyHunters or risk the public exposure of their data. This tactic is designed to create internal division and pressure, forcing individual institutions to weigh the immediate costs of paying a ransom against the potentially far greater long-term costs of data leakage, including reputational damage, legal liabilities, and the erosion of trust among their students and faculty.
A source close to the investigation, speaking to KrebsOnSecurity on condition of anonymity due to the sensitive nature of the discussions, confirmed that a number of universities had indeed approached the cybercrime group to negotiate payments. The subsequent removal of Instructure from ShinyHunters’ data leak blog, alongside the samples of stolen data from Canvas customers, further indicated that either negotiations were underway or a payment had been made. Cyber extortion groups typically only remove victims from their leak sites after receiving a ransom payment or reaching an agreement to negotiate.
On May 11, Instructure posted a significant update, confirming they had paid ShinyHunters. The statement read: "Instructure posted an update saying they paid their extortionists in exchange for a promise to destroy the stolen data. The data was returned to us. We received digital confirmation of data destruction (shred logs). We have been informed that no Instructure customers will be extorted as a result of this incident, publicly or otherwise."
This decision to pay the ransom, while pragmatic in protecting sensitive data and restoring academic continuity, raises complex ethical and practical questions. While it ensured the return and purported destruction of the stolen data, it also inadvertently validates the extortion model, potentially emboldening ShinyHunters and other cybercriminal groups to pursue similar attacks in the future. The financial cost of such a payment is substantial, but for a company like Instructure, whose entire business model relies on trust and reliability in the education sector, the cost of a catastrophic data leak and prolonged outage could have been far greater.
Unveiling the Root Cause: The Free-for-Teacher Exploit
In an update published on May 8, Instructure shed more light on the technical vulnerability exploited by ShinyHunters. The company confirmed that Canvas was functioning normally again and, crucially, revealed that the hackers exploited "an issue related to Free-for-Teacher accounts." This was a critical disclosure, as Instructure admitted it was "the same issue that led to the unauthorized access the prior week."
As a direct consequence of this repeated exploitation, Instructure announced "the difficult decision to temporarily shut down Free-for-Teacher accounts." These accounts, designed to provide educators with free access to Canvas features, have been a "core part of our platform," according to Instructure, which committed to resolving the underlying security issues. While these free accounts are distinct from the premium, institution-managed versions of Canvas, the fact that they served as an entry point for a widespread breach affecting paid customers highlights a critical security flaw. Free tiers, while valuable for market penetration and accessibility, can sometimes introduce unforeseen vulnerabilities if not secured with the same rigor as enterprise-level services, creating a potential weak link in the overall security chain.
Instructure stated that affected organizations were notified on May 6 and reiterated that direct outreach would be the sole verified source of information for impacted institutions. This guidance aimed to prevent panic and misinformation spread through unverified third-party lists or social media posts.
The Broader Implications for Ed-Tech Security
The Canvas breach by ShinyHunters serves as a stark reminder of the escalating cyber threats facing the education technology sector. The incident underscores the critical reliance of modern education on third-party vendors and the cascading effects when these vendors become targets. For Instructure, the breach represents a significant blow to its reputation and could lead to intensified scrutiny from its vast customer base, potentially impacting future contracts and market share.
The incident also highlights the need for a more proactive and resilient cybersecurity posture across the entire education ecosystem. Educational institutions, whether K-12 or higher education, must rigorously vet the security practices of their ed-tech partners, demand transparent incident response plans, and understand the potential attack vectors that third-party services can introduce. The "path of least resistance," as Dipan Mann noted, has often been for education vendors and institutions to quietly absorb breaches. However, the scale and public nature of the Canvas defacement may force a shift in this approach, compelling greater pressure for robust security measures and more forthright communication from service providers.
Ultimately, the Canvas attack underscores the imperative for continuous investment in cybersecurity, not just by platform providers but by every institution utilizing these vital digital tools. As education continues its digital transformation, ensuring the integrity and security of learning platforms is paramount to protecting student data, maintaining academic continuity, and fostering trust in the digital classroom. The lessons learned from this incident will undoubtedly shape future security strategies for ed-tech companies and the institutions they serve, reinforcing the need for vigilance, transparency, and collaboration in the face of evolving cyber threats.