The United Kingdom government issued a secret directive to Apple Inc. two weeks ago, demanding the inclusion of a backdoor into the company’s end-to-end encrypted iCloud Backup feature. This undisclosed order, reportedly issued last month, requires a blanket capability to access fully encrypted material, not merely assistance in cracking a specific account. Its implementation would represent a significant setback for technology firms in their long-standing efforts to avoid being compelled to act as government tools against their users, according to sources speaking on condition of anonymity due to the legally and politically sensitive nature of the matter.
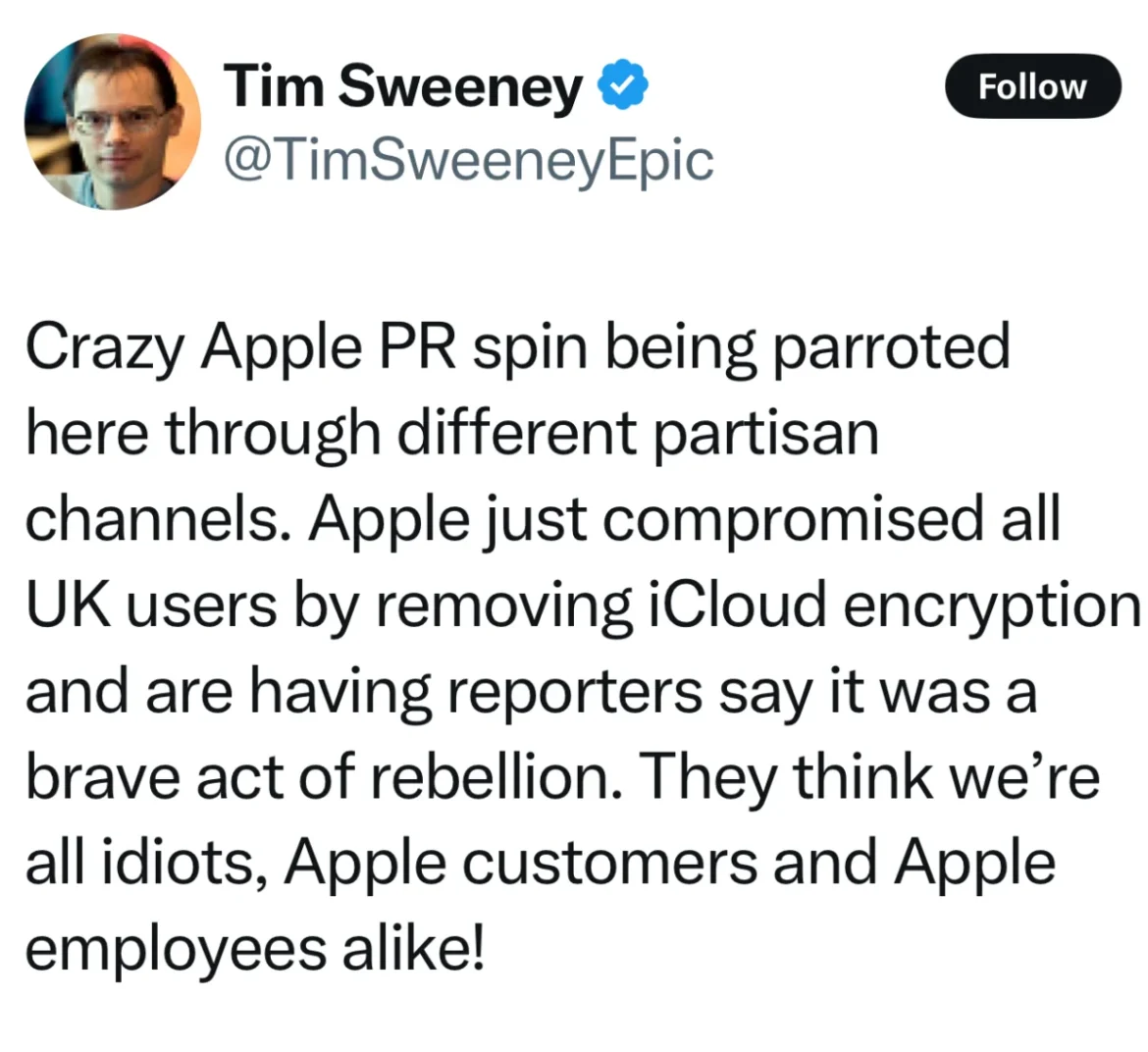
Following this revelation, a prediction was made that Apple would soon disable its end-to-end encrypted iCloud backup feature, known as Advanced Data Protection, for all users in the U.K. This prediction was confirmed on Friday, as reported by the BBC. Apple’s decision to disable this encrypted cloud backup feature has ignited widespread reactions, including sharp criticism from some observers who accuse Apple of compromising user privacy.
This development prompts a critical examination of the underlying issues, requiring a measured approach to understanding the motivations and potential ramifications.

The Evolving Landscape of Encryption and Government Access
Encryption, at its core, is a method of securing data by transforming it into an unreadable format, accessible only with a specific key. End-to-end encryption (E2EE) takes this a step further by ensuring that only the intended users possess the keys, rendering the data inaccessible even to the service provider. This robust security model protects users from various threats, including data breaches, cyberattacks, and sophisticated state-sponsored actors. However, a significant consequence of E2EE is its ability to impede access by law enforcement agencies and governments, creating a persistent tension between digital security and public safety mandates.
Apple has historically navigated this complex trade-off, largely by prioritizing the deployment of strong encryption across its product ecosystem. This stance has often led to friction with governmental bodies. A landmark instance was the 2016 Apple v. FBI encryption dispute, where the company staunchly resisted a U.S. government demand to bypass encryption on an iPhone linked to a terrorism investigation. Apple argued that complying would necessitate weakening encryption for all its devices, a move with far-reaching implications for user security. Then-CEO Tim Cook publicly defended the company’s commitment to encryption in an open letter.
Despite its general advocacy for encryption, Apple has also faced scrutiny for past proposals. In 2021, the company announced plans to implement client-side scanning of iCloud Photos to detect child sexual abuse material. This initiative, while aimed at a critical issue, raised concerns among privacy advocates and technical experts who foresaw potential avenues for broader government-mandated data surveillance, even within encrypted backups. Following swift technical critiques highlighting potential flaws and significant public backlash, Apple first paused, and subsequently abandoned, this plan in 2022. This history suggests a pattern of Apple taking substantial risks to promote encryption, albeit with occasional missteps.
Understanding the U.K.’s Investigatory Powers Act
The U.K. government’s recent actions appear to be rooted in the Investigatory Powers Act 2016, colloquially known as the "Snooper’s Charter." Enacted in 2016, the law granted authorities broad surveillance powers, and critics at the time expressed concerns that it could be leveraged to secretly undermine security systems, potentially increasing their vulnerability to hacking.

A pivotal aspect of this legislation is its provision for secret "Technical Capability Notices" (TCNs). These notices can compel service providers, such as Apple, to alter their system’s operational parameters. In the context of E2EE, this could involve mandating that the provider retain a copy of user encryption keys, thereby enabling government access to data upon demand.
A particularly contentious feature of the U.K. law is its perceived lack of explicit distinction between U.K. and non-U.K. customers. Apple’s legal counsel highlighted this concern in a 2024 submission to Parliament, suggesting that the law could grant the U.K. government the authority to dictate global cybersecurity standards. Under a stringent interpretation, the U.K. could potentially set a cap on the level of digital security available to users worldwide, irrespective of their location, without their knowledge. This could inadvertently expose vast quantities of data to state-sponsored adversaries, as evidenced by recent compromises of telecommunications industries. Moreover, the secrecy surrounding TCNs could force companies like Apple into a position of misleading their customers about the true security of their devices.
The Unfolding Scenario: Apple’s Response to a Global Demand
The situation intensifies when considering the possibility of a broad, global demand from the U.K. government. If Apple were compelled to alter its systems worldwide to disable E2EE for all users, the implications would be catastrophic. Engaging with such a demand would effectively cede control of Apple’s security infrastructure to a single nation, dictating global security protocols. It would also create an untenable diplomatic and operational dilemma, forcing Apple to disclose to other major powers, such as China, the European Union, and the United States, that a backdoor has been provided to the U.K. This could precipitate demands for similar access from other governments, leading to a global erosion of digital privacy and security.
Given the severe repercussions, engaging with such a demand is likely not a viable option for Apple. The company faces a limited set of strategic choices in such a scenario:

-
Legal Challenges: Apple could pursue extensive legal avenues to contest the order within the U.K.’s judicial system. This might involve engaging with secret court proceedings, which, similar to the U.S. Foreign Intelligence Surveillance Court (FISA), may not offer a balanced platform for a foreign company.
-
Disabling the Feature: As observed, Apple has opted to disable end-to-end encrypted iCloud Backup for U.K. users. This action effectively nullifies any demand for a backdoor within that specific feature for U.K. customers, as the feature itself will no longer offer that level of protection. U.K. users will be unable to enroll in Apple’s E2EE backup service starting February 21st. The handling of existing users’ data remains unclear, but they may face a choice between downgrading to unencrypted backups or losing their stored data.
-
Withdrawing Services: In extreme circumstances, if faced with insurmountable demands that fundamentally compromise user security and privacy, a company might consider withdrawing its services from a particular jurisdiction. This represents a drastic measure with significant economic and reputational consequences.
-
Public Exposure: While potentially risky, a company might choose to publicly disclose the government’s demands, hoping to rally public opinion and international pressure to resist. However, the secret nature of TCNs makes this approach challenging.

Timeline and Immediate Ramifications
- Last Month: The U.K. government reportedly issued a secret directive to Apple.
- Two Weeks Ago: The Washington Post broke the story of the secret order.
- Following the Report: Speculation arose that Apple would disable E2EE iCloud Backup for U.K. users.
- Friday (Date of BBC Report): Apple confirmed the disabling of its end-to-end encrypted iCloud Backup feature for U.K. users. The feature will cease to be available for new enrollments on February 21st.
The implications of this move are substantial. For U.K. users who relied on Advanced Data Protection, their cloud backups will revert to a less secure, standard encryption model. This change significantly alters the privacy landscape for millions of individuals within the U.K., potentially exposing their sensitive data to greater risk. The global implications are also significant, as this event sets a precedent and highlights the growing tension between national security interests and the fundamental right to digital privacy.
Broader Impact and Future Considerations
The U.K. government’s actions and Apple’s response have ignited a critical global conversation about the balance between security and privacy in the digital age. This incident underscores the potential for governments to exert pressure on technology companies to weaken encryption, a cornerstone of modern digital security. The move by Apple, while seemingly a concession, can also be interpreted as a strategic maneuver to isolate the demand to a specific region and feature, thereby preventing a broader compromise of its global encryption infrastructure.
The long-term consequences remain to be seen. The U.K. government may choose to de-escalate its demands, particularly if faced with significant international pressure or widespread public outcry. Conversely, if the U.K. government persists, this could trigger further legal battles, policy debates, and potentially inspire similar demands from other nations. The future of end-to-end encryption and the extent to which it can withstand governmental pressure will be shaped by these ongoing developments, impacting how individuals and organizations protect their digital lives worldwide.