The evolving digital landscape is increasingly demanding robust user authentication, yet simultaneously raising profound privacy concerns. As legislative pressures mount and artificial intelligence proliferates, the fundamental question of how individuals can prove their identity online without surrendering their personal data to a potential "privacy dystopia" has become paramount. This article delves into the critical cryptographic concept of anonymous credentials, exploring their genesis, technical underpinnings, and their growing relevance in a world grappling with routine identity verification.
The Internet’s shift from a loosely authenticated space to one requiring stringent identification measures is driven by a confluence of factors. Historically, many online platforms operated on a more permissive model, where pseudonymous accounts or minimal anti-bot measures sufficed. This era, however, is rapidly receding. The rise of advertising-driven business models incentivizes platforms to collect granular user data, making precise identification a valuable commodity. More significantly, a surge in legislative initiatives mandating age verification for access to age-restricted content is forcing a broad overhaul of online authentication protocols.
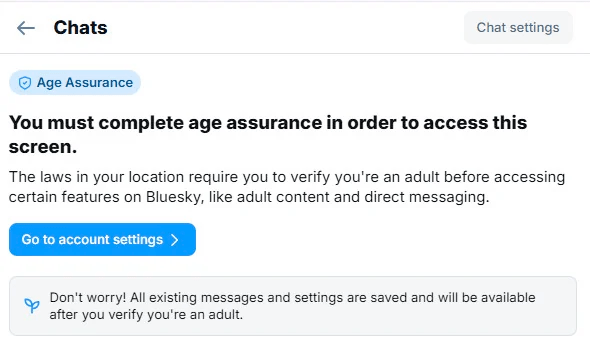
This legislative push, initially aimed at safeguarding minors from inappropriate content, has inadvertently created a widespread requirement for users to present verifiable identification to a multitude of online services. Twenty-five U.S. states and at least a dozen countries have enacted or are considering laws that compel website operators to confirm users’ ages. Consequently, age verification mechanisms are now appearing on major social media platforms like Facebook, BlueSky, and X, as well as communication services such as Discord. Even entities like Wikipedia are facing pressure to implement identity checks due to legislation such as the UK’s Online Safety Bill. The practical implication is a landscape where routine ID checks, rather than pseudonymous access, are becoming the norm.
The inherent risk in this transition is the creation of comprehensive, citizen-level transcripts of online activities. While some jurisdictions permit data minimization, allowing sites to discard identity information after verification, this is far from a universal standard. Furthermore, the lucrative nature of detailed user profiles in an AI-driven economy creates a strong financial incentive for advertising-supported platforms to retain this sensitive data, potentially linking online behavior to real-world identities with unprecedented accuracy. This scenario underscores the urgent need for cryptographic solutions that can decouple authentication from identification, a challenge addressed by the concept of anonymous credentials.
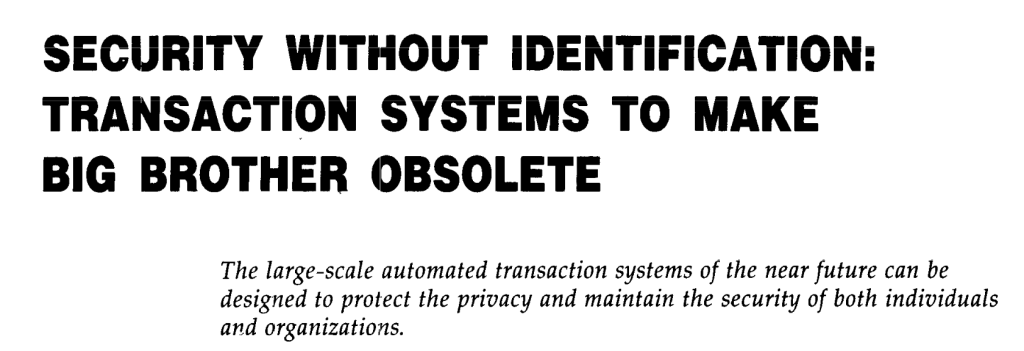
The Genesis of Anonymous Credentials: David Chaum’s Vision
The conceptual seeds for anonymous credentials were sown in the 1980s by cryptographer David Chaum. Long before the widespread adoption of the internet or smartphones, Chaum foresaw a future where individuals would routinely need to present electronic credentials to navigate daily life. He recognized the profound privacy implications of such a system and proposed a novel solution: the anonymous credential.
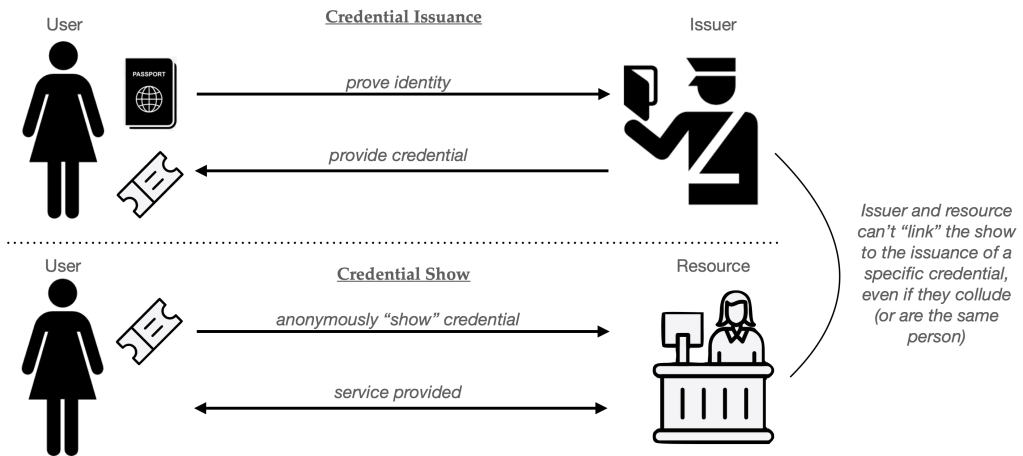
Chaum’s model aimed to fundamentally alter the traditional authentication flow. In a standard system, a user (or their device) must present a credential, such as a cookie or login token, to a resource provider to prove authorization. This credential is often linked to the user’s real-world identity, either directly through a username and password or indirectly through services like Google’s Single Sign-On (SSO). The critical privacy vulnerability arises when this credential, tied to one’s identity, is presented repeatedly to various resources. This allows for the potential creation of a detailed profile of the user’s online activities, linking every interaction to their actual identity.
The proposed solution was to break the inherent link between the issuance of a credential and its subsequent usage. In an anonymous credential system, when a user presents a credential to a resource, the resource should only learn that a valid credential has been presented by some authorized user. Crucially, the resource should not be able to ascertain which specific individual owns that credential. This anonymity holds even if the resource colludes with, or is itself, the entity that initially issued the credential. The outcome is that, from the perspective of the resource, the user’s activity is unlinked from their identity, allowing them to blend into an "anonymity set" of all users who possess valid credentials.
A popular analogy for this concept is the digital equivalent of a physical wristband, commonly distributed at venues like clubs or festivals. Upon verifying identity and age at the entrance, an individual receives an unlabeled wristband. This wristband serves as proof of authorization (e.g., being of legal drinking age) without revealing the individual’s name or address to subsequent service providers, such as bartenders. While this analogy captures the essence of decoupling authorization from identity, digital credentials present unique challenges compared to their physical counterparts.
The Challenge of Digital Replication: Why a Single Credential Isn’t Enough
An intuitive question arises: why not simply issue every user the exact same credential? The appeal of this approach lies in its potential to achieve anonymity, as every user’s "show" would be identical. However, this strategy falters due to the fundamental difference between physical and digital objects: the ease of digital replication.
Unlike physical wristbands, which are at least somewhat difficult to duplicate, digital credentials can be copied infinitely and effortlessly. If a single credential were to be compromised, such as through a security breach on a user’s device, an attacker could generate an unlimited number of identical copies. These duplicates could then be used to create a vast army of bot accounts, bypass age verification systems, or be sold on the black market, all appearing indistinguishable to the resource provider.
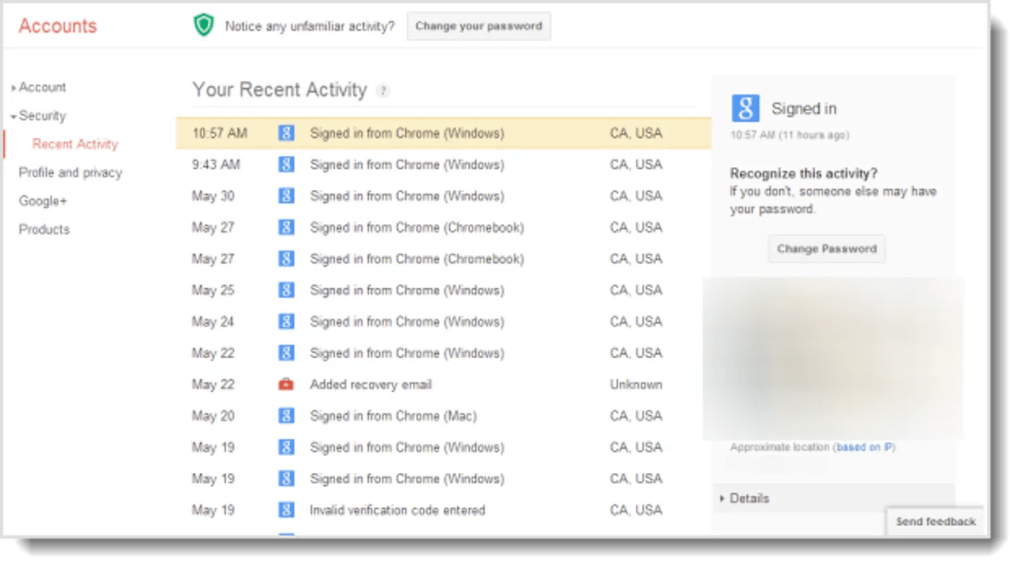
While this problem of credential cloning also exists for non-anonymous credentials like usernames and session cookies, traditional systems offer mechanisms for detection. Websites can monitor for suspicious patterns, such as a single "user" logging in from multiple, geographically disparate locations or an unusually high frequency of logins, a practice often referred to as "continuous authentication." However, the inherent anonymity of anonymous credentials renders these detection methods ineffective. When every credential "show" is identical, a resource has no basis to distinguish between a legitimate user accessing the service multiple times or a cloned credential being used by an army of bots. This vulnerability necessitates mechanisms to limit credential duplication.
Addressing Credential Cloning: Strategies for Limiting Duplication
To overcome the challenge of credential cloning, any practical anonymous credential system must incorporate methods to limit the proliferation and unauthorized use of credentials. Several approaches have been developed to achieve this:
- Single-Use Credentials: Each instance of a credential can only be used once. After its single use, it becomes invalid. This is the most straightforward approach but can lead to significant overhead if users require frequent access.
- Limited-Use Credentials: A credential is issued with a predetermined limit on the number of times it can be used, or a specific time frame within which it can be employed. For example, a credential might be valid for 100 uses or for a period of 24 hours.
- Revocable Credentials: The system allows for the invalidation of specific credentials, even if they have not been fully used, typically in response to detected abuse or compromise.
The literature on anonymous credentials explores numerous variants and combinations of these strategies, all aiming to introduce friction into the process of credential cloning and abuse.
Building a Single-Use Anonymous Credential: The Blind Signature Scheme
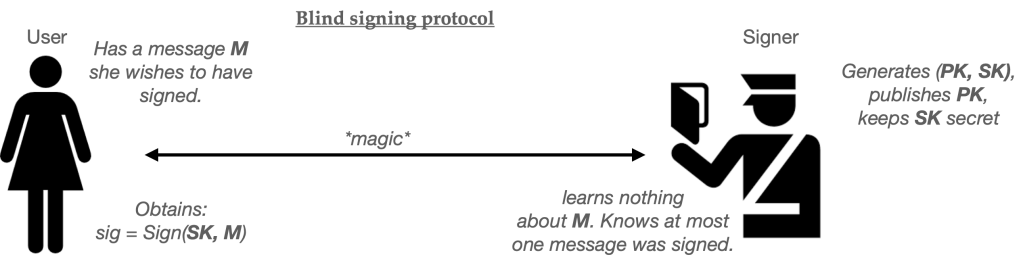
David Chaum’s original proposal for anonymous credentials relied on a cryptographic primitive known as a "blind signature scheme." Blind signatures are a variant of digital signatures that introduce an interactive protocol allowing for "blind signing." In this process, a user possesses a message they wish to have signed, and a server holds the private signing key. Through an interactive protocol, the user obtains a signature on their message. The server verifies that it has signed exactly one message but, crucially, does not learn the content of the message it has signed.
While a detailed construction of blind signature schemes is beyond the scope of this article, we can assume their availability as a foundational ingredient. Using a blind signature scheme, a basic single-use anonymous credential can be constructed as follows:
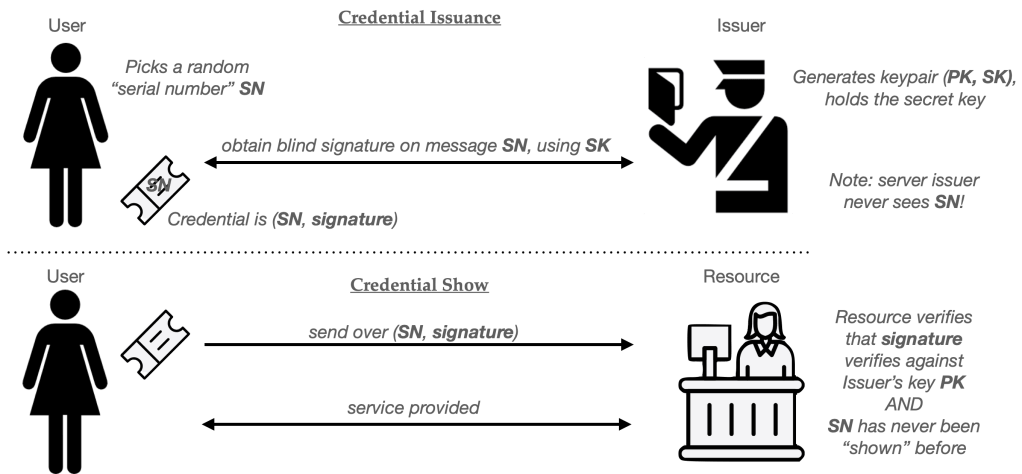
- Issuance: The User generates a unique, random serial number, denoted as SN. This serial number is specifically designed to be used only once. The User then presents SN to the Issuer within a blind signature protocol. The Issuer, using its private key, signs SN without learning its specific value. The User receives a signature on SN, along with the Issuer’s public key, PK.
- Presentation (Show): To authenticate to a Resource (e.g., a website), the User presents the pair (SN, signature) to the Resource.
- Verification: The Resource, possessing the Issuer’s public key PK, verifies that the provided signature is valid for the message SN. Crucially, the Resource also checks if this specific SN has been presented previously. If it has, the presentation is rejected. If the SN is new and the signature is valid, the Resource grants access.
This protocol provides privacy because the Issuer never learns the specific value of SN it signs, and therefore cannot link a credential "show" back to the specific user to whom it was issued. The Resource, by checking for previously used SN values, ensures that each credential is used only once.
Protocols like Privacy Pass, an IETF standard (RFC 9578), implement this concept using blind RSA signatures. These systems are effective for scenarios where the Issuer and the Resource are distinct entities. For cases where the Issuer and Resource are the same, a "blind MAC" variant can offer performance improvements.

However, single-use credentials, while functional, face limitations in terms of efficiency and expressiveness. The efficiency issue becomes apparent when a user requires frequent access. For instance, if an anonymous credential were to replace session cookies for a service like Google, a user might need to obtain and present thousands of single-use credentials daily. This can be mitigated by using an initial anonymous credential for registration and then trading it for a pseudonym issued by the site itself, such as a randomly generated username or a standard session cookie. However, this compromise links subsequent site accesses to the pseudonym.
The Need for Expressiveness: Beyond Simple Proofs
The expressiveness objection to basic Chaumian credentials highlights a more fundamental limitation: they carry minimal information. Consider the club wristband analogy: it essentially conveys a single piece of information – that the wearer is over 21. Many real-world scenarios, however, require more complex assertions.
Imagine a cryptocurrency exchange that requires users to prove not only their age but also their residency in a specific country, while simultaneously excluding residents of a particular state with its own regulatory framework. The exchange might also demand proof of being over 25 years old. In a non-anonymous system, a user could present a digitally signed driver’s license, which contains a wealth of structured information: name, address, state of issue, date of birth, and more. The exchange could then verify the signature and extract the necessary attributes to confirm compliance with its requirements.
The drawback of this approach is information leakage. Presenting a full driver’s license to the exchange would also reveal sensitive information, such as the user’s home address, which the exchange might not need and could potentially misuse. Furthermore, it directly links the user’s identity to each transaction. An ideal system would allow the user to prove only that they meet the specific requirements of the exchange, without revealing any extraneous personal data.
This is where Zero-Knowledge (ZK) proofs become invaluable. ZK proofs enable a "Prover" to convince a "Verifier" that they possess knowledge of a secret value that satisfies certain constraints, without revealing the secret itself. In the driver’s license example, a user could employ a ZK proof to demonstrate that they possess a valid, signed license and that specific fields within that license (e.g., state of residence, age) meet the exchange’s criteria. The ZK proof would convince the exchange of the validity of the claims without disclosing the user’s full identity or other personal details.
Zero-Knowledge Proofs: Empowering Expressive and Reusable Credentials
The integration of ZK proofs into anonymous credential systems offers significant advantages. It allows for the construction of credentials that are not only expressive but also reusable, addressing the efficiency limitations of single-use credentials. A single digitally signed driver’s license, for instance, could be used to satisfy the requirements of multiple different websites, each with its own set of criteria. The ZK proof mechanism ensures that each "show" of the credential remains unlinkable to other "shows" by the same user, preserving anonymity.
However, this reusability introduces a renewed concern about credential cloning. If a reusable credential, such as a digital driver’s license, is compromised, an attacker could potentially create an unlimited number of identical copies, leading to widespread abuse.
Winning the Clone Wars: Advanced Techniques for Credential Security
Mitigating the risks associated with reusable anonymous credentials requires sophisticated security measures. One approach, championed by proposals like Google’s new anonymous credential scheme, involves tying credentials to secret keys stored within secure elements (SEs) in devices like smartphones. These SEs are designed to make credential duplication extremely difficult. However, the security of this approach is contingent on the robust security of a vast number of devices, which varies significantly across different phone models and manufacturers. The weakest link in such an ecosystem can compromise the integrity of the entire system.
This fragility necessitates alternative techniques that actively limit the utility of compromised credentials. When ZK proofs are employed, several methods can be used to achieve this:
- N-Time Use Credentials: These credentials can be "shown" a fixed number of times (N) before they expire. This is achieved by embedding a pseudorandom function (PRF) and a secret key (K) into the credential during issuance. Each time the credential is used, a unique serial number is generated using the PRF, the key K, and a counter (i). The ZK proof includes a clause that prevents the reuse of the same counter value, thus detecting attempts to exceed the allowed usage limit.
- Time-Limited Credentials: Credentials can be designed to expire after a certain date or time. This is implemented by embedding an expiration timestamp into the credential. The ZK proof then includes a condition that verifies the current system time is before the expiration time.
- Revocable Credentials: The ability to ban users who engage in malicious activity is crucial. With anonymous credentials, this poses a challenge as users are not explicitly identified. Clever techniques allow for the revocation of credentials even in an anonymous context. One method involves the user embedding a secret key (K) into the credential that powers a PRF. When a user abuses the system, the resource can ban them by recording a pair of values associated with their malicious activity. In subsequent authentication attempts, the user must prove that their credential’s PRF, when applied to the banned values, does not match the recorded banned serial numbers. This mechanism allows for the exclusion of malicious actors without requiring their explicit identification.
The Path Forward: Real-World Applications and Future Directions
The exploration of anonymous credentials is a complex and rapidly evolving field. While the foundational cryptographic principles are established, practical implementation faces numerous real-world challenges. These include the secure issuance of digital identity certificates, the development of user-friendly interfaces, and the establishment of trust frameworks among issuers, verifiers, and users.
The next steps in understanding this critical area involve examining concrete real-world systems. Projects like Privacy Pass and emerging proposals from major technology companies, such as Google’s integration of anonymous credentials with digital driver’s licenses on Android phones, offer tangible examples of how these cryptographic concepts are being translated into practical applications. These real-world implementations will provide crucial insights into the usability, scalability, and security of anonymous credential systems, paving the way for a future where online authentication can be both secure and privacy-preserving. The ongoing development in this domain is essential for navigating the increasingly complex digital world and ensuring that individuals can participate online without compromising their fundamental right to privacy.

