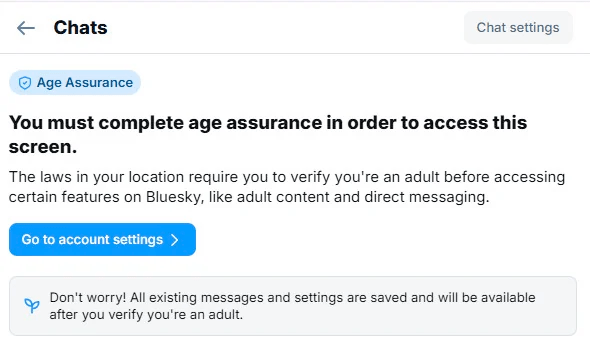
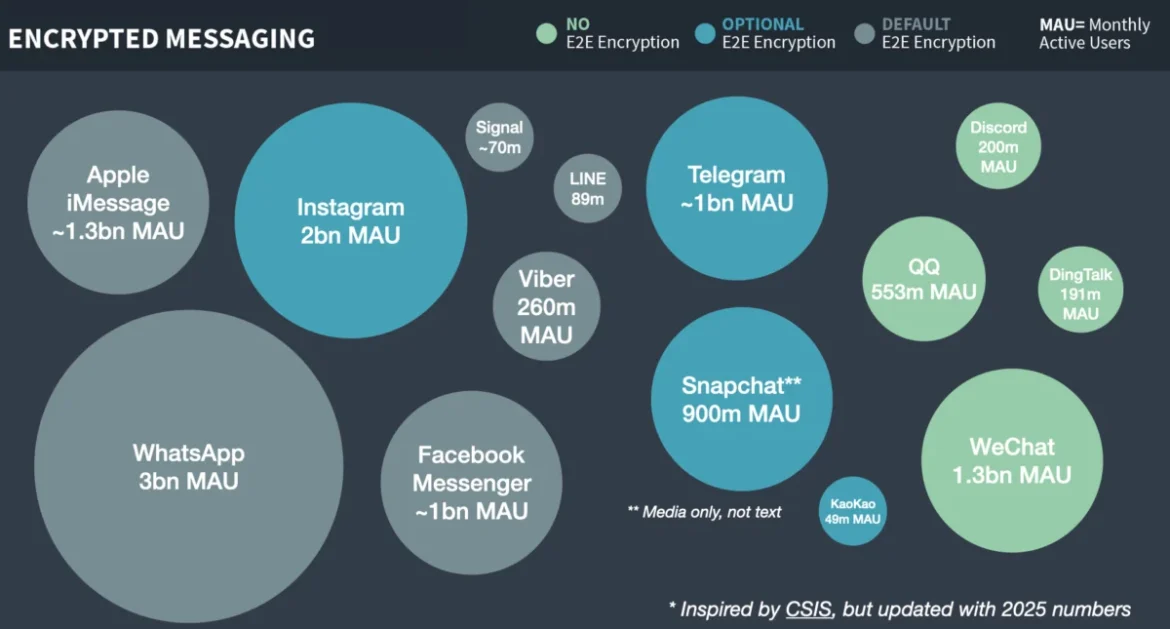
The recent rollout of X’s end-to-end encrypted messaging feature, now branded as XChat, has ignited a vigorous debate within the cybersecurity community regarding its cryptographic integrity and the underlying architecture. While X has positioned XChat as a secure communication channel, an in-depth analysis by security researchers has raised significant concerns, particularly around the management and storage of cryptographic keys, a critical component for any robust end-to-end encryption system.
The core of the controversy lies in XChat’s reliance on a system called Juicebox, a distributed key hardening service. While the concept of Juicebox aims to address the perennial challenge of users securely managing their own cryptographic keys, the specific implementation by X has drawn sharp criticism. Security experts argue that the current setup, as understood by external observers, presents substantial vulnerabilities that could undermine the very premise of end-to-end encryption, which guarantees that only the sender and intended recipient can access message content.
The Vulnerability at the Heart of XChat: Key Storage
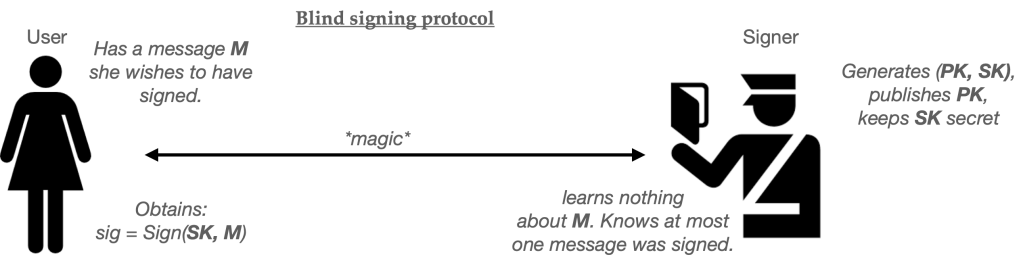
At the crux of the issue is how XChat handles decryption keys. According to analysis by cybersecurity experts, including a detailed post by Matthew Garrett, a significant weakness emerges from the system’s key storage approach. The decryption keys for XChat appear to be held on three servers that are not Hardware Security Modules (HSMs) and are entirely under X’s control. This centralized control raises immediate red flags.
"If decryption keys live in three non-HSM servers that are all under X’s control, then X could probably obtain anyone’s key and decrypt their messages," explained one security researcher, echoing sentiments prevalent in the technical community. This capability, they noted, could be exploited for various purposes, ranging from internal investigations driven by executive decisions to compliance with legal mandates such as warrants or subpoenas. In the context of end-to-end encryption, such a potential for a service provider to access user keys is considered a "game-over" vulnerability, effectively negating the intended privacy assurances.
The security of XChat, therefore, hinges critically on the security of the Juicebox implementation and the specific deployment choices made by X. Further investigation into Juicebox’s functionality and X’s operational practices has shed more light on these concerns.
Understanding Juicebox: A Solution to a Persistent Problem
Many end-to-end encrypted applications face a common hurdle: users are notoriously poor at securely storing their private cryptographic keys. This difficulty arises from various factors, including device loss, the proliferation of multiple devices, and the complexities of integrating secure key management into web browser environments.

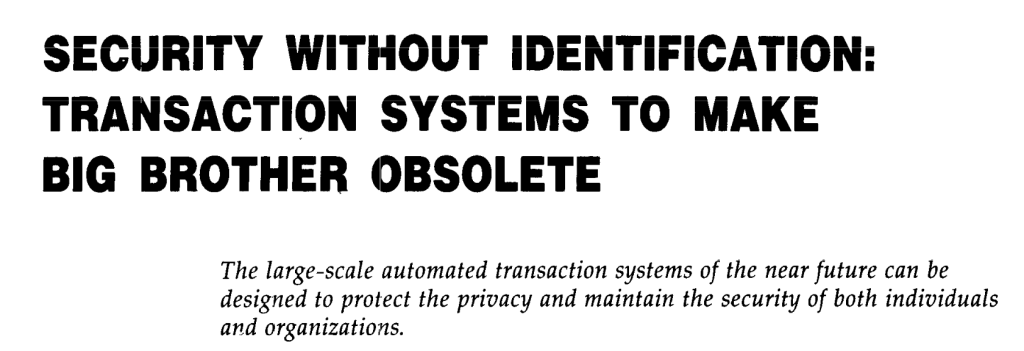
A seemingly straightforward solution – storing secret keys with the service provider – directly contradicts the fundamental principle of end-to-end encryption. The very essence of E2E encryption is to prevent service providers from accessing user secrets. Therefore, storing decryption keys in an accessible format on a provider’s servers is an unacceptable compromise for genuine privacy.
An alternative approach involves users encrypting their own secret keys and uploading the encrypted version to the service provider. However, this method introduces its own paradox: what key should be used to encrypt the secret key? This often leads to an "infinite pile of turtles," a recursive problem where each solution requires another, seemingly insurmountable, security measure.
The Role of PINs and Passwords in Key Management
Systems like Juicebox, Signal SVR, and Apple’s iCloud Key Vault attempt to circumvent this recursive problem by leveraging user-familiar credentials. Their observation is that while users struggle with complex cryptographic keys, they are more likely to remember simpler passwords or PINs, especially when prompted periodically. The proposed solution is to use a user’s PIN or password to encrypt the stronger cryptographic key that is then uploaded to the server.
However, this approach is not without its own limitations. Human-selected passwords and PINs often provide insufficient cryptographic strength. Short, numerical PINs, such as the six-digit codes common for phone passcodes, are particularly vulnerable to brute-force guessing attacks. A six-digit PIN offers at most 2^20 bits of security, a figure considered alarmingly low by cryptographic standards. Even with the use of robust key derivation functions like scrypt or Argon2, applied with extreme difficulty settings, the security of data remains precarious.
Towards Stronger Security: Password Hardening and Server Enforcement
A more robust solution to the weak secret problem involves a concept known as "password hardening." This process typically requires two key components. Firstly, a strong cryptographic secret is "mixed" with the user’s password to generate a truly formidable encryption key. Secondly, a mechanism is needed to limit the number of guessing attempts, thereby preventing attackers from mounting online brute-force attacks. This latter aspect cannot be enforced through cryptography alone; it necessitates a server (or servers) to enforce these limits. Critically, these servers must impose constraints on the number of incorrect password entries, such as locking an account or erasing associated data after a predetermined number of failed attempts.
This brings us back to the necessity of a server infrastructure. If this server is under the direct control of the service provider, they could potentially disable guessing limits or extract the server’s secret key material, thereby compromising the entire system.
To address this, many services have developed sophisticated solutions, often falling into one of two categories:

- Hardware Security Modules (HSMs): These are dedicated physical devices designed to securely generate, store, and manage cryptographic keys. Their tamper-resistant nature offers a higher level of security for sensitive key material.
- Distributed Trust: This involves distributing the operational responsibilities and trust across multiple, ideally mutually distrustful, entities. This prevents any single entity from having complete control or access to critical secrets.
X’s Juicebox Deployment: A Cause for Concern
Juicebox, in principle, is a software-based distributed key hardening service designed to operate across multiple servers. Users can "enroll" their accounts, and the Juicebox servers then transform their PIN/password into a strong cryptographic key by combining it with a secret stored on the Juicebox servers. Users can later retrieve this key by providing the correct password and adhering to guessing attempt limits. The system allows for specifying the number of servers (N) and a threshold (T), aiming to maintain security even if N-T servers are lost or unavailable, and if fewer than T servers are compromised. Crucially, Juicebox enforces limits on incorrect password entries, preventing brute-force attacks.
While Juicebox’s design allows for servers ("realms") to be either software-based or deployed within HSMs, the author’s understanding, as of the initial analysis, was that the HSM capability was not fully supported outside of a single test deployment and had not been implemented in deployments by X or elsewhere. This suggested that the security of XChat’s Juicebox implementation likely rested on the trustworthiness of the entities operating the servers.
The Crucial Question: Who Runs X’s Juicebox Servers, and Do They Use HSMs?
Based on initial observations, the prevailing assumption was that all XChat servers were run in software by X itself. This meant that the security of users’ secrets would be largely dependent on the internal security practices and trustworthiness of X’s server administrators. Without safeguards like verifiable HSM usage or the distribution of Juicebox servers across independently operated entities, having just three servers under X’s sole control offered minimal protection against the service operator itself.
Update on June 10th: A significant development emerged with a short conversation with an engineering lead at X. This individual claimed that some of the devices used at X are indeed utilizing HSMs for Juicebox. This statement, if accurate, suggests a departure from the initial assessment. However, the lack of public documentation or key ceremony ceremonies related to this purported HSM deployment has led to considerable skepticism within the security research community. Verifying such claims through public channels remains challenging, with the information currently limited to informal social media exchanges.
The absence of transparency regarding the use of HSMs and the key ceremonies involved is a point of contention. Security experts emphasize that even if X is implementing these advanced protections, doing so in secrecy is counterproductive to building trust. As a widely cited principle in security states: "If it’s not public, it doesn’t exist."
Further investigation into the Juicebox GitHub repository reveals both software-only and HSM-specific implementations of their "realms." A dedicated repository exists for supporting Juicebox on Entrust nShield Solo XC HSMs, complete with instructions and a "ceremony" document for administrators to certify correct setup and destruction of sensitive materials. However, according to Nora Trapp, the protocol designer for Juicebox, the project ceased active development over a year ago, and the existing code is open-source and not actively maintained.
Trapp’s analysis of XChat’s Juicebox deployment indicated that four realms are in use: realm-a.x.com, realm-b.x.com, realm-east1.x.com, and realm-west1.x.com. Timing analysis, particularly through the x-exec-time response header, suggests these realms are employing software-based HSMs. Real HSMs are generally known to be significantly slower, and even if actual HSMs were in use, the absence of published ceremonies means there is no verifiable basis to trust their security or to rule out key material exfiltration.

Trapp herself recently published a warning to deployers, advising against placing all servers under the control of a single service provider, a practice that appears to be followed by X. This advice directly addresses the core vulnerability identified in X’s current setup.
Given this information, the current advice to users remains cautious: assume the XChat Juicebox deployment is entirely software-based and that all Juicebox "realms" are operated by the same organization. Consequently, users should assume that their decryption keys could be recoverable by X’s server administrators with minimal difficulty, unless they employ an exceptionally strong password.
Deeper Dive into the Juicebox Protocol: Threshold OPRFs
For those interested beyond the immediate security posture of XChat, understanding the Juicebox protocol itself is beneficial. Assuming a scenario where a deployer has configured Juicebox intelligently—utilizing HSMs or distributing realms across multiple trust boundaries—the protocol offers significant cryptographic guarantees.
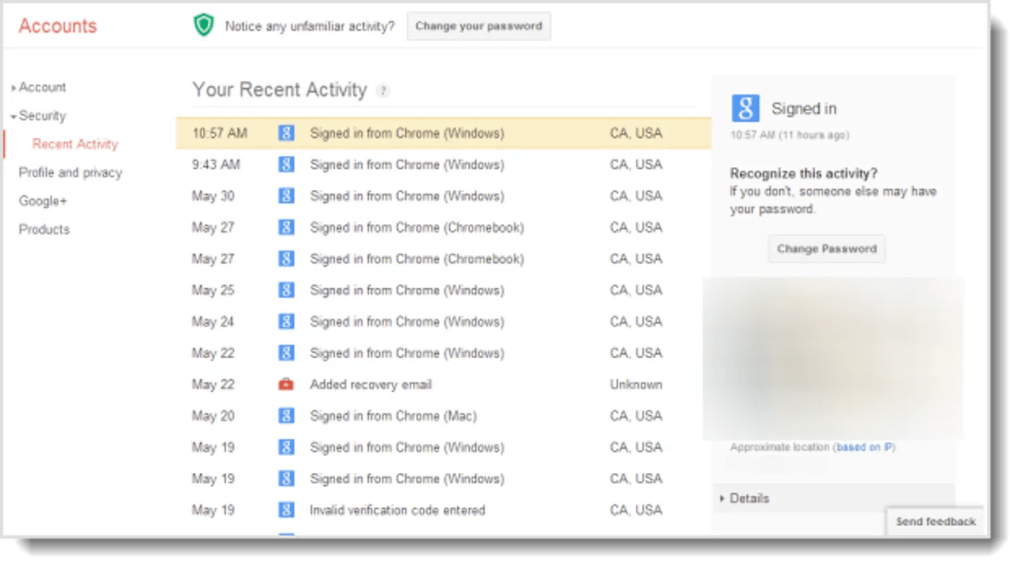
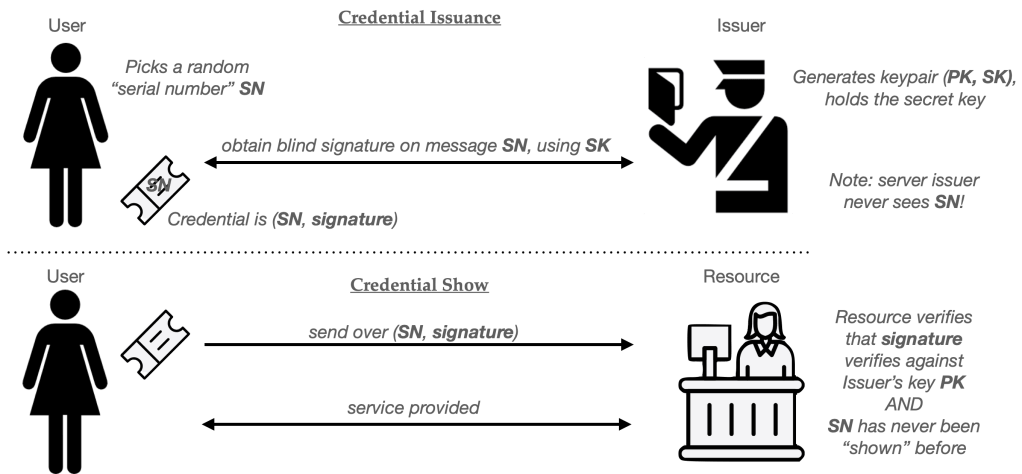
The core cryptographic primitive underpinning Juicebox is the "threshold oblivious pseudorandom function," or t-OPRF. OPRFs are functions that take a key K and a string P (such as a password) and output a pseudorandom string of bits, denoted as O = PRF(K, P). When an attacker does not know the key, the output O appears random, making it an excellent candidate for cryptographic keys.
An Oblivious PRF (OPRF) is a two-party cryptographic protocol enabling a client and server to jointly compute the output of a PRF without the server learning the client’s input. The protocol typically involves the client sending an encrypted version of its input to the server. The server then applies a pseudorandom function to this encrypted input and returns the result. The client can then decrypt this result to obtain the final pseudorandom output, while the server, due to the encryption, remains oblivious to the actual input.
This OPRF mechanism forms the basis of a simple password-hardening protocol. A server is configured with a unique key K for each user account. The client then runs the OPRF protocol with the server to compute O = PRF(K, P). This resulting value O serves as a robust encryption key for the client’s secrets. A key advantage is that the OPRF protocol ensures the server never learns the user’s password P, thus preventing information leakage even if the server is malicious.
Addressing Limitations: Guessing Limits and Distributed Servers
The basic OPRF design has limitations, primarily the inability of the server to enforce password guessing limits and the lack of support for distributing the process across multiple servers.

The guessing limit problem can be addressed by having the client compute an "authenticator tag" T derived from the secret O during the initial account registration. When the user logs back in, the client and server re-run the OPRF protocol. A verification process then checks if the obtained O is consistent with the stored tag T. If this verification fails, the server increments a counter for incorrect password guesses. A successful verification resets this counter to zero. Critically, when this counter reaches a predefined maximum (e.g., ten attempts), the server must lock the user’s account or, preferably, delete the account-specific key K, thereby thwarting systematic guessing attempts.
Distributing the PRF computation across multiple servers is achieved through threshold implementations. The specific OPRF used by Juicebox is based on elliptic curves, which are well-suited for threshold cryptography. This allows the service operator to split the key K across multiple servers, and a client can interact with any T of these servers to ultimately obtain PRF(K, P).
Client Proof of Key Possession and Potential Attacks
The "incorrect attempt" counters are a critical defense mechanism in systems like Juicebox. By limiting attackers to a fixed number of guesses, even relatively weak passwords can offer reasonable security. However, the entire system’s robustness hinges on these limits.
Assuming a scenario where the server operator is the attacker and has deployed Juicebox with protections like HSMs or distributed trust, several attack vectors can be considered. These attacks typically assume the server operator cannot directly access the secret key material. Given that the core principle of end-to-end encryption is to keep secret keys away from server operators, and considering governmental requests for backdoors into encrypted services, both hacking and legal compulsion are relevant threats.
Within this context, several attacks on systems like Juicebox can be envisioned:
- Side-Channel Attacks on Software Realms: If Juicebox realms are implemented purely in software, attackers could potentially exploit side-channel information leakage (e.g., timing, power consumption) to infer key material. However, this is highly dependent on the specific software implementation and the attacker’s capabilities.
- Credential Stuffing and Phishing: While not directly an attack on the Juicebox protocol itself, attackers could target users through credential stuffing (using leaked passwords from other breaches) or sophisticated phishing campaigns to obtain user passwords. If successful, these would allow them to bypass the Juicebox protections.
- Exploiting Trust in Software Realms: If all Juicebox realms are controlled by a single entity, and these realms are software-based, that entity could theoretically manipulate the software to disable guessing limits or extract keys. This highlights the critical importance of HSMs or distributed trust across independent operators.
A more theoretical, albeit illustrative, attack scenario involves a malicious (software) server operator attempting to exploit the protocol directly. In this hypothetical attack, a user who has previously registered their key with legitimate, potentially HSM-based, servers might have their login requests intercepted and redirected to a new set of malicious servers set up by an attacker using software. If the attacker configures these malicious servers with identical "realm IDs" to the legitimate ones, the "unlockKeyTag" computed by the client for the malicious server would be identical to the tag that would have been used by the real HSM-based server. Upon receiving this stolen tag, the attacker could then make an unlimited number of guesses against the HSM server associated with that realm ID, effectively resetting its counter indefinitely. While practical implementation challenges make this specific attack less likely, it underscores the delicate nature of distributed protocols and the potential for assumptions to be invalidated.
Implications for XChat Users
The ongoing scrutiny of XChat’s security architecture underscores a critical point for users: the promise of end-to-end encryption is only as strong as its weakest link. In XChat’s case, the primary concern revolves around the management and protection of cryptographic keys. Until X provides verifiable evidence of robust security measures, such as the exclusive use of tamper-resistant HSMs for all Juicebox realms and transparent key ceremony procedures, users should exercise caution. The current understanding suggests that X retains a significant level of access to user decryption keys, which fundamentally compromises the end-to-end encryption model. This situation, coupled with the potential for legal compulsion, means that users seeking true privacy on X’s platform may need to reconsider their choices or employ exceptionally strong, complex passwords as a primary line of defense. The broader implications for platform security and user trust in encrypted communication services remain a significant point of discussion.