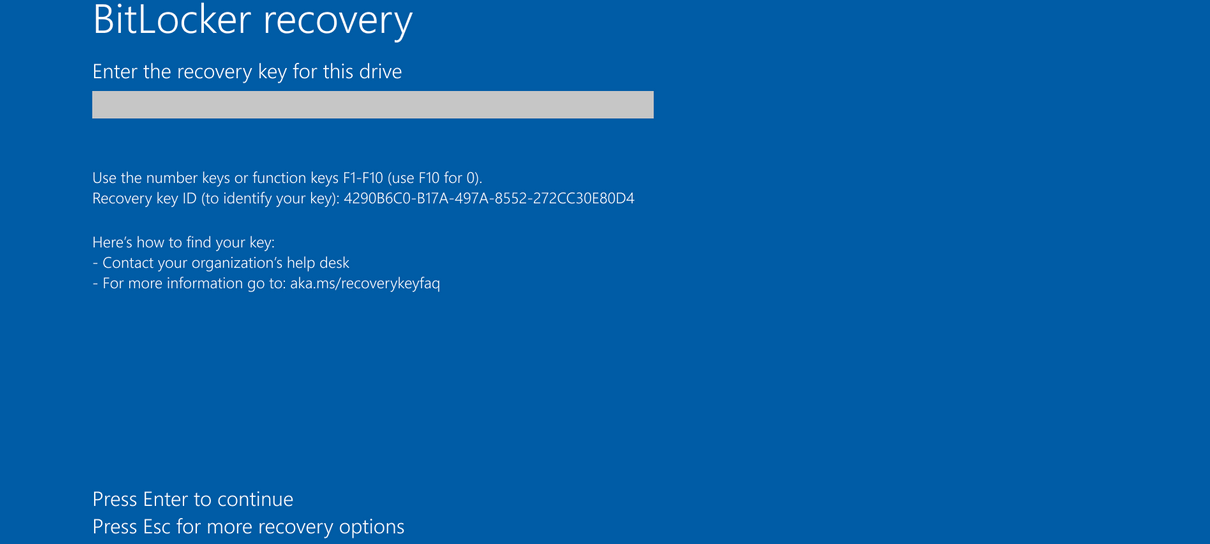
Microsoft has officially confirmed that a subset of Windows Server 2025 devices are encountering an unexpected boot into BitLocker recovery mode subsequent to the installation of the April 2026 security update, identified as KB5082063. The revelation, made public on Tuesday, signals a recurring challenge for enterprise IT administrators managing critical server infrastructure. This issue specifically impacts systems configured with certain Group Policy settings, necessitating immediate attention and adherence to Microsoft’s provided workarounds to prevent operational disruption.
Understanding BitLocker and its Role in Enterprise Security
BitLocker Drive Encryption is a fundamental security feature integrated into Microsoft Windows operating systems, designed to safeguard data by providing full-volume encryption. Its primary purpose is to protect sensitive information from unauthorized access, particularly in scenarios involving device theft, loss, or unauthorized tampering. When enabled, BitLocker encrypts the entire operating system drive and, optionally, fixed or removable data drives, rendering data unreadable without the correct decryption key. This is particularly crucial in enterprise environments where data privacy, regulatory compliance (such as GDPR, HIPAA, or CCPA), and intellectual property protection are paramount.
The mechanism relies heavily on hardware components, most notably the Trusted Platform Module (TPM). A TPM is a secure cryptoprocessor that stores encryption keys and validates the integrity of the boot process. If any unauthorized changes are detected in the boot environment—such as modifications to hardware, firmware, or specific software components—BitLocker will, as a security measure, prompt for a recovery key. This ensures that the system integrity is maintained and that data remains protected from tampering. Typically, users or administrators are required to input a lengthy recovery key, which is generated during BitLocker setup and ideally stored securely, often in an Azure Active Directory (AAD) or Active Directory (AD) environment for enterprise-managed devices. The average enterprise might manage thousands of BitLocker keys, making efficient retrieval critical during recovery events.
The current incident arises because the KB5082063 security update, intended to bolster system defenses, inadvertently triggers BitLocker’s recovery protocol on specific Windows Server 2025 configurations. Microsoft explicitly stated, "Some devices with an unrecommended BitLocker Group Policy configuration might be required to enter their BitLocker recovery key on the first restart after installing this update." This suggests a delicate interplay between the update’s changes and existing system configurations, particularly those managed through Group Policy. Group Policy is a powerful feature in Windows Server environments that allows administrators to define and control operating environments for users and computers, including critical security settings like BitLocker. An "unrecommended" configuration implies a deviation from best practices that, while perhaps functional under previous conditions, now clashes with changes introduced by the latest security patch. This highlights the inherent complexity of managing a diverse fleet of servers with potentially custom configurations.
Specific Conditions Leading to Recovery Mode
Microsoft has delineated the precise conditions under which Windows Server 2025 devices are susceptible to this BitLocker recovery loop. The issue manifests only when all the following criteria are met:
- Operating System: The device must be running Windows Server 2025. This indicates a targeted impact on the latest iteration of Microsoft’s server operating system, which is crucial for modern data centers, virtualized environments, and cloud infrastructures. Windows Server, with its estimated 70% market share in server operating systems, forms the backbone of countless global businesses.
- BitLocker Group Policy Configuration: The system must be utilizing a specific, "unrecommended" BitLocker Group Policy configuration. While the specific parameters of this "unrecommended" setting are not fully detailed in the initial alert, it is understood to pertain to how BitLocker bindings are configured to use the Platform Configuration Register 7 (PCR7) profile.
- PCR7 Profile: The BitLocker bindings must specifically use the PCR7 profile. PCR7 is a crucial component of the Trusted Platform Module (TPM) that measures the Secure Boot configuration and ensures the integrity of the boot process. When BitLocker is configured to rely on PCR7 for its integrity checks, any perceived change in this measurement—such as an update to the Boot Manager or other firmware components—can trigger the recovery mode. This is because BitLocker interprets the new PCR7 hash as a potential tampering event, even if it’s a legitimate system update.
- TPM Configuration: The underlying Trusted Platform Module (TPM) on the device must also align with conditions that make it vulnerable to this specific configuration conflict. This often involves specific TPM versions (e.g., TPM 1.2 vs. 2.0) or firmware states that interact unexpectedly with the update and the PCR7 configuration.
It is noteworthy that Microsoft reassures that "this known issue is unlikely to affect personal devices, as impacted configurations are typically found on systems managed by enterprise IT teams." This distinction is critical, highlighting the issue’s focus on complex, managed environments where custom Group Policies, specific hardware configurations, and advanced security settings are more prevalent. For an individual user, BitLocker is often configured automatically during Windows setup, using default, recommended settings that are less prone to such update-induced conflicts.
Operational Impact and IT Administrator Challenges
For enterprise IT teams, the prospect of servers booting into BitLocker recovery is a significant operational concern. Windows Server 2025 systems often host mission-critical applications, databases, virtualized environments, and core network services. Any unexpected downtime can lead to substantial financial losses, reputational damage, and disruption to business operations. According to industry estimates, the average cost of server downtime can range from hundreds to thousands of dollars per minute, escalating rapidly for critical systems. The requirement to manually enter a BitLocker recovery key, even if only once, presents several challenges:
- Downtime: Each affected server must be manually intervened with, causing unplanned downtime. In large enterprises with hundreds or thousands of servers, this can quickly scale into a massive operational burden, potentially affecting service level agreements (SLAs).
- Resource Allocation: IT staff must divert from other strategic projects or daily tasks to address this issue, consuming valuable time and resources. This often means delaying critical maintenance, security audits, or development work.
- Key Management: While enterprise environments typically have robust BitLocker key management systems (e.g., storing keys in Active Directory or Azure AD), retrieving and correctly entering keys for numerous servers can still be a cumbersome and error-prone process, especially under pressure.
- Patch Management Delays: The necessity to apply workarounds before installing the update, or to manage the recovery process afterward, can delay the deployment of essential security patches. This delay, in turn, can leave systems vulnerable to other threats that the KB5082063 update is designed to mitigate. This creates a dilemma for administrators: risk BitLocker recovery or risk exposure to other known vulnerabilities, a choice no IT professional wants to make.
Microsoft acknowledges the one-time nature of the recovery, stating, "In this scenario, the BitLocker recovery key only needs to be entered once — subsequent restarts will not trigger a BitLocker recovery screen, as long as the group policy configuration remains unchanged." While this provides some relief that the issue is not a persistent loop, the initial hurdle remains a significant operational challenge for maintaining system availability.

A Recurring Pattern: Chronology of Previous BitLocker Incidents
This is not an isolated incident but rather a recurring theme in Microsoft’s update history, highlighting the inherent complexity of managing full-disk encryption in conjunction with operating system updates. A brief chronology of similar BitLocker recovery issues underscores this pattern, indicating a systemic challenge in the interaction between OS updates, firmware, and encryption technologies:
- May 2025 (Windows 10 Emergency Updates): Just a year prior, Microsoft had to release emergency, out-of-band updates to address a similar problem. Windows 10 systems were widely reported to be booting into BitLocker recovery mode after installing the May 2025 security updates. This incident also caused significant disruption, prompting Microsoft to issue rapid patches to stabilize affected systems, showcasing the severity and widespread nature of such issues when they occur on client OS.
- August 2024 (All Supported Windows Versions): Earlier, in August 2024, another widespread issue emerged where BitLocker recovery prompts appeared across all supported Windows versions following the installation of the July 2024 Windows security updates. This problem necessitated a broader fix from Microsoft, indicating a vulnerability in the update deployment mechanism or BitLocker’s interaction with the core OS components across various versions, from client workstations to servers.
- August 2022 (KB5012170 Security Update): Further back, in August 2022, Windows devices faced widespread issues of becoming stuck at a BitLocker recovery prompt after installing the KB5012170 security update. This particular update was related to the Secure Boot DBX (Denied Boot Execution) revocation list, a critical component for maintaining the integrity of the boot process against malicious drivers and firmware. Changes to this list, while necessary for security, could inadvertently trigger BitLocker if not handled with extreme precision, as the perceived change in the boot environment would cause BitLocker to suspect tampering. This event notably affected both enterprise and some personal devices, leading to extensive community discussions and support requests.
The consistent recurrence of these issues points to the delicate balance Microsoft must maintain between enhancing security through updates and ensuring the stability of core features like BitLocker. Each incident provides valuable lessons, but the sheer complexity of the Windows ecosystem, with its myriad hardware configurations, firmware versions, and custom enterprise policies, makes achieving universal compatibility a formidable task. These events often highlight the critical need for comprehensive testing in diverse environments before public release, especially given the rapid pace of development and security threats.
Official Responses and Mitigations
In response to the current Windows Server 2025 issue, Microsoft has promptly acknowledged the problem and confirmed that a permanent solution is actively under development. In the interim, the company has provided crucial temporary workarounds for IT administrators to manage the installation of the KB5082063 security update without triggering BitLocker recovery. These workarounds are vital for maintaining operational continuity and ensuring the timely application of security patches.
Administrators are presented with two primary options:
- Pre-Installation Group Policy Adjustment: The recommended approach involves proactively removing the problematic Group Policy configuration before deploying the KB5082063 update. This preemptive measure aims to prevent the conflict from occurring altogether. Specifically, administrators are advised to ensure that BitLocker bindings are configured to correctly use the PCR7 profile. This often involves reviewing and adjusting BitLocker Group Policy settings related to "Configure TPM platform validation profile for native boot or fixed data drive" to align with recommended configurations. By ensuring the system’s BitLocker configuration aligns with the expected PCR7 profile prior to the update, the perceived change by BitLocker can be avoided. Microsoft has provided detailed steps for this process in its support documentation, accessible via the KB5082063 page, emphasizing the importance of precise execution and understanding of the specific GPO settings.
- Known Issue Rollback (KIR) Post-Installation: For scenarios where administrators cannot remove the PCR7 Group Policy before installation, or if the issue has already occurred, Microsoft offers the option to apply a Known Issue Rollback (KIR). A KIR is a mechanism Microsoft uses to quickly revert changes introduced by an update that cause unforeseen problems, without requiring a full patch rollback. In this context, applying the KIR to affected devices is designed to prevent the automatic switch to the 2023 Boot Manager, which is understood to be a key trigger for the BitLocker recovery in this specific scenario. By preventing this Boot Manager transition, the KIR avoids triggering BitLocker’s integrity check failure. This option provides a crucial safety net for organizations that may not have the luxury of pre-patching configuration changes or have already deployed the update and are now facing recovery prompts. KIRs are typically deployed via Group Policy or Microsoft Endpoint Manager, allowing for centralized management.
These proactive and reactive measures demonstrate Microsoft’s commitment to supporting its enterprise customers through complex update cycles. However, the need for such manual interventions underscores the inherent challenges in maintaining a vast and diverse ecosystem of operating systems and hardware.
Broader Implications for Enterprise Security and Patch Management
The recurring BitLocker recovery issues carry significant implications for enterprise security strategies and patch management protocols, resonating beyond just the immediate technical fix.
- Erosion of Trust in Updates: Each incident, particularly when affecting critical server infrastructure, can erode trust among IT professionals in the reliability of Microsoft’s security updates. While necessary for protection against ever-evolving cyber threats (with hundreds of vulnerabilities patched monthly), if updates frequently introduce stability issues, it can lead to delays in deployment as organizations become more cautious. This hesitancy can, paradoxically, increase the overall attack surface if critical vulnerabilities remain unpatched for longer periods, potentially exposing systems to ransomware or data breaches.
- Increased Operational Overhead: The need for manual workarounds, recovery key management, and potential system remediation adds considerable operational overhead to already strained IT departments. This diverts resources from strategic initiatives like cybersecurity enhancements, cloud migration, or digital transformation, pushing them back into reactive firefighting. This can lead to increased operational costs and a backlog of essential IT projects.
- Importance of Staging and Testing: These incidents strongly reinforce the critical importance of robust staging and testing environments within enterprises. Before deploying any security update to production servers, especially in complex environments like Windows Server 2025, organizations must conduct thorough testing on a representative subset of their infrastructure. This allows them to identify and mitigate potential conflicts, such as the BitLocker recovery issue, in a controlled setting before they impact live services. Industry best practices suggest a multi-stage deployment process, starting with a small pilot group, then a larger test group, before widespread deployment.
- Data Integrity and Availability: While BitLocker is a data protection feature, an unintended recovery state can lead to temporary data unavailability. For organizations dependent on continuous access to their server data, this can translate into significant business disruption. The balance between data security (encryption) and data availability (uptime) is a constant challenge for IT architects, and such incidents push the scales towards availability concerns.
- Vendor Communication and Transparency: Microsoft’s prompt communication and provision of workarounds are positive steps. Continued transparency regarding the root causes of these recurring issues and detailed guidance for prevention will be crucial for rebuilding and maintaining confidence among its enterprise user base. Clear, timely, and actionable advice is paramount for IT professionals navigating complex patch cycles.
In conclusion, while the April 2026 KB5082063 security update for Windows Server 2025 is vital for patching vulnerabilities, its unintended consequence of triggering BitLocker recovery on specific configurations highlights the intricate challenges of modern operating system maintenance. Microsoft’s ongoing efforts to provide solutions and workarounds are essential, but the broader impact underscores the critical need for meticulous patch management strategies, comprehensive testing, and a deep understanding of BitLocker’s interaction with the underlying system architecture within every enterprise environment. The recurring nature of these incidents serves as a powerful reminder of the delicate balance between security enhancement and operational stability in the ever-evolving landscape of enterprise IT.