Stryker, a preeminent global medical technology company headquartered in Kalamazoo, Michigan, has been crippled by a sophisticated data-wiping cyberattack, with an Iran-linked hacktivist group named Handala (also known as Handala Hack Team) claiming responsibility. The extensive digital assault has led to widespread operational disruptions, forcing the closure of offices across numerous countries, sending thousands of employees home, and sparking significant concerns about the stability of vital medical supply chains worldwide. This incident underscores the escalating threat of state-sponsored cyber warfare impacting critical infrastructure and the global economy.
The Cyberattack Unfolds: Stryker’s Operational Halt
Reports emerging early Wednesday detailed the immediate and severe impact on Stryker’s vast global operations. In Ireland, home to Stryker’s largest hub outside the United States and employing over 5,000 individuals, workers were instructed to return home as systems went offline. The disruption was so profound that staff reportedly resorted to using WhatsApp for updates on when they might be able to resume work. An anonymous employee quoted by the Irish Examiner highlighted the comprehensive nature of the attack, stating, "anyone with Microsoft Outlook on their personal phones had their devices wiped." Furthermore, login pages on company devices were reportedly defaced with the distinctive Handala logo, serving as a stark digital calling card from the perpetrators.
Concurrently, a voicemail message at Stryker’s main U.S. headquarters indicated a "building emergency," a euphemism often employed by corporations to describe significant IT outages that render physical premises inoperable. These initial reports painted a picture of a company struggling to maintain basic functionality, with network-connected systems largely inaccessible or compromised. Stryker, a titan in the medical and surgical equipment manufacturing sector, reported a staggering $25 billion in global sales last year and boasts a workforce of 56,000 employees across 61 countries, making the scale of this disruption truly monumental.
Handala’s Claim and Retaliatory Motivation
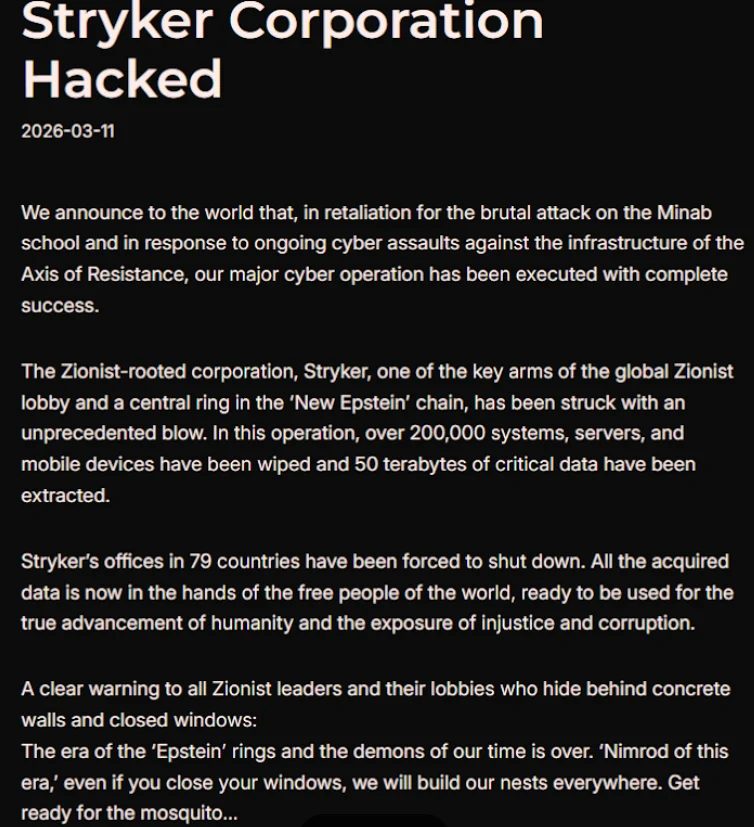
The hacktivist group Handala took to Telegram to publicly assert its responsibility for the attack, issuing a lengthy statement that detailed the alleged scope and motivation behind their actions. Handala claimed to have forced the shutdown of Stryker’s offices in an astounding 79 countries, asserting that data had been irrevocably erased from more than 200,000 systems, servers, and mobile devices. The group’s manifesto declared, "All the acquired data is now in the hands of the free people of the world, ready to be used for the true advancement of humanity and the exposure of injustice and corruption."
The stated primary motivation for this devastating cyberattack was direct retaliation for a missile strike on February 28 that targeted an Iranian school, resulting in the tragic deaths of at least 175 people, many of whom were children. The New York Times reported today that an ongoing military investigation has determined the United States to be responsible for this deadly Tomahawk missile strike. Handala explicitly referenced Stryker as a "Zionist-rooted corporation" in its manifesto, a designation that intelligence analysts suggest could be linked to Stryker’s 2019 acquisition of OrthoSpace, an Israeli medical technology company specializing in rotator cuff repair. This connection highlights the geopolitical undercurrents driving the attack, extending beyond the immediate missile strike to broader regional conflicts.
The Attribution: Handala’s Link to Iran’s Intelligence Apparatus
The identification of Handala as the perpetrator immediately raised red flags among cybersecurity experts, as the group has been extensively profiled by leading intelligence firms. Palo Alto Networks, a prominent cybersecurity company, recently highlighted Handala as one of several hacker groups with demonstrable links to Iran’s Ministry of Intelligence and Security (MOIS). According to Palo Alto’s analysis, Handala first surfaced in late 2023 and is assessed to be one of multiple online personas maintained by Void Manticore, a known MOIS-affiliated actor. This direct connection to a state intelligence agency elevates the incident from a mere hacktivist stunt to a potentially state-sponsored act of cyber warfare, carrying significant international implications.
Palo Alto Networks’ research indicates that Handala’s hack-and-leak activities primarily target Israeli entities, though the group occasionally expands its scope when specific agendas are served. Previous attacks attributed to Handala include those against fuel systems in Jordan and an Israeli energy exploration company. The security firm characterizes Handala’s recent observed activities as "opportunistic and ‘quick and dirty,’" often focusing on exploiting supply-chain footholds—such as IT or service providers—to reach downstream victims. These operations are typically followed by "proof" posts designed to amplify credibility and intimidate targets, a tactic clearly demonstrated by the Telegram manifesto and the defaced login screens observed at Stryker.
Technical Modus Operandi: The "Wiper" Mechanism and Intune Exploitation
While data-wiping attacks typically involve malicious software designed to systematically overwrite existing data on infected devices, the Stryker incident appears to have leveraged a more insidious method. A trusted source with intimate knowledge of the attack, speaking anonymously to KrebsOnSecurity, indicated that the perpetrators exploited a legitimate Microsoft service known as Microsoft Intune to issue a "remote wipe" command against all connected devices.
Microsoft Intune is a cloud-based solution designed for IT teams to manage and secure endpoints, enforce security and data compliance policies, and monitor and control devices from a single, web-based administrative console, regardless of their physical location. The apparent misuse of such a powerful administrative tool is particularly alarming. Evidence supporting the Intune connection surfaced in a Reddit discussion among individuals claiming to be Stryker employees, who reported being urgently instructed to uninstall Intune from their devices. This suggests that the attackers either gained highly privileged access to Stryker’s Intune management console or exploited a vulnerability within the system itself, turning an essential enterprise management tool into a weapon for mass data destruction. The ability to remotely wipe devices globally through a legitimate management platform signifies a profound breach of administrative control and highlights a critical vulnerability in modern enterprise security architecture.
Broader Impact and Implications for Healthcare and Cybersecurity
The cyberattack on Stryker is not merely an isolated corporate incident; it has immediate and far-reaching implications for the global healthcare sector. Stryker is a major supplier of essential medical devices, surgical instruments, and technologies that are indispensable for hospitals and healthcare providers worldwide. The disruption has already begun to manifest as a "real-world supply chain attack," according to an anonymous healthcare professional at a major university medical system in the United States. This expert emphasized the pervasive reliance on Stryker’s products, stating, "Pretty much every hospital in the U.S. that performs surgeries uses their supplies." The inability to order surgical supplies directly impacts patient care, potentially delaying critical procedures and straining already fragile healthcare systems.
The American Hospital Association (AHA) acknowledged awareness of the attack, with John Riggi, national advisor for the AHA, stating that they are "actively exchanging information with the hospital field and the federal government to understand the nature of the threat and assess any impact to hospital operations." While Riggi noted that as of now, they were not aware of "any direct impacts or disruptions to U.S. hospitals," he cautioned that this assessment could change as hospitals evaluate services, technology, and supply chains related to Stryker, especially if the duration of the attack extends. This cautious optimism underscores the latent but significant threat to healthcare continuity.
Further evidence of the immediate impact emerged from a March 11 memo issued by the state of Maryland’s Institute for Emergency Medical Services Systems. The memo indicated that Stryker reported a "global network disruption" and, in response, several hospitals opted to disconnect from Stryker’s various online services. Notably, this included LifeNet, a critical platform that allows paramedics to transmit electrocardiograms (EKGs) to emergency physicians, thereby enabling expedited treatment for heart attack patients upon arrival at the hospital. Timothy Chizmar, Maryland’s EMS medical director, advised that while Maryland Medical Protocols for EMS require ECG transmission for acute coronary syndrome patients, if transmission is impossible, paramedics should initiate radio consultation to describe ECG findings. This workaround, while necessary, highlights a downgrade in immediate patient care capabilities due to the cyber incident.
Geopolitical Cyber Warfare and Critical Infrastructure Vulnerability
This incident serves as a stark reminder of the increasing intersection of geopolitical tensions and cyber warfare, with critical civilian infrastructure often becoming collateral damage or direct targets. The targeting of a medical technology company, regardless of its perceived "Zionist roots," raises ethical concerns about attacks that could ultimately harm patients globally. The use of a data-wiping attack, designed for maximum destruction and disruption rather than data exfiltration for financial gain, further emphasizes the retaliatory and punitive nature of Handala’s actions.
The attack also brings to the forefront the vulnerability of complex global supply chains. When a single, foundational supplier like Stryker is incapacitated, the ripple effects can be felt across an entire industry, affecting millions of end-users. For the healthcare sector, this translates directly into potential impacts on patient safety and public health. The incident necessitates a deeper re-evaluation of cybersecurity strategies within critical infrastructure sectors, emphasizing not only defensive measures but also robust incident response plans and resilient supply chain alternatives.
Lessons and Future Outlook
The Stryker cyberattack offers several critical lessons for organizations worldwide. Firstly, the exploitation of legitimate IT management tools like Microsoft Intune for malicious purposes highlights the need for stringent access controls, multi-factor authentication, and continuous monitoring of administrative accounts. Insider threat prevention and the principle of least privilege are more vital than ever. Secondly, the incident underscores the importance of supply chain cybersecurity; companies must not only secure their own networks but also assess and mitigate risks associated with their vendors and partners. Finally, the event illustrates the evolving landscape of cyber threats, where politically motivated hacktivist groups, often state-sponsored, are increasingly capable of launching highly destructive attacks against targets perceived as aligned with adversary nations.
As this remains a developing story, the full extent of the damage to Stryker, its financial implications, and the long-term impact on the global healthcare supply chain are yet to be fully realized. The company faces a monumental task of recovery, including restoring systems, potentially rebuilding data, and regaining the trust of its customers and the broader medical community. This incident will undoubtedly serve as a case study in the escalating and dangerous world of state-backed cyber warfare.
Update, 2:54 p.m. ET: Added comment from John Riggi of the American Hospital Association (AHA) and expanded on perspectives regarding the attack’s potential to evolve into a significant supply-chain problem for the healthcare system.
Update, Mar. 12, 7:59 a.m. ET: Incorporated information about the outage affecting Stryker’s critical online services, specifically LifeNet, and the resulting guidance from the Maryland Institute for Emergency Medical Services Systems.