A Brazilian technology firm specializing in safeguarding networks from distributed denial-of-service (DDoS) attacks has been found to be inadvertently or complicitly enabling a powerful botnet, an investigation by KrebsOnSecurity has revealed. This botnet has been responsible for an extensive campaign of massive DDoS attacks targeting other network operators within Brazil. The company at the center of these allegations, Huge Networks, through its chief executive, Erick Nascimento, contends that the malicious activity stems from a sophisticated security breach and is likely the calculated work of a competitor aiming to tarnish the company’s public image and operational integrity.
For several years, cybersecurity experts have meticulously tracked a series of large-scale DDoS attacks originating from Brazil, exclusively directed at Brazilian Internet Service Providers (ISPs). The precise origins and orchestrators of these digital sieges remained largely elusive until earlier this month. The breakthrough occurred when a trusted, anonymous source shared a highly revealing file archive, which had been inadvertently exposed in an open online directory.
The Unveiling of the Botnet’s Infrastructure
The exposed archive proved to be a treasure trove of incriminating evidence. It contained several malicious programs, written in Python and primarily in Portuguese, alongside the private SSH authentication keys belonging to Erick Nascimento, the CEO of Huge Networks. This discovery immediately raised serious questions, as Huge Networks is a prominent Brazilian ISP that primarily offers advanced DDoS protection services to other network operators across the country.
Founded in Miami, Florida, in 2014, Huge Networks has strategically centered its operational footprint in Brazil. The company initially built its reputation by protecting game servers from the relentless onslaught of DDoS attacks, a common tactic in the competitive online gaming landscape. Over time, it evolved into a specialized DDoS mitigation provider catering specifically to ISPs. Prior to this revelation, Huge Networks maintained an outwardly pristine record, appearing in no public abuse complaints and showing no discernible association with any known DDoS-for-hire services, which are often the architects of such destructive campaigns. This clean public image now stands in stark contrast to the findings within the exposed archive.
Nevertheless, the contents of the archive painted a disturbing picture, indicating that a Brazil-based threat actor had maintained root access to Huge Networks’ infrastructure. This access was leveraged to construct and operate a powerful DDoS botnet. The method involved routinely mass-scanning the Internet for vulnerable devices, specifically insecure Internet routers and unmanaged Domain Name System (DNS) servers that could be enlisted and weaponized in these attacks.
Dissecting the Attack Mechanism: DNS Reflection and Amplification
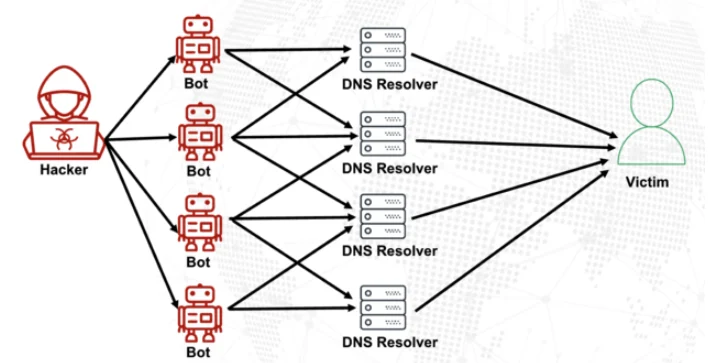
To understand the potency of the botnet, it’s crucial to grasp the mechanics of the attacks it facilitated. DNS is a foundational Internet protocol that translates human-readable domain names (like "google.com") into machine-readable IP addresses, allowing users to access websites. Ideally, DNS servers are configured to respond only to queries originating from within their trusted domain or from authorized clients. However, "DNS reflection" attacks exploit misconfigured DNS servers that are left open to accept queries from any source on the Internet.
In a DNS reflection attack, the attacker sends spoofed DNS queries to these open servers. The crucial element here is "spoofed": the source IP address of the query is falsified to appear as if it originated from the target’s network, rather than the actual attacker’s location. Consequently, when the misconfigured DNS servers respond to these queries, they send their replies directly to the spoofed, targeted address, effectively flooding the victim’s network with unwanted traffic.
The efficacy of these attacks is further magnified by a technique known as "DNS amplification." This relies on an extension to the DNS protocol that enables the transmission of significantly larger DNS messages. Botmasters meticulously craft DNS queries such that the responses they elicit are dramatically larger than the initial requests. For instance, an attacker might send a DNS request less than 100 bytes in size, which could provoke a response 60-70 times larger. This amplification effect becomes particularly devastating when perpetrators can simultaneously query tens of thousands of compromised devices, each sending spoofed requests to numerous open DNS servers. The cumulative effect is an overwhelming torrent of data directed at the target, capable of knocking even robust networks offline. The sheer volume generated by these attacks can overwhelm network infrastructure, causing legitimate traffic to be dropped and services to become unavailable, resulting in significant financial losses and reputational damage for targeted organizations.
The Botnet’s Construction and Targets
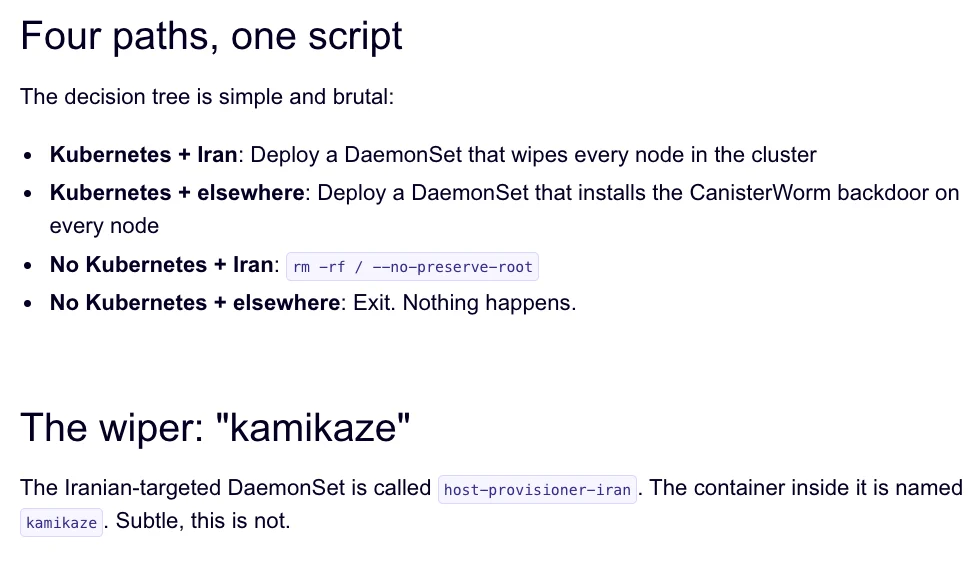
The exposed file archive offered an unparalleled glimpse into the botnet’s operational blueprint, including a command-line history detailing precisely how the attacker built and maintained this powerful network. The logs revealed a systematic process of scouring the Internet for vulnerable TP-Link Archer AX21 routers. Specifically, the botnet sought out TP-Link devices that remained susceptible to CVE-2023-1389, an unauthenticated command injection vulnerability that TP-Link had patched back in April 2023. The continued prevalence of unpatched devices provided a fertile ground for the botnet’s expansion, highlighting the persistent challenge of patch management across the vast landscape of IoT devices globally. Many users neglect firmware updates, leaving their devices open to known exploits long after patches are released.
Further analysis of the malicious Python attack scripts within the archive uncovered DNS lookups for domains such as hikylover[.]st and c.loyaltyservices[.]lol. Both of these domains have been flagged by cybersecurity researchers over the past year as command-and-control (C2) servers for an Internet of Things (IoT) botnet powered by a variant of the notorious Mirai malware. This connection immediately linked the ongoing Brazilian attacks to a lineage of highly destructive botnets, known for their ability to compromise a wide array of insecure smart devices and turn them into attack vectors.
The leaked archive further indicated that the botmaster coordinated their scanning activities from a Digital Ocean server, an IP address that has been flagged for abusive activity hundreds of times over the past year by various cybersecurity platforms. The Python scripts explicitly invoked multiple Internet addresses assigned to Huge Networks, which were then used to identify specific targets and execute the DDoS campaigns. The attacks were meticulously confined to Brazilian IP address ranges, suggesting a localized agenda. The scripts showed a rapid-fire attack pattern: each selected IP address prefix was assaulted for a duration of 10 to 60 seconds, employing four parallel processes per host, before the botnet swiftly moved on to the next target. This dynamic and aggressive targeting strategy is characteristic of sophisticated, rapid-cycling DDoS operations designed to overwhelm and bypass conventional defenses, making detection and mitigation challenging for smaller ISPs.

Crucially, the archive irrefutably demonstrated that these malicious Python scripts relied on private SSH keys belonging to Huge Networks’ CEO, Erick Nascimento. When confronted with these findings by KrebsOnSecurity, Mr. Nascimento emphatically denied authoring the attack programs. He stated that he was unaware of the full extent of the DDoS campaigns until he was contacted directly by the investigative journalists. "We received and notified many Tier 1 upstreams regarding very very large DDoS attacks against small ISPs," Nascimento recounted. "We didn’t dig deep enough at the time, and what you sent makes that clear." His statement suggests a lack of granular insight into the origin of attacks even when Huge Networks was involved in their mitigation, which raises questions about their internal monitoring capabilities.
CEO’s Defense and Internal Breach Allegations
Nascimento offered an explanation, attributing the unauthorized activity to a digital intrusion first detected in January 2026. This breach, he claimed, compromised two of the company’s development servers, along with his personal SSH keys. However, he maintained there was no evidence that these compromised keys were utilized after January. "We notified the team in writing the same day, wiped the boxes, and rotated keys," Nascimento stated, providing a screenshot of a January 11 notification from Digital Ocean as corroborating evidence. He added, "All documented internally." The timeline provided by Nascimento would imply that the malicious activity, if it occurred using these keys, would have had to happen before or immediately after January 11th, yet the archive suggests ongoing operations.
Further elaborating on the supposed breach, Mr. Nascimento asserted that Huge Networks has since enlisted a third-party network forensics firm to conduct a comprehensive investigation. "Our working assessment so far is that this all started with a single internal compromise — one pivot point that gave the attacker downstream access to some resources, including a legacy personal droplet of mine," he explained. A "droplet" refers to a virtual private server instance offered by Digital Ocean, often used for development or testing.
Nascimento clarified the nature of the initial compromise: "The compromise happened through a bastion/jump server that several people had access to." He continued, "Digital Ocean flagged the droplet on January 11 — compromised due to a leaked SSH key, in their wording — I was traveling at the time and addressed it on return. That droplet was deprecated and destroyed, and it was never part of Huge Networks infrastructure." This narrative attempts to distance the compromised assets from the core operational infrastructure of Huge Networks, framing it as an isolated incident involving a legacy, personal, and ultimately decommissioned resource. However, the direct use of his private SSH keys and Huge Networks’ IP addresses in the botnet operations, as indicated by the exposed archive, raises critical questions about the thoroughness of the remediation or the precise timeline of events, and whether the compromise was fully contained as asserted.
The Shadow of Mirai: A History of Exploitation
The malicious software powering the botnet of TP-Link devices used in the DDoS attacks on Brazilian ISPs is undeniably based on Mirai, a malware strain with a notorious history. Mirai first burst onto the scene in September 2016, launching what was then a record-shattering DDoS attack that kept KrebsOnSecurity’s website offline for four days. The unprecedented scale of that attack brought the vulnerability of IoT devices to the forefront of cybersecurity concerns, highlighting how easily insecure consumer electronics could be weaponized. In January 2017, KrebsOnSecurity’s investigation successfully identified the Mirai authors as the co-owners of a DDoS mitigation firm. Disturbingly, this firm was found to be leveraging the very botnet it created to attack gaming servers, effectively generating business by creating the problems it claimed to solve. This historical precedent adds a layer of scrutiny to the current allegations against Huge Networks, a firm operating in a similar niche.
The threat of Mirai resurfaced dramatically in May 2025 when KrebsOnSecurity was hit by another Mirai-based DDoS attack. This particular incident was so immense that Google, which was mitigating the attack, described it as the largest it had ever handled, reaching an astonishing 6.3 terabits per second (Tbps). That subsequent report implicated a young Brazilian man, then in his twenties, who was simultaneously operating a DDoS mitigation company and several DDoS-for-hire services. These services have since been seized by the FBI, underscoring the lucrative and illicit synergy between offering "protection" and orchestrating attacks. This pattern of behavior within the DDoS mitigation industry, particularly in Brazil, creates a challenging environment for distinguishing between legitimate service providers and those who may exploit vulnerabilities for financial gain, making trust a paramount but often fragile commodity.
Nascimento vehemently denied any involvement in launching DDoS attacks against Brazilian operators to drum up business for Huge Networks’ services. "We don’t run DDoS attacks against Brazilian operators to sell protection," Nascimento asserted in his written response. "Our sales model is mostly inbound and through channel integrator, distributors, partners — not active prospecting based on market incidents. The targets in the scripts you received are small regional providers, the vast majority of which are neither in our customer base nor in our commercial pipeline — a fact verifiable through public sources like QRator." This defense aims to decouple the botnet’s activities from Huge Networks’ commercial interests, arguing that the attack targets are not potential clients and therefore the motive for generating business by creating incidents is absent.
Allegations of Competitor Sabotage and Broader Implications
Adding another layer of intrigue to the unfolding narrative, Nascimento maintains he possesses "strong evidence stored on the blockchain" that this entire ordeal was orchestrated by a competitor. However, he declined to name this competitor, citing strategic reasons. "I would love to share this with you, but it could not be published as it would lose the surprise factor against my dishonest competitor," he explained. The CEO further hinted at a specific timeline: "Coincidentally or not, your contact happened a week before an important event — one that this competitor has NEVER participated in (and it’s a traditional event in the sector). And this year, they will be participating. Strange, isn’t it?" This statement suggests a deliberate timing to undermine Huge Networks’ standing, potentially before a significant industry gathering, raising the specter of corporate cyber warfare.
The implications of these findings are substantial, both for Huge Networks and the broader cybersecurity landscape in Brazil. For Huge Networks, the revelations undoubtedly cast a long shadow over its reputation and the trust it has built within the industry. Despite the CEO’s claims of a breach and competitor sabotage, the direct link of his SSH keys and Huge Networks’ IP addresses to the botnet operations necessitates a thorough and transparent investigation. The company’s future hinges on its ability to convincingly demonstrate that it was a victim, rather than an unwitting or complicit enabler, of these destructive attacks. Without clear, verifiable evidence, the perception of impropriety could severely impact its client base and market standing.
More broadly, this incident underscores the persistent vulnerabilities within the global Internet infrastructure. The widespread presence of unpatched IoT devices, such as the TP-Link Archer AX21 routers vulnerable to CVE-2023-1389, provides readily exploitable resources for botnet operators. Similarly, misconfigured DNS servers continue to be a significant enabler of large-scale reflection and amplification attacks. The case also highlights the inherent challenges in the competitive cybersecurity market, where the line between protection and exploitation can sometimes appear blurred, especially when malicious actors may pose as legitimate service providers. This complex environment demands increased vigilance from both industry players and regulators.
The allegations of competitor sabotage, while unproven, introduce a complex dynamic, suggesting that cybersecurity itself can be weaponized in commercial rivalries. If true, it would represent a concerning escalation in business espionage, where a company’s own infrastructure is compromised and used to attack others, then framed to discredit the victim. This scenario underscores the critical need for robust internal security practices, even for companies whose core business is security. Regular audits, stringent access controls, immediate key rotation post-compromise, and continuous monitoring are paramount to prevent such incidents, or at least to provide irrefutable evidence of victimhood. The lack of detailed, public evidence for Nascimento’s blockchain claim adds to the uncertainty surrounding this aspect of the case.
As the investigation by the third-party forensics firm proceeds, the cybersecurity community will be watching closely. The outcome will not only determine the fate of Huge Networks but could also set precedents for how similar incidents are understood and addressed in an increasingly complex and interconnected digital world, particularly in regions like Brazil that have historically been hotspots for DDoS activity and the rise of sophisticated botnets. The "surprise factor" promised by Nascimento regarding his competitor remains to be seen, but the current revelations have already delivered a significant shock to the Brazilian tech sector, emphasizing the constant need for vigilance and accountability in the digital realm.