The hack of the Solana-essentially essentially based decentralized finance (DeFi) platform Drift Protocol could well were prevented if customary operational safety procedures were followed by the Drift group of workers, and could well well constitute “civil negligence,” in step with attorney Ariel Givner.
“In terrifying terms, civil negligence formulation they failed their frequent duty to defend the cash they were managing,” Givner said in step with the autopsy change provided by the Drift group of workers and the plot it handled Wednesday’s $280 million exploit.
The Drift group of workers did now not discover “frequent” safety procedures, in conjunction with maintaining signing keys on separate, “air-gapped” systems which can be never out of date for developer work, and conducting due diligence on blockchain developers met through industry conferences.
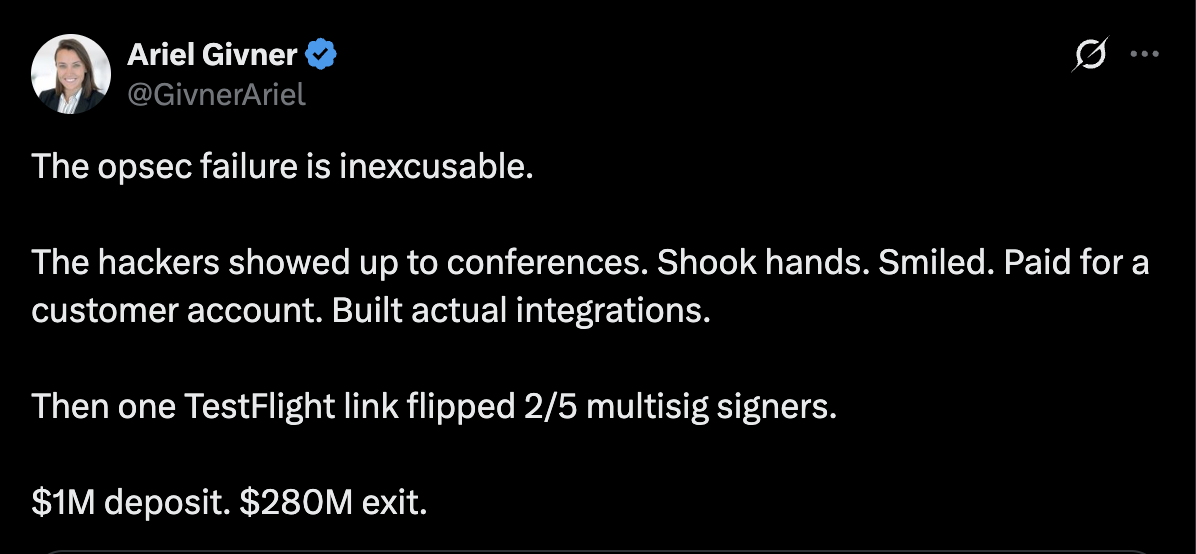
“Each and every serious mission is conscious of this. Drift didn’t discover it,” she said, in conjunction with, “They knew crypto is filled with hackers, especially North Korean order groups.” Givner persisted:
“But their group of workers spent months chatting on Telegram, assembly strangers at conferences, opening sketchy code repos, and downloading spurious apps on devices tied to multisignature controls.”
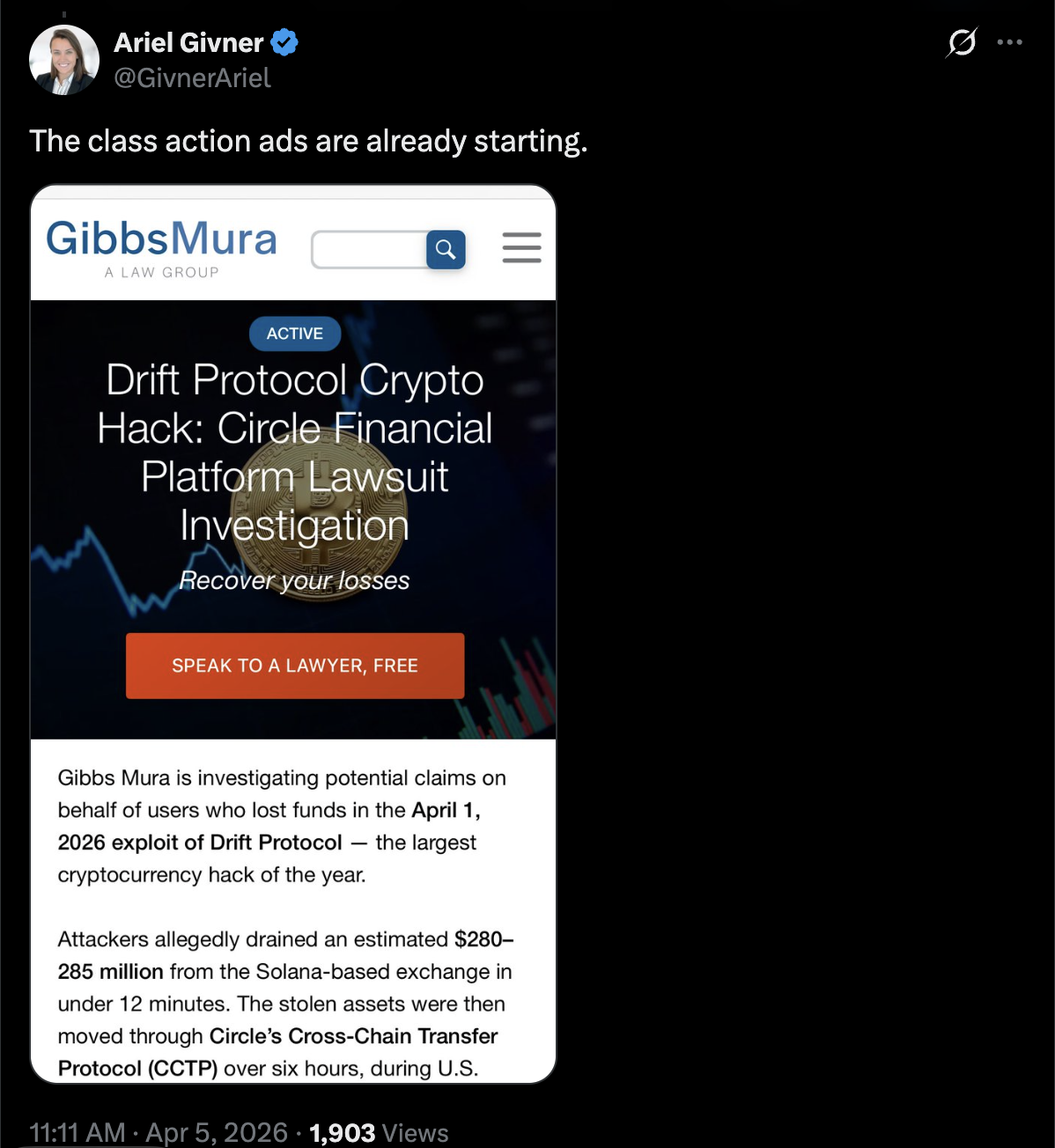
Advertisements for sophistication motion complaints towards Drift Protocol are already circulating, she said. Cointelegraph reached out to the Drift Team but did no longer receive a response by the level of e-newsletter.
The incident is a reminder that social engineering and mission infiltration by malicious actors are vital attack vectors for cryptocurrency developers that would drain person funds and completely erode customer belief in compromised platforms.
Related: Drift explains $280M exploit as critics ask Circle over USDC freeze
Drift Protocol says attack took “months” of planning
The Drift Protocol group of workers revealed an change on Saturday outlining how the exploit occurred and claimed that the attackers deliberate the attack for six months sooner than execution.
Menace actors first approached the Drift group of workers at a “vital” crypto industry convention in October 2025, expressing passion in protocol integrations and collaboration.
The malicious actors persisted to dangle rapport with the Drift constructing group of workers in the following six months, and once sufficient belief modified into once constructed, they began sending the Drift group of workers malicious hyperlinks and embedding malware that compromised developer machines.
These other folks, who are suspected of working for North Korea order-affiliated hackers and physically approached the Drift developers, were no longer North Korean nationals, in step with the Drift group of workers.
Drift said, with “medium-high confidence,” that the exploit modified into once applied by the the same actors in the wait on of the October 2024 Comely Capital hack.
In December 2024, Comely Capital said the exploit modified into once applied through malware sent through Telegram from a North Korea-aligned hacker posing as an ex-contractor.
Magazine: Meet the hackers who could well lend a hand receive your crypto lifestyles financial savings wait on

