In a significant stride towards enhancing device security at its most fundamental levels, Google has announced the successful integration of a Rust-based Domain Name System (DNS) parser directly into the modem firmware of its latest Pixel 10 devices. This pioneering move marks the first instance of a memory-safe language being deployed within a Pixel device’s modem, underscoring Google’s unwavering commitment to mitigating a pervasive class of software vulnerabilities and solidifying the security posture of its flagship smartphones. The initiative is a cornerstone of Google’s broader strategy to embed memory-safe code deeper into its hardware and software ecosystems, promising a more resilient and secure mobile experience for users.
A New Frontier in Mobile Security: The Pixel 10 and Rust
The announcement, made on April 14, 2026, details a critical advancement in mobile security, specifically targeting the cellular baseband modem—a component often considered a lucrative target for sophisticated attackers due to its privileged access and complex processing of network communications. Jiacheng Lu, a software engineer with the Google Pixel Team, articulated the profound impact of this integration, stating, "The new Rust-based DNS parser significantly reduces our security risk by mitigating an entire class of vulnerabilities in a risky area, while also laying the foundation for broader adoption of memory-safe code in other areas." This statement highlights not only the immediate benefits for the Pixel 10 but also signals a strategic direction for future Pixel device security enhancements and potentially, the wider Android ecosystem.
The Pixel 10, by becoming the inaugural Pixel device to incorporate a memory-safe language into its modem, sets a new benchmark for device security. This development is particularly noteworthy because the modem operates at a very low level, directly interacting with cellular networks. Vulnerabilities at this layer can have severe consequences, potentially leading to remote code execution, data interception, or complete device compromise without user interaction. By replacing traditionally C/C++ based components with Rust, Google aims to eliminate a significant percentage of these critical vulnerabilities at their source.
Understanding the Pervasive Threat of Memory Safety Vulnerabilities
To fully appreciate the significance of Google’s move, it’s essential to understand the nature of memory safety vulnerabilities. For decades, programming languages like C and C++ have been the backbone of operating systems, drivers, and firmware due to their performance and low-level control. However, this control comes at a cost: manual memory management. This often leads to common programming errors such as buffer overflows, use-after-free bugs, and double-free errors. These "memory unsafety" bugs are not merely theoretical; they consistently rank among the most exploited vulnerabilities by malicious actors.
Industry reports consistently corroborate the severity of this issue. For instance, studies from Microsoft and Google have repeatedly shown that a substantial majority—often cited as around 70%—of critical security vulnerabilities discovered in their products are memory-safety related. These statistics underscore a systemic problem that traditional defensive measures, while important, often struggle to fully contain. Exploitation of such flaws can grant attackers arbitrary code execution, enabling them to bypass security mechanisms, elevate privileges, and compromise entire systems. In the context of a smartphone modem, this could mean an attacker gaining control over cellular communications, tracking a user’s location, or even installing persistent malware.
Google’s Steadfast Commitment to Memory Safety: A Chronology
The integration of Rust into the Pixel 10 modem is not an isolated event but rather the culmination of a multi-year, multi-pronged strategy by Google to systematically address memory safety across its product portfolio. This chronology demonstrates a deliberate and escalating commitment:

-
Late 2023: Clang Sanitizers for Baseband Hardening: Google began publicly detailing its efforts to harden the cellular baseband modem against exploitation. A key initiative involved the extensive use of Clang sanitizers, such as Overflow Sanitizer (IntSan) and BoundsSanitizer (BoundSan). These tools are designed to catch undefined behavior, including various memory errors, during program execution. By instrumenting code with these sanitizers, developers can detect and fix bugs that might otherwise lead to exploitable vulnerabilities. This proactive debugging approach significantly improved the quality and security of the C/C++ codebase within the modem.
-
Late 2024: Android 14’s Modem Security Features: Building on previous efforts, Android 14 introduced a suite of new security measures specifically aimed at combatting advanced threats like 2G exploits and baseband attacks. Google detailed various architectural and firmware-level enhancements designed to prevent attackers from leveraging memory-safety vulnerabilities, such as buffer overflows, to achieve remote code execution within the modem. These included stricter memory isolation, improved privilege separation, and enhanced input validation mechanisms, creating multiple layers of defense.
-
Throughout 2024-2025: Broad Rust Adoption Across Android and Firmware: Concurrently with its modem-specific hardening, Google embarked on a strategic shift towards Rust across its broader Android operating system and other low-level firmware components. This initiative gained significant momentum, with reports in September 2024 highlighting how Google’s shift to Rust programming was already yielding tangible benefits, including a reduction in security bugs. This systematic adoption across various layers of the software stack demonstrated Google’s belief in Rust as a long-term solution for memory safety.
-
November 2025: Tangible Results in Android Vulnerability Reduction: The impact of this broader Rust adoption became quantifiable in November 2025, when Google revealed a significant milestone: the number of memory safety vulnerabilities discovered in the Android mobile operating system had fallen below 20% of the total vulnerabilities identified in the preceding year. This dramatic reduction from the historical 70% figure served as powerful empirical evidence of Rust’s effectiveness and solidified Google’s resolve to expand its use.
The integration of the Rust-based DNS parser into the Pixel 10’s modem firmware in April 2026 is therefore the natural progression of this well-defined security roadmap. It represents Google’s commitment to applying proven memory-safety principles to one of the most critical and historically vulnerable components of a modern smartphone.
The Strategic Choice: DNS and the Modem Firmware
Google’s decision to specifically target the DNS protocol for its initial Rust implementation within the modem firmware was highly strategic. The Domain Name System is an absolutely foundational component of modern internet communication, translating human-readable domain names (like google.com) into machine-readable IP addresses. In the context of cellular technology, as Google noted, "With the evolution of cellular technology, modern cellular communications have migrated to digital data networks; consequently, even basic operations such as call forwarding rely on DNS services." This means the DNS parser within the modem is constantly active, processing network requests that are essential for almost every cellular function, from voice calls (VoLTE) to data connectivity and messaging.
This pervasive reliance makes the DNS parser a high-value target. When implemented in memory-unsafe languages like C/C++, vulnerabilities in DNS parsers can expose users to significant risks. An example cited by Google, CVE-2024-27227, demonstrates how out-of-bound memory accesses in a DNS-related component can lead to severe security flaws. Exploiting such a vulnerability could allow an attacker to craft malicious DNS responses that, when processed by a vulnerable parser, could trigger memory corruption, leading to a denial-of-service, information leakage, or even remote code execution. By reimplementing this critical component in Rust, Google directly confronts and "decreases the attack surfaces associated with memory unsafety."
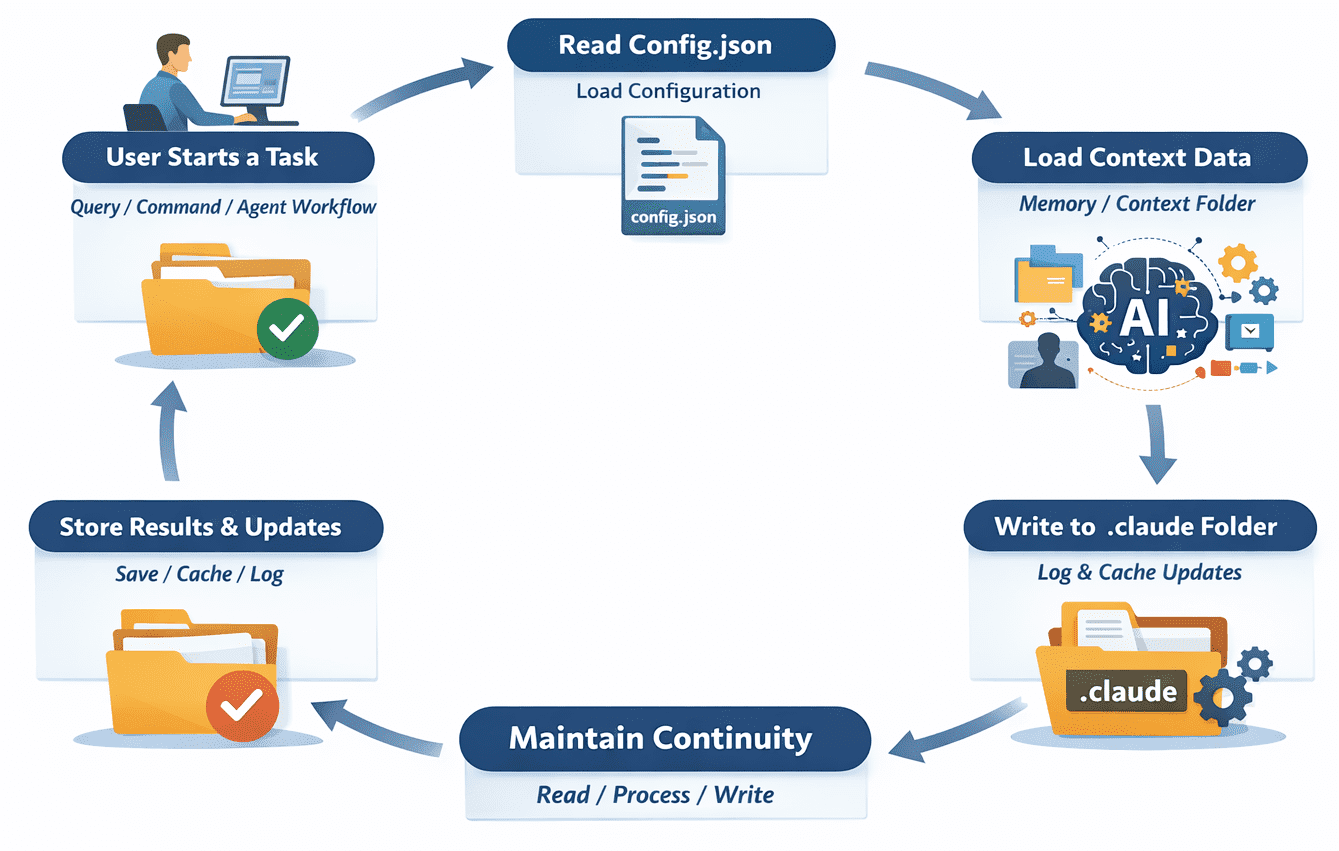
Technical Deep Dive: Hickory-Proto and Cargo-Gnaw
To bring this vision to fruition, Google leveraged existing, robust Rust infrastructure. They opted for the "hickory-proto" crate, a well-regarded Rust-based DNS client, server, and resolver library. The choice of an established, open-source crate allowed Google to benefit from community-vetted code, though modifications were necessary to adapt it for the highly constrained "bare metal" and embedded environments typical of modem firmware. These modifications likely involved optimizing for minimal memory footprint, strict real-time requirements, and integration with the existing C codebase.

A significant challenge in integrating Rust libraries into such environments, especially those with numerous dependencies, is managing the build process and ensuring a minimal final binary size. To address this, Google developed and utilized a custom tool called "cargo-gnaw." This tool is crucial for easily resolving and maintaining the more than 30 dependencies introduced by the hickory-proto crate. cargo-gnaw likely streamlines the dependency management, ensures consistent builds, and potentially helps in optimizing the final compiled code for size and performance, which are paramount in embedded systems.
Despite these efforts, Google acknowledged that the hickory-proto crate was not initially optimized for memory-constrained systems. They noted that future code size optimizations could be achieved by adding extra feature flags. These flags would enable modularity, allowing developers to selectively compile only the required functionality from the crate, thereby reducing the final binary size and memory footprint. This iterative optimization process is typical in embedded development and signifies ongoing refinement.
The C-Rust Interoperability Challenge
One of the most intricate aspects of this integration involved ensuring seamless interoperability between the new Rust code and the vast, pre-existing C codebase of the modem firmware. Google detailed their approach: "For the DNS parser, we declared the DNS response parsing API in C and then implemented the same API in Rust." This technique, often referred to as a Foreign Function Interface (FFI), allows code written in one language to call functions implemented in another. The Rust function returns an integer error code, signaling success or failure to the C caller.
Furthermore, the received DNS answers, once parsed by the Rust component, "are required to be updated to in-memory data structures that are coupled with the original C implementation." This necessitates calling back into existing C functions from the Rust implementation to populate the data structures that the rest of the C-based modem firmware relies upon. This bidirectional communication is a testament to the flexibility of Rust’s FFI capabilities and Google’s engineering prowess in bridging two distinct programming paradigms within a single, highly critical system. It ensures that the memory-safe benefits of Rust can be introduced incrementally without necessitating a complete rewrite of the entire modem firmware, which would be an enormous and potentially destabilizing undertaking.
Broader Industry Impact and Implications
Google’s integration of Rust into the Pixel 10 modem firmware carries significant implications for the broader mobile security landscape and the tech industry at large:
- Setting an Industry Precedent: As a major technology leader, Google’s move is likely to inspire other device manufacturers and chipmakers to explore and adopt memory-safe languages like Rust for critical firmware components. This could accelerate a shift away from C/C++ in new development for sensitive areas, leading to a general uplift in device security across the industry.
- Enhanced User Trust and Security: For Pixel users, this translates directly into a more secure device. By reducing the attack surface at such a foundational level, Google is proactively protecting users from a wide array of sophisticated network-based attacks that might otherwise compromise their privacy and data. This builds greater trust in the Pixel brand’s security promises.
- Validation of Rust’s Enterprise Readiness: This high-profile deployment in a consumer device’s core firmware further validates Rust’s capabilities for mission-critical, high-assurance systems. It demonstrates that Rust is not just a language for web services or developer tools but is robust enough for bare-metal, embedded programming where performance, reliability, and security are paramount. This could spur further investment and adoption of Rust in other sensitive domains like automotive, aerospace, and industrial control systems.
- Challenges and Future Directions: While a significant achievement, the integration also highlights ongoing challenges. Optimizing Rust code for extreme memory constraints and seamlessly integrating it with legacy C/C++ codebases remains a complex engineering task. Google’s mention of future optimizations through feature flags suggests that the journey towards pervasive memory safety in embedded systems is iterative. Future developments might include further Rustification of other modem components, or even the development of entirely new modem firmware written predominantly in Rust.
Conclusion
The integration of a Rust-based DNS parser into the Pixel 10’s modem firmware is a landmark achievement in mobile security. It represents a proactive and strategic response to the enduring threat of memory safety vulnerabilities, leveraging the unique strengths of Rust to harden one of the most critical components of a smartphone. This move not only fortifies the security of Pixel devices but also sets a powerful precedent for the entire industry, signaling a decisive shift towards memory-safe languages in the development of foundational software and firmware. As the digital threat landscape continues to evolve, Google’s commitment to foundational security through innovations like Rust integration will be crucial in building a more resilient and trustworthy mobile ecosystem for everyone.