This is the second in a series of posts about anonymous credentials, continuing our exploration of technologies that enable privacy-preserving authentication. In the preceding installment, we established the foundational concept of anonymous credentials, a cryptographic mechanism allowing users to interact with online services without divulging personally identifiable information. This subsequent article delves into the practical engineering aspects of these systems, examining a prominent real-world implementation and its far-reaching impact.
At its core, an anonymous credential system involves several key actors: an Issuer, responsible for generating and distributing credentials; one or more Resources (such as websites or applications) that require authentication; and numerous Users seeking to access these resources. The Issuer typically verifies a user’s identity through a traditional, non-anonymous process to grant them a credential. Subsequently, the user can present this credential to a Resource. The critical innovation lies in the "presentation" or "showing" of this credential; when implemented correctly, this process should be unlinkable to the specific credential issued to the user, thereby safeguarding their privacy from both the Resource and potentially the Issuer. Key features desirable in such systems include unlinkability, which prevents the association of different credential presentations by the same user; unforgeability, ensuring that only the Issuer can create valid credentials; and anonymity, protecting the user’s identity.
Moving beyond theoretical underpinnings, this analysis focuses on two significant real-world credential systems: Privacy Pass, a widely adopted standard, and a nascent proposal for anonymous age verification spearheaded by Google.
Privacy Pass: The Ubiquitous Digital Wristband
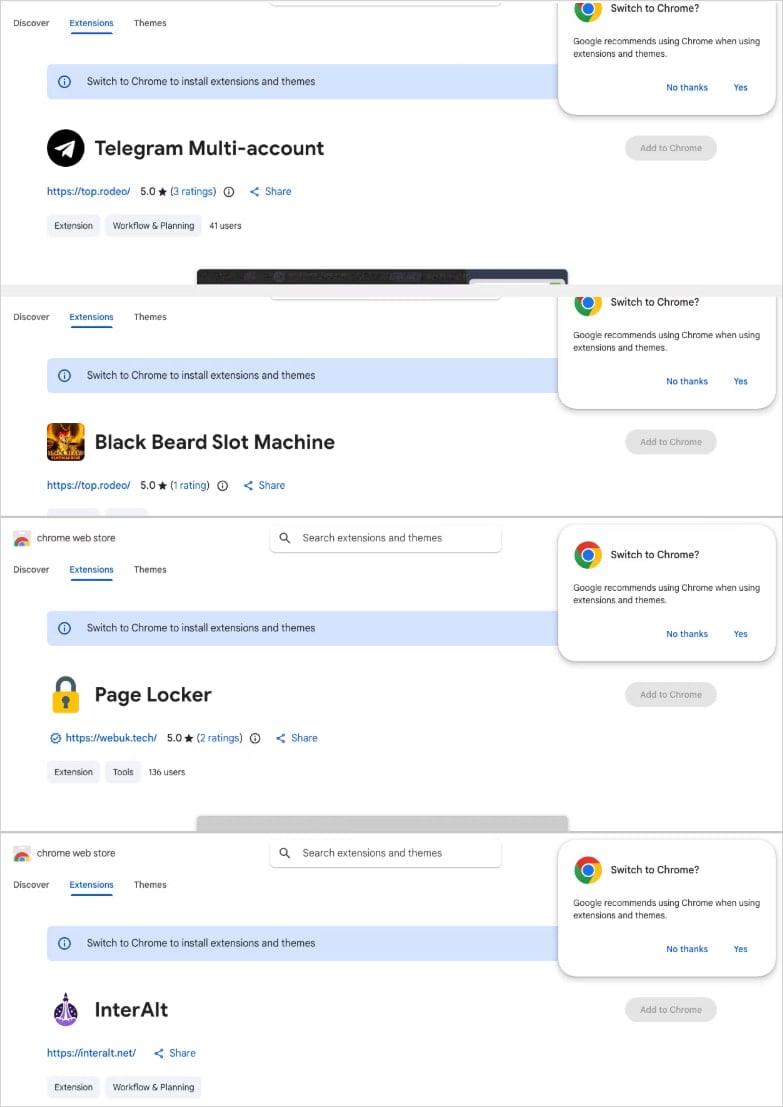
Privacy Pass stands as the most extensively deployed anonymous credential standard globally. Its influence is pervasive across the internet, primarily leveraged by major technology corporations. Cloudflare, a leading content delivery network and security provider, has been a significant proponent, with its researchers playing a crucial role in developing the standard as a solution to mitigate the friction caused by CAPTCHAs and other anti-abuse measures. The protocol, or functionally identical variants, is also implemented by tech giants such as Apple, which refers to it as "Private Access Tokens," and Google, under the umbrella of "Private State Tokens." Other notable adopters include the Brave browser and a host of other projects. The widespread adoption of Privacy Pass is so profound that even Microsoft has integrated it into its Edge browser, underscoring its de facto status as an internet standard, despite potential philosophical differences regarding privacy emphasis.
Privacy Pass embodies the expected characteristics of a large-scale credential deployment: remarkable simplicity. The protocol essentially offers single-use "wristband" credentials, akin to a digital token signifying "I have been verified." The underlying cryptographic techniques are rooted in foundational research from the 1980s, augmented with sophisticated performance optimizations. The true innovation lies not in groundbreaking theoretical novelty but in its successful and widespread practical application.
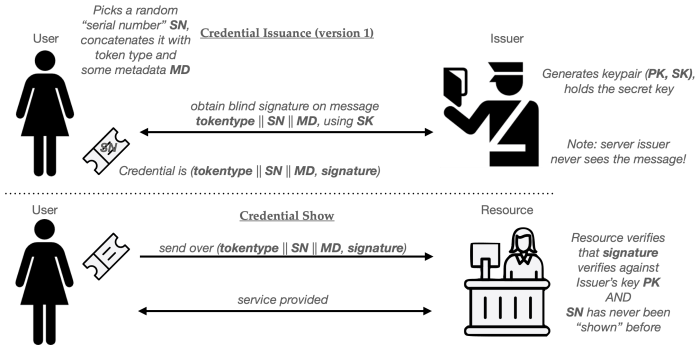
The technical specifications for Privacy Pass are codified in Internet Engineering Task Force (IETF) Request for Comments (RFCs) 9576, 9577, and 9578. While these standards offer various deployment configurations, the core protocol is a near-perfect realization of David Chaum’s seminal "blind signature" credentials, concepts we explored in the previous installment. The process can be broadly understood as follows:
- Issuance: A user, after being authenticated by an Issuer, requests a credential. The user "blinds" the token, a cryptographic operation that obscures the actual token data from the Issuer. The Issuer then signs this blinded token. Crucially, due to the blinding process, the Issuer cannot later identify which specific token they signed.
- Redemption: The user unblinds the signed token, yielding a valid, anonymous credential. This credential is a four-tuple: (tokentype, MD, SN, sig). The
tokentypespecifies the protocol variant,MDis metadata,SNis a serial number or identifier, andsigis the cryptographic signature from the Issuer. - Presentation: To access a Resource, the user presents this credential. The Resource verifies the signature using the Issuer’s public key and checks the
tokentypeandSN. TheMDfield can be used to bind the credential to a specific context, such as a particular website or a time window.
This basic flow, visualized as a pictogram, illustrates the user’s journey from obtaining a credential to presenting it anonymously.

The Role of Metadata (MD) in Privacy Pass
A key component of the Privacy Pass credential is the MD (metadata) field. This string serves as a flexible mechanism to "bind" a credential to a specific application or context. For instance, a user intending to access the New York Times on a particular date could request a credential with MD set to "nyt.com || 2026-03-31." When presented to the New York Times, the website can verify this metadata string to ensure the credential is appropriate for its service.
Critically, the Issuer does not have visibility into this metadata during the signing process. The User has the agency to select and bind the metadata, but once chosen, it cannot be altered. This feature empowers Resources to enforce granular policies, requiring tokens that are specific to their domain or limited by temporal constraints, thereby enhancing security and preventing the misuse of credentials across different services or timeframes.
A particularly innovative application of this metadata is the implementation of "session-specific credentials." In this issuance flow, the user obtains the credential not before, but rather after initiating a session with a Resource, such as a Cloudflare-protected website. This real-time issuance protocol operates as follows:
- Session Initiation: The User begins to access a Resource.
- Challenge and Blinded Request: The Resource issues a challenge. The User responds with a blinded token request, incorporating relevant session information into the metadata.
- Issuance and Verification: The Resource forwards the blinded request to the Issuer. The Issuer signs the blinded request and returns it to the Resource. The Resource then unblinds the signature, verifies it, and forwards the resulting credential to the User.
- Credential Presentation: The User now possesses a credential specifically tied to that session, which they can use for further authentication or to bypass subsequent challenges within that session.
This session-specific flow, depicted in a pictogram, offers a tightly coupled authentication mechanism. The primary advantage is that each credential is inherently bound to the specific session for which it was issued. This prevents users from stockpiling credentials for future use, a feature that could be advantageous for services like Cloudflare, where real-time control over user access is paramount.
However, this real-time issuance model introduces certain drawbacks. Firstly, it necessitates the continuous availability of the Issuer. If the Issuer becomes unavailable, users are unable to obtain fresh credentials, potentially leading to widespread service disruption. This contrasts with the pre-issuance model, where users can accumulate credentials for later use, even if the Issuer is offline. Secondly, the real-time issuance protocol is susceptible to "timing correlation attacks." In such an attack, the Resource and Issuer could compare the timestamps of their respective messages. If these timestamps are sufficiently close, it might be possible to infer a link between a user’s session and their credential issuance request.
This latter concern is particularly acute when the Issuer and Resource are operated by the same entity, as is the case with Cloudflare’s deployment. While Cloudflare processes an immense volume of transactions—hundreds of thousands per second—making such correlation attacks theoretically challenging, it remains a potential vulnerability. Preliminary analyses, including informal assessments using AI code generation tools, have yielded mixed results regarding the feasibility of such attacks in this specific context.
Cryptographic Underpinnings: Signature Schemes and Token Types
A fundamental question in understanding Privacy Pass revolves around the specific blind signature schemes employed and the nature of the "token types." Privacy Pass defines two standardized "issuance protocols" that utilize distinct cryptographic approaches.
The first protocol supports publicly verifiable tokens. These align closely with the Chaumian credentials previously discussed. Here, the Issuer employs blind RSA signatures to authenticate tokens, mirroring Chaum’s original 1980s protocol. A significant benefit of these tokens is that the Resource can verify them using the Issuer’s public key. This eliminates the need for the Issuer and Resource to share any secret cryptographic material, enhancing security and simplifying key management.
However, RSA blind signatures present certain challenges. They tend to produce large signatures and are computationally somewhat expensive to generate. RSA requires substantial public key sizes, typically a minimum of 2,048 bits, to achieve adequate security levels (around 112-bit symmetric-equivalent security). This results in relatively large signatures and a more demanding signing process.
The theoretical alternative would involve employing elliptic-curve (EC) cryptography, such as Schnorr signatures or ECDSA. However, the practical landscape for EC-based blind signatures is less mature. Existing schemes often suffer from issues such as complexity, lack of widespread standardization, or limited compatibility with the full range of desired features. Consequently, Privacy Pass currently does not natively support elliptic-curve-based blind signatures.
For deployments prioritizing extreme speed, Privacy Pass introduces a second issuance protocol for privately verifiable tokens. These tokens leverage an oblivious Message Authentication Code (MAC) built upon an oblivious pseudorandom function. The advantage of these tokens lies in their reliance on EC-based primitives, leading to exceptionally fast creation and verification processes. The primary disadvantage, however, is that the verifier (the Resource) must possess the Issuer’s secret key to validate a credential. This introduces a tighter coupling and a potential security risk if the secret key is compromised.
Conclusion: A Foundation for Future Privacy Technologies
Privacy Pass represents a pragmatic and highly successful implementation of anonymous credential technology. It offers users a straightforward, single-use "wristband" credential optimized for speed and efficiency. While the foundational concepts date back to the 1980s, the protocol has been standardized and engineered for contemporary web environments, achieving remarkable speed and usability. Its significance lies less in its theoretical novelty and more in its unprecedented scale of deployment. With endorsements from industry leaders like Apple, Google, and Cloudflare, it is estimated that billions of individuals interact with Privacy Pass daily, often without their explicit awareness.
Despite its widespread success, Privacy Pass is, by design, a relatively simple system. It primarily facilitates the "get token, use token" model of wristband credentials and offers limited advanced features. Consequently, it falls short of providing comprehensive solutions for complex challenges like age verification, unless a constant, real-time interaction with an Issuer is envisioned for every web service access.
The subsequent installment in this series will pivot to a more sophisticated proposal: Google’s initiative to standardize zero-knowledge credentials. This emerging technology promises to address some of the limitations of current systems, particularly in the realm of privacy-preserving age assurance, by leveraging advanced cryptographic techniques such as zero-knowledge proofs.