Kamerin Stokes, a 23-year-old from Memphis, Tennessee, has been sentenced to 30 months in federal prison for his involvement in a sophisticated cybercrime operation that compromised tens of thousands of DraftKings accounts. The sentencing, which includes three years of supervised release, $1,327,061 in restitution, and $125,965.53 in forfeiture, underscores the severe legal consequences awaiting individuals who exploit digital vulnerabilities for illicit financial gain. Stokes’ case is particularly notable for his audacious decision to relaunch his criminal enterprise under the tagline "fraud is fun" even after pleading guilty and being released on pretrial supervision, citing the need to pay his legal fees.
The Anatomy of a Credential-Stuffing Attack: The November 2022 DraftKings Breach
The roots of Stokes’ conviction trace back to a massive credential-stuffing attack that rocked DraftKings in November 2022, ultimately compromising nearly 68,000 user accounts. Credential stuffing is a pervasive cyberattack technique where threat actors leverage lists of username and password combinations, typically stolen in previous data breaches from unrelated websites, to gain unauthorized access to accounts on other online services. The effectiveness of this method hinges on the common user practice of reusing the same login credentials across multiple platforms. Cybercriminals exploit this human vulnerability, knowing that if a user’s credentials are leaked from one site, they are likely to work on others.
In this particular incident, the primary architects of the attack were identified as Nathan Austad, known online as "Snoopy," and Joseph Garrison, a third accomplice who was separately charged in May 2023. These individuals systematically tested credentials obtained from various prior breaches against DraftKings’ systems. Once access was gained, the perpetrators would exploit the accounts by adding new payment methods, typically making a small deposit (often $5) to verify the new method, and then swiftly withdrawing all available funds from the compromised accounts. This method allowed them to siphon approximately $635,000 from around 1,600 individual accounts, directly impacting the victims’ finances.

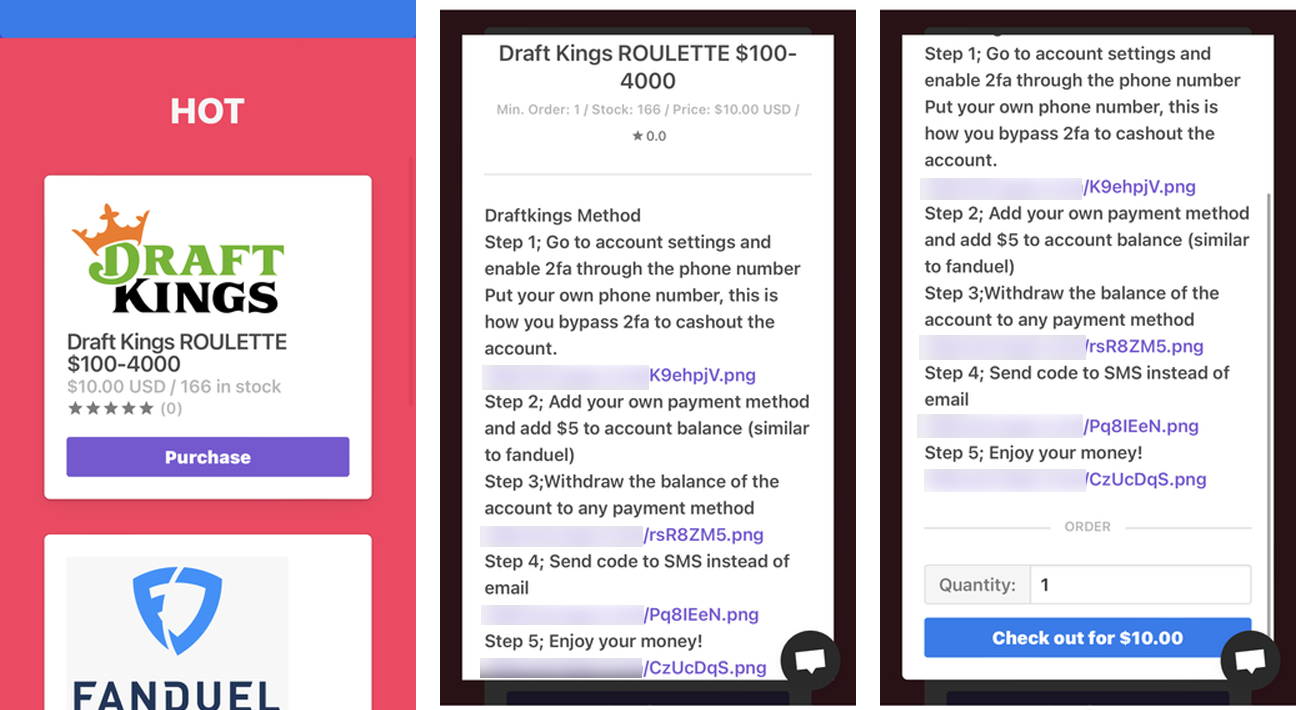
The illicit market for these compromised accounts proved to be highly lucrative. Austad and Garrison reportedly generated over $2.1 million by selling access to not only DraftKings accounts but also those belonging to FanDuel, another major online sports betting platform, and even Chick-fil-A, highlighting the diverse targets of such credential-stuffing operations. Kamerin Stokes, operating under the online moniker "TheMFNPlug," served as a key reseller in this network. He purchased bulk access to these hijacked accounts from Austad and Garrison and then resold them through his own digital "shop," further expanding the reach and profitability of the criminal enterprise.
A Timeline of Deception, Discovery, and Justice
The chronology of events reveals a rapid sequence from initial breach to eventual prosecution:
- November 2022: The credential-stuffing attack against DraftKings accounts commences. Threat actors, including Austad and Garrison, gain unauthorized access to nearly 68,000 accounts using stolen credentials.
- December 2022: DraftKings publicly acknowledges the security incident. The company confirms that hundreds of thousands of dollars were stolen from compromised accounts and announces its commitment to refunding affected users. This move, while necessary for customer trust, represented a significant financial outlay for the sports betting giant.
- Early 2023 (estimated): Law enforcement agencies, likely including the FBI and the U.S. Secret Service, initiate investigations into the DraftKings breach, identifying Austad, Garrison, and Stokes as key players.
- May 2023: Joseph Garrison, one of the primary hackers, is formally charged in connection with the scheme. This charge signals the advancement of the federal investigation.
- Sometime after May 2023 (estimated): Kamerin Stokes is arrested and subsequently pleads guilty to federal crimes related to his role in selling access to the compromised accounts. He is released on pretrial supervision pending his sentencing.
- Post-Guilty Plea: In a startling display of defiance, Stokes reopens his online "shop," continuing to sell access to compromised accounts for various retailers. He markets this renewed illicit activity with the provocative tagline "fraud is fun" and, when questioned, admits to relaunching the shop partly to generate funds for his attorney fees related to his ongoing prosecution.
- Subsequent Arrest: Due to his flagrant violation of pretrial release conditions, Stokes is re-arrested and remanded into federal custody.
- Recent Sentencing: Stokes is formally sentenced to 30 months in prison, followed by three years of supervised release, and ordered to pay substantial restitution and forfeiture.
DraftKings’ Response and the Broader Impact on Victims
Upon discovering the breach, DraftKings acted to mitigate the damage and restore customer trust. The company initiated a process to refund the hundreds of thousands of dollars stolen from affected accounts. This involved identifying accounts from which funds were withdrawn following the suspicious activity of adding and verifying new payment methods. While commendable, such incidents inevitably erode user confidence and necessitate enhanced security measures and public relations efforts to rebuild trust.

For the individual victims, the impact extended beyond financial loss. The theft of funds from their betting accounts could have ripple effects, including potential impacts on linked bank accounts or credit cards, identity theft concerns if other personal information was exposed, and the psychological stress of being targeted by cybercriminals. The process of disputing fraudulent charges, changing passwords, and monitoring financial statements adds a significant burden to those affected. The total amount stolen from users, $635,000, reflects direct monetary loss, but the intangible costs related to privacy and security breaches are often far greater.
Brazen Disregard: Stokes’ Post-Arrest Actions
Perhaps the most striking aspect of this case is Kamerin Stokes’ actions following his initial arrest and guilty plea. While awaiting sentencing, Stokes, as detailed by prosecutors, audaciously reopened his online marketplace for compromised accounts. This decision was not merely a lapse in judgment but a deliberate continuation of his criminal enterprise, openly promoted with the cynical tagline "fraud is fun." When confronted, Stokes admitted to having operated such "shops" for three years and justified his renewed activities by stating he needed money to pay his legal representation.
U.S. Attorney Jay Clayton highlighted this egregious behavior in a press release following the sentencing: "Kamerin Stokes victimized thousands of users of an online betting website through a cyberattack. After pleading guilty to federal crimes, Stokes audaciously reopened his criminal business, marketed using the tagline ‘fraud is fun,’ and said that he opened the new Shop in part because ‘gotta pay my attorneys,’ referring to his prosecution in this case." This defiance undoubtedly played a significant role in the court’s perception of his remorse and ultimately contributed to the severity of his sentence, including his re-arrest for violating pretrial release conditions.
The Legal Reckoning: Sentencing and Penalties
The sentence handed down to Kamerin Stokes – 30 months in prison, three years of supervised release, $1,327,061 in restitution, and $125,965.53 in forfeiture – reflects the serious nature of his crimes and the court’s commitment to punishing cybercriminals. The restitution order ensures that victims are compensated for their losses, while the forfeiture component aims to seize any assets or profits derived from the illegal activities. The supervised release period will impose strict conditions on Stokes’ activities post-incarceration, monitoring his digital footprint and preventing a return to cybercrime.
The prosecution of individuals like Stokes, Austad, and Garrison demonstrates the increasing focus of law enforcement on dismantling organized cybercrime networks, particularly those involved in financially motivated attacks. These cases often require sophisticated digital forensics and collaboration between various agencies to trace digital footprints across multiple platforms and jurisdictions.
Broader Implications for Cybersecurity and Online Safety
The DraftKings breach and Stokes’ conviction serve as a potent reminder of several critical cybersecurity challenges and responsibilities:
- For Users: The incident underscores the paramount importance of practicing robust cyber hygiene. This includes using strong, unique passwords for every online account, ideally generated and stored using a reputable password manager. Crucially, enabling multi-factor authentication (MFA) on all available services adds a vital layer of security, making it significantly harder for attackers to access accounts even if they possess stolen credentials. Users must also remain vigilant against phishing attempts, which are often used to harvest credentials.
- For Online Service Providers (like DraftKings, FanDuel, Chick-fil-A): Companies operating online platforms, especially those handling financial transactions or sensitive user data, must invest continuously in advanced security measures. This includes implementing robust credential stuffing detection and prevention mechanisms, employing sophisticated fraud detection algorithms, regularly auditing security protocols, and providing clear, actionable guidance to users on how to protect their accounts. The financial and reputational costs of a breach far outweigh the investment in proactive security. Proactive threat intelligence, monitoring for credential leaks on the dark web, and rapid incident response plans are essential.
- For Law Enforcement and the Justice System: The case highlights the ongoing battle against cybercrime and the need for specialized legal expertise to prosecute complex digital offenses. The ability to trace digital transactions, identify anonymous online actors, and collaborate across agencies is crucial in bringing such criminals to justice. The "fraud is fun" attitude displayed by Stokes also points to a mindset among some cybercriminals that necessitates firm legal responses to deter future offenses.
The sentencing of Kamerin Stokes is more than just the culmination of a single criminal case; it is a significant message from the justice system. It emphasizes that participating in the illicit trade of stolen digital access, even as a reseller, carries severe penalties, and that open defiance of legal processes will only compound those consequences. As the digital landscape continues to evolve, the fight against cybercrime remains a critical frontier for both individuals and institutions alike.

